CryptoShield Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 167 |
| First Seen: | February 1, 2017 |
| Last Seen: | February 1, 2023 |
| OS(es) Affected: | Windows |
The CryptoShield Ransomware is a variant of a previously known ransomware Trojan known as CryptoMix (or CryptMix). The CryptoShield Ransomware is being distributed using exploit kits currently, specifically EITest and the RIG Exploit Kit. Currently, the CryptoShield Ransomware is being distributed on compromised websites. Con artists will infiltrate these websites and inject corrupted Java scripts that redirect computer users to attack websites that install the CryptoShield Ransomware and other threats on the victim's computer.
Table of Contents
A Shield that Works Against You
Since the exploit kits used to distribute the CryptoShield Ransomware leverage known vulnerabilities in the victims' software and operating system, it is essential to ensure that all of your software is up-to-date and all security updates and patches are applied. This is especially true for the Windows operating system, the Adobe software and Java. Once the CryptoShield Ransomware is downloaded onto the victim's computer, it will start encrypting the victim's files using a strong encryption algorithm, communicating with its Command and Control server to relay a unique key and encryption key for the victim's computer. The CryptoShield Ransomware will encrypt all files found on the victim's computer with file extensions matching the list below:
.ACCDB, .MDB, .MDF, .DBF, .VPD, .SDF, .SQLITEDB, .SQLITE3, .SQLITE, .SQL, .SDB, .DOC, .DOCX, .ODT, .XLS, .XLSX, .ODS, .PPT, .PPTX, .ODP, .PST, .DBX, .WAB, .TBK, .PPS, .PPSX, .PDF, .JPG, .TIF, .PUB, .ONE, .RTF, .CSV, .DOCM, .XLSM, .PPTM, .PPSM, .XLSB, .DOT, .DOTX, .DOTM, .XLT, .XLTX, .XLTM, .POT, .POTX, .POTM, .XPS, .WPS, .XLA, .XLAM, .ERBSQL, .SQLITE-SHM, .SQLITE-WAL, .LITESQL, .NDF, .OST, .PAB, .OAB, .CONTACT, .JNT, .MAPIMAIL, .MSG, .PRF, .RAR, .TXT, .XML, .ZIP, .1CD, .3DS, .3G2, .3GP, .7Z, .7ZIP, .AOI, .ASF, .ASP, .ASPX, .ASX, .AVI, .BAK, .CER, .CFG, .CLASS, .CONFIG, .CSS, .DDS, .DWG, .DXF, .FLF, .FLV, .HTML, .IDX, .JS, .KEY, .KWM, .LACCDB, .LDF, .LIT, .M3U, .MBX, .MD, .MID, .MLB, .MOV, .MP3, .MP4, .MPG, .OBJ, .PAGES, .PHP, .PSD, .PWM, .RM, .SAFE, .SAV, .SAVE, .SRT, .SWF, .THM, .VOB, .WAV, .WMA, .WMV, .3DM, .AAC, .AI, .ARW, .C, .CDR, .CLS, .CPI, .CPP, .CS, .DB3, .DRW, .DXB, .EPS, .FLA, .FLAC, .FXG, .JAVA, .M, .M4V, .MAX, .PCD, .PCT, .PL, .PPAM, .PS, .PSPIMAGE, .R3D, .RW2, .SLDM, .SLDX, .SVG, .TGA, .XLM, .XLR, .XLW, .ACT, .ADP, .AL, .BKP, .BLEND, .CDF, .CDX, .CGM, .CR2, .CRT, .DAC, .DCR, .DDD, .DESIGN, .DTD, .FDB, .FFF, .FPX, .H, .IIF, .INDD, .JPEG, .MOS, .ND, .NSD, .NSF, .NSG, .NSH, .ODC, .OIL, .PAS, .PAT, .PEF, .PFX, .PTX, .QBB, .QBM, .SAS7BDAT, .SAY, .ST4, .ST6, .STC, .SXC, .SXW, .TLG, .WAD, .XLK, .AIFF, .BIN, .BMP, .CMT, .DAT, .DIT, .EDB, .FLVV, .GIF, .GROUPS, .HDD, .HPP, .M2TS, .M4P, .MKV, .MPEG, .NVRAM, .OGG, .PDB, .PIF, .PNG, .QED, .QCOW, .QCOW2, .RVT, .ST7, .STM, .VBOX, .VDI, .VHD, .VHDX, .VMDK, .VMSD, .VMX, .VMXF, .3FR, .3PR, .AB4, .ACCDE, .ACCDR, .ACCDT, .ACH, .ACR, .ADB, .ADS, .AGDL, .AIT, .APJ, .ASM, .AWG, .BACK, .BACKUP, .BACKUPDB, .BANK, .BAY, .BDB, .BGT, .BIK, .BPW, .CDR3, .CDR4, .CDR5, .CDR6, .CDRW, .CE1, .CE2, .CIB, .CRAW, .CRW, .CSH, .CSL, .DB_JOURNAL, .DC2, .DCS, .DDOC, .DDRW, .DER, .DES, .DGC, .DJVU, .DNG, .DRF, .DXG, .EML, .ERF, .EXF, .FFD, .FH, .FHD, .GRAY, .GREY, .GRY, .HBK, .IBANK, .IBD, .IBZ, .IIQ, .INCPAS, .JPE, .KC2, .KDBX, .KDC, .KPDX, .LUA, .MDC, .MEF, .MFW, .MMW, .MNY, .MONEYWELL, .MRW, .MYD, .NDD, .NEF, .NK2, .NOP, .NRW, .NS2, .NS3, .NS4, .NWB