Cyborg Ransomware
As a regular user, one of the worst threats that you can have infiltrating your system would be a data-encrypting Trojan. These nasty threats would sneak into your system, scan it, and begin locking your files. When the ransomware threat is done with encrypting your files, it will blackmail you into paying a ransom fee by promising that once you comply, the attackers will assist you in reversing the damage. There has been a brand-new file-locking Trojan spotted in the wild, and it has been given the name Cyborg Ransomware.
Propagation and Encryption
It has not been confirmed what distribution methods are used in the Cyborg Ransomware campaign. Threats of this class often are propagated via bogus application updates and fake pirated copies of legitimate software services. However, the most popular infection vectors when it comes to spreading ransomware threats are mass spam email campaigns. These fraudulent emails usually carry a corrupted attachment, which, once executed, will compromise the target's system. To induce the user to open the attachment, the attackers tend to use social engineering tricks that are woven into the message of the email. The Cyborg Ransomware will perform a brief scan and locate the files of interest. Most threats of this type tend to target a long list of file types, which are likely to be present on any user's computer. Then, the Cyborg Ransomware will begin its encryption process. Once a file is locked by the Cyborg Ransomware, you will notice that its name has been altered. This ransomware threat appends a '.petra' extension to it. For example, if you had named a file 'Celtic-eyes.jpeg,' its name will be changed to 'Celtic-eyes.jpeg.petra' after the file undergoes the encryption process of the Cyborg Ransomware.
The Ransom Note
When the encryption process is completed, the Cyborg Ransomware drops a ransom note and changes the background of the victim's desktop. The image's name is 'Cyborg_DECRYPT.jpg' and has a black background and blue text stating 'ALL YOUR FILES ARE ENCRYPTED BY CYBORG RANSOMWARE.' It also lets the users know that they can find more information in the ransom note the threat has dropped, which goes by the name 'Cyborg_DECRYPT.txt.' In the note, the attackers offer the user to decrypt one file free of charge, which aims to prove to the victim that the attackers are in possession of a functioning decryption key. As a ransom fee, the attackers demand to be sent $300 in the shape of Bitcoin. There is an email provided, where the victim can get in touch with the attackers for further information – 'petra-mail.ru.'
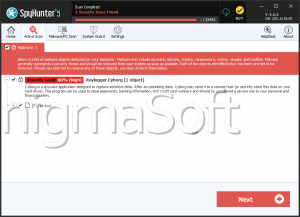
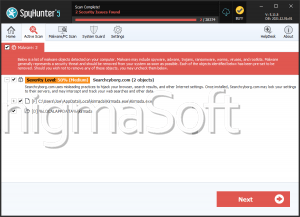
It is not advisable to cooperate with cybercriminals. Most authors of ransomware threats lose all interest in helping their victims once the monetary transaction has been completed. This is why you should consider obtaining a legitimate anti-spyware application precisely and use it to wipe off the Cyborg Ransomware from your system.