Desktop Ransomware
The Desktop Ransomware is an encryption ransomware Trojan. The Desktop Ransomware's main targets seem to be individual, home computer users. The Desktop Ransomware, like most encryption ransomware Trojans, is mainly designed to keep the victim's files inaccessible and then demand a ransom payment from the victim. The Desktop Ransomware was first observed on November 1, 2018.
Table of Contents
How the Desktop Ransomware Attacks a Computer
The Desktop Ransomware uses a strong encryption algorithm to make the victim's files inaccessible. The Desktop Ransomware targets the user-generated files, which may include a wide variety of media files, databases and document types. The files that threats like the Desktop Ransomware target in these attacks may include:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
The Desktop Ransomware will mark the damaged files with the string 'Lock.' added as a prefix to the affected file's name. This is a departure from most encryption ransomware Trojan naming schemes, which add a new string to the end of the affected files' names as a new extension rather than to the beginning.
The Desktop Ransomware’s Ransom Demands
The Desktop Ransomware will change the infected computer's desktop background imageThe Desktop Ransomware will replace this image with a red skull over a black screen. This image will contain the following text:
The Desktop Ransomware displays a ransom note in the form of a program window that is titled 'Desktop Ransomware.' The Desktop Ransomware ransom note contains the following message:
'Welcome in
the Desktop Ransomware
Oooooops All your files on the desktop
are encrypted To decrypt files enter PIN
see you soon
Enter PIN
PIN = [TEXT BOX]
[Decryption|BUTTON]
[Get PIN|BUTTON]'
Clicking on the 'Get PIN' button leads computer users to a Facebook page that has been since removed. The PIN used by the Desktop Ransomware was recovered easily so that computer users can, fortunately, restore their data after a Desktop Ransomware attack.
Restoring Your Data from a Desktop Ransomware Attack
Computer users can restore their data by entering the following PIN code:
00114455220033669988554477++//
Since most of these threats are delivered in association with other malware and hoaxes, once the files have been restored, malware researchers strongly advise computer users to perform a full scan of their machines using a reliable, fully updated anti-malware program. It also is primordial to take precautions and have file backups since in most ransomware attacks it is not so simple to restore the files that have been compromised (and in most cases, the files may be lost permanently).
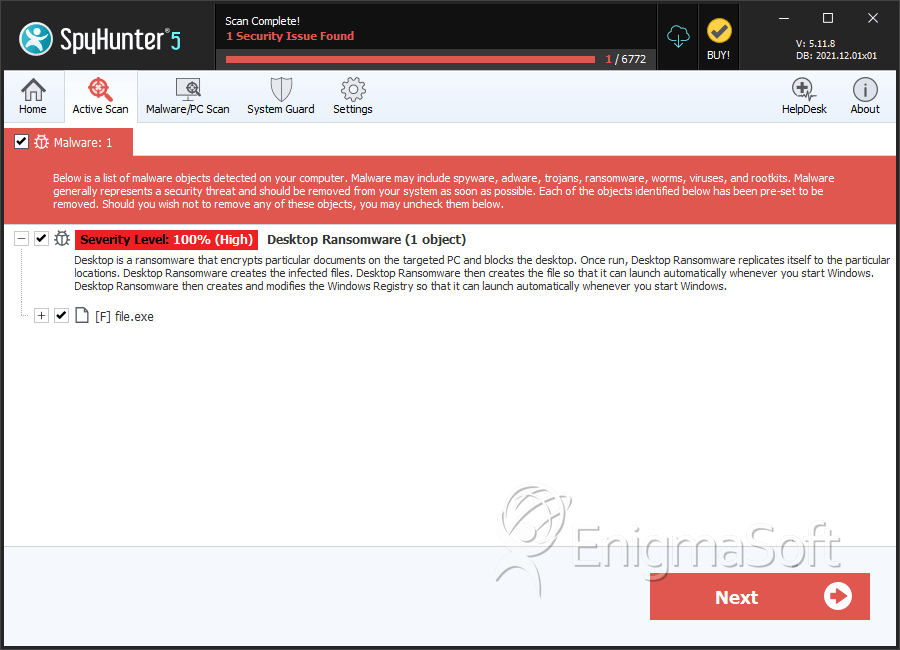
SpyHunter Detects & Remove Desktop Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | c013c2911340d6d29325254cf72d4e42 | 0 |