, .NX2, .NXL, .NYF, .ODB, .ODF, .ODG, .ODM, .ORF, .OTG, .OTH, .OTP, .OTS, .OTT, .P12, .P7B, .P7C, .PDD, .MTS, .PLUS_MUHD, .PLC, .PSAFE3, .PY, .QBA, .QBR, .QBW, .QBX, .QBY, .RAF, .RAT, .RAW, .RDB, .RWL, .RWZ, .S3DB, .SD0, .SDA, .SR2, .SRF, .SRW, .ST5, .ST8, .STD, .STI, .STW, .STX, .SXD, .SXG, .SXI, .SXM, .TEX, .WALLET, .WB2, .WPD, .X11, .X3F, .XIS, .YCBCRA, .YUV, .MAB, .JSON, .MSF, .JAR, .CDB, .SRB, .ABD, .QTB, .CFN, .INFO, .INFO_, .FLB, .DEF, .ATB, .TBN, .TBB, .TLX, .PML, .PMO, .PNX, .PNC, .PMI, .PMM, .LCK, .PM!, .PMR, .USR, .PND, .PMJ, .PM, .LOCK, .SRS, .PBF, .OMG, .WMF, .SH, .WAR, .ASCX, .K2P, .APK, .ASSET, .BSA, .D3DBSP, .DAS, .FORGE, .IWI, .LBF, .LITEMOD, .LTX, .M4A, .RE4, .SLM, .TIFF, .UPK, .XXX, .MONEY, .CASH, .PRIVATE, .CRY, .VSD, .TAX, .GBR, .DGN, .STL, .GHO, .MA, .ACC, .DB.
The CryptoShield Ransomware uses the AES 256 encryption to encrypt the victim's files and then encrypts the file name using the ROT 13. The CryptoShield Ransomware identifies the encrypted files by adding the extension '.CryptoShield' to each affected file. While the file names can be decrypted relatively simply, the files themselves are not accessible without the decryption key, which the con artists hold in their possession.
The Ransom Note Displayed by the CryptoShield Ransomware
Wherever the CryptoShield Ransomware encrypts files, it creates ransom notes. These are named '# RESTORING FILES #.HTML' and '# RESTORING FILES #.TXT' and are opened with the victim's text editor and Web browser. Apart from the ransom notes, the CryptoShield Ransomware also will display fake error messages that contain numerous suspicious misspellings and odd syntax errors. These error messages are designed to trick computer users into allowing the CryptoShield Ransomware gain administrator access to the victim's computer. Below is the full text of the CryptoShield Ransomware ransom note:
'NOT YOUR LANGUAGE? USE http://translate.google.com
What happened to you files?
All of your files were encrypted by a strong encryption with RSA-2048 using the CryptoShield 1.0.
More information about the encryption keys using RSA-2048 can be found here: https://en.wikipedia.org/wiki/RSA_(cryptosystem)
How did this happen ?
Specially for your PC was generated personal RSA-2048 KEY, both public and private.
ALL your FILES were encrypted with the public key, which has been transferred to your computer via the Internet.
Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our secret server.
What do I do ?
So, there are two ways you can choose: wait for a miracle and get your price doubled, or start send email now for more specific instructions, and restore your data easy way.
If You have really valuable data, you better not waste your time, because there is no other way to get your files, except make a payment.
To receive your private software:
Contact us by email , send us an email your (personal identification) ID number and wait for further instructions.
Our specialist will contact you within 24 hours.
For you to be sure, that we can decrypt your files - you can send us a single encrypted file and we will send you back it in a decrypted form.
This will be your guarantee.
Please do not waste your time! You have 72 hours only! After that The Main Server will double your price!
So right now You have a chance to buy your individual private SoftWare with a low price!'
This is the text of the CryptoShield Ransomware fake error message (note the spelling error of 'momory' instead of 'memory'):
'explorer.exe - Application Error
The instruction at 0xe9c71f6c referenced memory at 0x46c8f91a. The momory could not be read.
