Cyberware Ransomware
Malware threats continue to grow in sophistication, and ransomware remains one of the most disruptive forms of attack facing individuals and organizations alike. A single infection can lock users out of critical data, interrupt operations, and cause financial and reputational damage. Understanding how modern ransomware works and how to defend against it is essential for reducing risk and limiting impact when attacks occur.
Table of Contents
Overview of the Cyberware Ransomware Threat
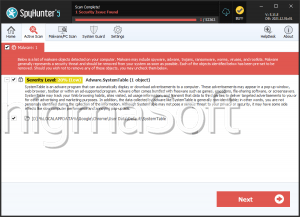
Cyberware is a recently identified ransomware strain uncovered during in-depth malware investigations by information security specialists. Once it successfully infiltrates a system, Cyberware immediately begins encrypting user files, rendering them inaccessible. Encrypted files are modified with the '.CYBER' extension, making the damage immediately visible, ordinary files such as images and documents are renamed from formats like '1.png' or '2.pdf' to '1.png.CYBER' and '2.pdf.CYBER.'
Beyond file encryption, Cyberware alters the desktop environment by changing the wallpaper, a psychological tactic designed to alert and pressure the victim. It also drops a ransom note titled 'CyberEvent-ReadMe.txt', which explains the attackers' demands and instructions.
Ransom Demand and Attacker Tactics
The ransom note claims that the victim's files were encrypted due to a security flaw in the operating system, attempting to shift blame onto the user's system hygiene. The attackers demand a payment of $430 in Bitcoin, directing the victim to send funds to a specific cryptocurrency address. After payment, the victim is instructed to email a copy of their so-called 'PCK' to 'cybersupport@protonmail.com', with the promise that a decryption tool will be delivered within 48 hours.
From a defensive standpoint, these promises should not be trusted. There is no technical or contractual obligation for the attackers to provide a working decryption utility, and many ransomware victims never regain access to their data despite paying. Worse still, an active ransomware infection may continue encrypting new files or propagate across shared drives and local networks if not promptly contained.
Consequences of Infection and Response Priorities
Once Cyberware completes its encryption routine, file recovery is generally impossible without either a clean backup or a legitimate decryption tool developed by security researchers. Paying the ransom does not improve recovery odds in a reliable way and can further incentivize criminal activity. For this reason, security professionals strongly advise against ransom payments.
An infected system should be isolated and cleaned as quickly as possible. Immediate removal of the ransomware helps prevent additional encryption activity and limits the risk of lateral spread to other devices on the same network.
How Cyberware Reaches Its Victims
Cyberware relies heavily on social engineering and poor security hygiene rather than advanced exploitation alone. Common infection vectors include fraudulent technical support scams, deceptive email attachments or links, and malicious advertising. Users are often tricked into opening weaponized documents, such as Word, Excel, or PDF files, or running disguised executables and scripts.
Additional delivery methods include peer-to-peer file-sharing platforms, third-party software installers, compromised or fake websites, and infected removable media like USB drives. Once executed, the ransomware silently initiates its encryption process in the background.
Best Security Practices to Defend Against Ransomware
Effective defense against threats like Cyberware depends on layered security and consistent user awareness. Keeping operating systems and applications fully patched closes vulnerabilities that ransomware often exploits. Reputable, up-to-date security software with real-time protection can detect and block malicious payloads before they execute. Equally important is maintaining regular offline or cloud-based backups that are not directly accessible from the primary system, ensuring data can be restored without negotiating with attackers.
User behavior also plays a critical role. Emails should be treated with caution, especially those urging immediate action or containing unexpected attachments. Software should only be downloaded from trusted sources, and the use of pirated or unofficial installers should be avoided entirely. Limiting user privileges, disabling macros by default, and monitoring network activity can further reduce the attack surface and improve early detection.
Final Thoughts
Cyberware ransomware exemplifies how modern malware combines technical damage with psychological pressure to coerce victims into paying. While its tactics are effective against unprepared systems, strong preventive measures and informed user practices significantly reduce the likelihood of successful infection. Vigilance, timely updates, and reliable backups remain the most powerful tools in defending against ransomware-driven extortion.