Decoder Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 7,297 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 2,131 |
| First Seen: | November 2, 2017 |
| Last Seen: | September 17, 2023 |
| OS(es) Affected: | Windows |
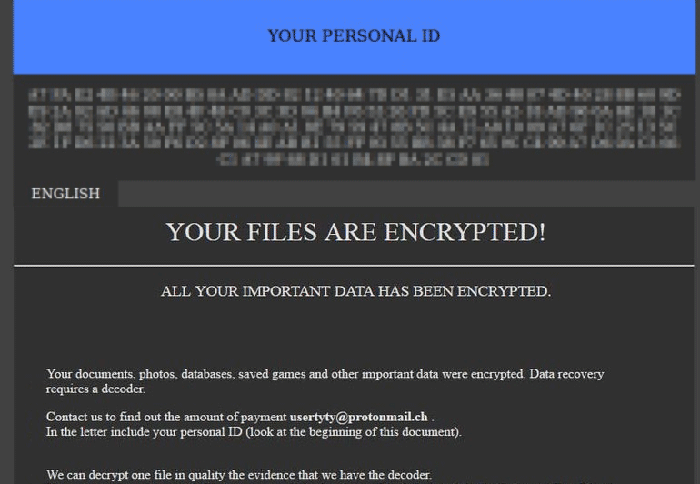
Decoder Ransomware Image
The Decoder Ransomware is an encryption ransomware Trojan that seems to be related to the Globe family of ransomware Trojans, which have been active at least since 2016. The Decoder Ransomware attacks were first observed in early November 2017. The Decoder Ransomware is designed to infect victims through spam email messages, which include corrupted file attachments with macro scripts that download and install the Decoder Ransomware onto the victim's computer. Learning to recognize these threats and handling these emails safely is essential in preventing threat attacks like the Decoder Ransomware.
Table of Contents
The Decoder that will Encode Your Files
Once the Decoder Ransomware is installed, it will carry out an encryption ransomware attack that is typical of these threats. Threats like the Decoder Ransomware encrypt the victim's files to make them inaccessible, to justify the demand of a ransom from the victims so that they will acquire the decryption key that makes it possible to restore the affected files. The Decoder Ransomware targets the user-generated files, which include media files, images, and commonly used document formats. Examples of the file extensions that threats like the Decoder Ransomware target in their attacks include:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks,.jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
The files encrypted by the Decoder Ransomware attack are marked with the file extension '.decoder,' which the Decoder Ransomware will add to the end of each affected file's name as part of its infection process. The Decoder Ransomware uses strong encryption algorithms that make it impossible to restore files encrypted by the Decoder Ransomware attack without the decryption key.
The size of the ransom demand is unknown at this time, but cyber criminals usually ask for sums between $500 and $1500 paid in Bitcoin or similar cryptocurrencies. Users are allowed to attach a number of encrypted files that total up to a megabyte in size, which is supposed to be restored as a 'gesture of good will' and proof the reversal of the encryption process is possible. Research shows that people behind these kinds of threats tend to ignore their victims, especially once payments have been submitted. Experience shows there is a high probability the victims will be scammed, robbed of their money and left hanging. Ignoring the ransom demands is the most sensible approach to the situation, as there is no guarantee the attackers will return any of the affected data to the state it was in.
Decoder shares similar traits with a number of other ransomware infections, such as Xorist, Crypto Tyrant, Losers, Bad Rabbit and more. Although these are threats developed by different people, they behave in the same manner. The main difference between these threats is the size of the ransom and the kind of encryption algorithm used, most often AES or RSA. Regular data backups are one of the best ways users can avoid this type of situation, as it would make the threat more of an annoyance.
The Decoder Ransomware’s Ransom Demands
The Decoder Ransomware will encrypt its victim's files and deliver its ransom note in the form of a text file named 'Instructions.txt,' which is dropped on the infected computer's desktop. The text of the Decoder Ransomware ransom note reads:
'Your personal ID
[RANDOM CHARACTERS]
All your files have been encrypted due to a security problem with your PC.
If you want to restore them, write us to the e-mail:decoder@keemail.me
Additional Mailing Address e-mail:decoder@expressmail.dk
How to obtain Bitcoins
** The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price.
** hxxps://localbitcoins.com/buy_bitcoins
** Also you can find other places to buy Bitcoins and beginners guide here:
** hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/
Free decryption as guarantee
** Before paying you can send to us up to 1 files for free decryption. Please note that files must NOT contain valuable information and their total size must be less than 1Mb
Attention!
** Do not rename encrypted files.
** Do not try to decrypt your data using third party software, it may cause permanent data loss.
** Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.'
Dealing with the Decoder Ransomware
PC security researchers advise computer users against contacting the email addresses mentioned in the Decoder Ransomware's ransom note or trying to negotiate with the criminals. Instead of paying the ransom amount, it is important to have file backups that allow computer users to restore the affected files by replacing the corrupted versions with a backup copy of the affected filed. File backups paired with a reliable security program that is fully up to date are the best protection against ransomware Trojans like the Decoder Ransomware.