Click on Yes in the next windows for restore work explorer.exe.
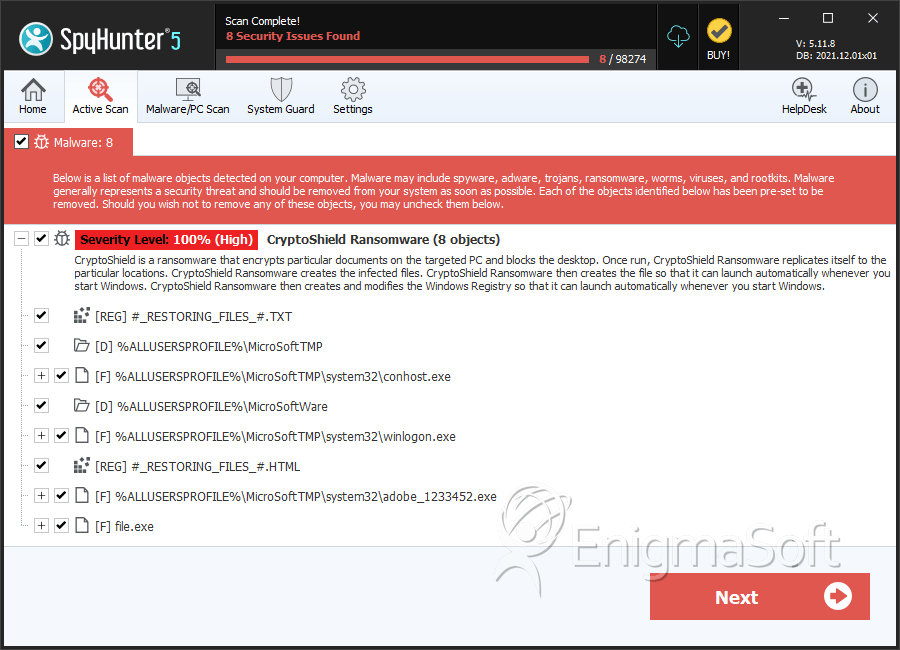
SpyHunter Detects & Remove CryptoShield Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | conhost.exe | dab3bc4a3cde46c6f2069786524a4f3e | 20 |
| 2. | adobe_1233452.exe | 00ff5b36cc6b09fabfd371f1f2091522 | 18 |
| 3. | winlogon.exe | c91bb73753c2ed68c1ee7a8c0ac006ac | 14 |
| 4. | conhost.exe | 97e9a421384905492f6675e10fd4d80f | 6 |
| 5. | conhost.exe | b4430540f3f8ba43db591332d8b41b50 | 5 |
| 6. | conhost.exe | 2d9c89f874fd2f341595046ad75efd01 | 4 |
| 7. | conhost.exe | 4527a86f7e1ad9328f091684618fc17d | 4 |
| 8. | conhost.exe | fdde3778c52f5a2d4de67ef8c049f856 | 4 |
| 9. | winlogon.exe | 2c613d71ba14be086195c9fd58a79fa9 | 3 |
| 10. | winlogon.exe | 297fa6182b74c19a7a894f0aa7437a01 | 3 |
| 11. | conhost.exe | e4d7596676b884563d9af2eef3642b1f | 3 |
| 12. | conhost.exe | 87ff17a6a8776dc211f8fe25e34a8120 | 3 |
| 13. | winlogon.exe | 9be2fea8003eef818fe399f537242fce | 3 |
| 14. | winlogon.exe | 5390a705d12f0befe460163341991e42 | 2 |
| 15. | winlogon.exe | 5ccd8fcc98b2e0fdac08ed01a381a66f | 2 |
| 16. | winlogon.exe | 83fd59daa3aae7f1fbfcdcb3a25104d8 | 2 |
| 17. | adobe_1233452.exe | 4e773fbd20d0bdd3fc6505e8ef19f621 | 2 |
| 18. | winlogon.exe | ab4fb0e72cd3d56967215acfa9712754 | 1 |
| 19. | conhost.exe | 71c906dad53d2cacc2640b2b4a11f609 | 1 |
| 20. | conhost.exe | 5f0179ce907ddb4492b7561ec2846c9c | 1 |
| 21. | adobe_1233452.exe | b4b6750d1bc64deb1aee0fa23ad56885 | 1 |
| 22. | file.exe | 2b110975ece5a5478f68aa1e98bed678 | 1 |
| 23. | file.exe | aa33bdac973488e3cee9e64c3c5b7158 | 1 |
| 24. | file.exe | e0d52cc8793592184a854fde5afaf152 | 1 |
Registry Details
Directories
CryptoShield Ransomware may create the following directory or directories:
| %ALLUSERSPROFILE%\MicroSoftTMP |
| %ALLUSERSPROFILE%\MicroSoftWare |