CryptoShield 2.0 Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 167 |
| First Seen: | February 1, 2017 |
| Last Seen: | February 1, 2023 |
| OS(es) Affected: | Windows |
The CryptoShield 2.0 Ransomware is a ransomware Trojan that is used to take advantage of inexperienced computer users. The CryptoShield 2.0 Ransomware is used to force computer users to pay large ransoms to recover their files, which are taken hostage by the CryptoShield 2.0 Ransomware infection. The CryptoShield 2.0 Ransomware presents a substantial threat, and computer users should take steps to protect their machines from threats like the CryptoShield 2.0 Ransomware and steps to limit the damage in case of a the CryptoShield 2.0 Ransomware infection.
Table of Contents
The CryptoShield 2.0 Ransomware can Cause Irreversible Harm to Your Files
The CryptoShield 2.0 Ransomware belongs to a large family of ransomware known as CryptoShield or Protected. Like other threats in this family, the CryptoShield 2.0 Ransomware encrypts the victim's data using a strong encryption algorithm. The CryptoShield 2.0 Ransomware then demands that the victim pays a large amount of money to recover the affected files. The CryptoShield 2.0 Ransomware will target numerous different file types, including media files and documents. The files that are encrypted using the CryptoShield 2.0 Ransomware will have the string '.[RES_SUP@INDIA.COM].ID[2D64A0776C78A9C3].CRYPTOSHIELD' added to the end of the file name.
The Operations Executed by the CryptoShield 2.0 Ransomwar
Apart from encrypting the victim's files, the CryptoShield 2.0 Ransomware will carry out the following operations on the victim's computer:
- The CryptoShield 2.0 Ransomware disables the Windows Recovery.
- The CryptoShield 2.0 Ransomware deletes all the Shadow Volume Copies to prevent this method of recovery.
- The CryptoShield 2.0 Ransomware makes changes to the infected computer to allow itself to persist on the victim's computer when it starts up.
- The CryptoShield 2.0 Ransomware is capable of deleting and manipulating other file processes.
The CryptoShield 2.0 Ransomware uses the AES encryption to make the victim's files inaccessible. After its attack, the CryptoShield 2.0 Ransomware will display the following ransom note on the victim's computer:
'NOT YOUR LANGUAGE? USE http://translate.google.com
What happens to you files?
All of your files were encrypted by a strong encryption with RSA-2048 using CryptoShield 2.0. DANGEROUS.
More information about the encryption keys using RSA-2048 can be found here: https://en.wikipedia.org/wiki/RSA_(cryptosystem)
How did this happen ?
Specially for your PC was generated personal RSA – 2048 KEY, both public and private. ALL your FILES were encrypted with the public key, which has been transferred to your computer via the Internet. Decrypting of your files is only possible with the help of the private key and decrypt program , which is on our secret server.
What do I do ?
So, there are two ways you can choose: wait for a miracle and get your price doubled, or start send email now for more specific instructions, and restore your data easy way. If You have really valuable data, you better not waste your time, because there is no other way to get your files, except make payment.
To receive your private software:
Contact us by email , send us an email your (personal identification) ID number and wait for further instructions. Our specialist will contact you within 24 hours.
ALL YOUR FILES ARE ENCRYPTED AND LOCKED, YOU CAN NOT DELETE THEM, MOVE OR DO SOMETHING WITH THEM. HURRY TO GET BACK ACCESS FILES. Please do not waste your time! You have 72 hours only! After that The Main Server will double your price!
So right now You have a chance to buy your individual private SoftWare with a low price!
CONTACTS E-MAILS:
res_sup@india.com – SUPPORT;
res_sup@computer4u.com – SUPPORT RESERVE FIRST;
res_reserve@india.com – SUPPORT RESERVE SECOND;
ID (PERSONAL IDENTIFICATION): 9694E***'
How the CryptoShield 2.0 Ransomware may Enter a Computer
In most cases, the CryptoShield 2.0 Ransomware is distributed in corrupted email attachments that use software exploits to download and execute corrupted code on the victim's computer. Apart from this method, the CryptoShield 2.0 Ransomware also may be distributed by hacking into a computer or by inserting corrupted scripts into compromised websites. Caution when handling email attachments and the use of a reliable security program that is fully up-to-date can help prevent these infections.
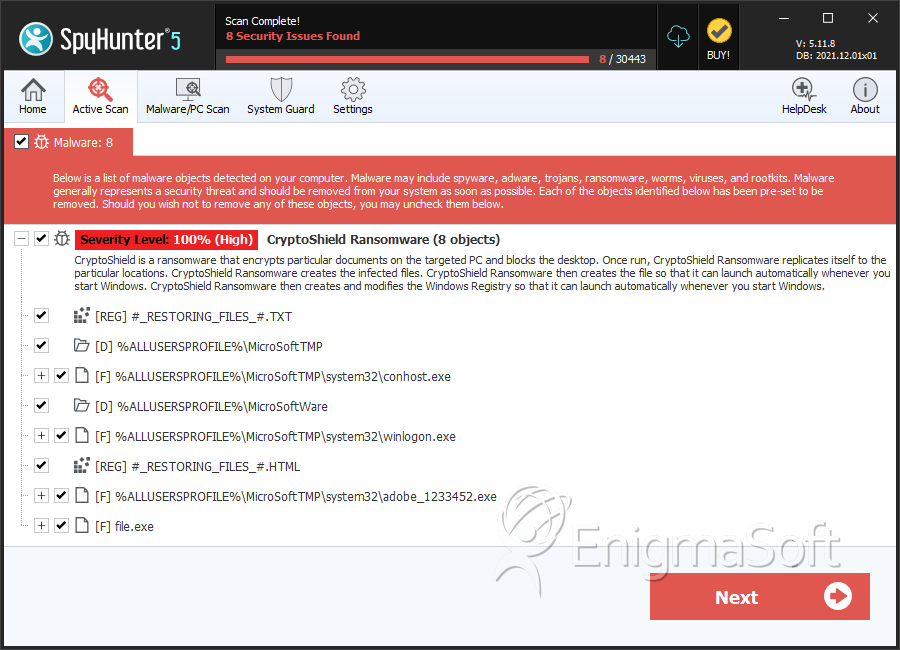
SpyHunter Detects & Remove CryptoShield 2.0 Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | conhost.exe | dab3bc4a3cde46c6f2069786524a4f3e | 20 |
| 2. | adobe_1233452.exe | 00ff5b36cc6b09fabfd371f1f2091522 | 18 |
| 3. | winlogon.exe | c91bb73753c2ed68c1ee7a8c0ac006ac | 14 |
| 4. | conhost.exe | 97e9a421384905492f6675e10fd4d80f | 6 |
| 5. | conhost.exe | b4430540f3f8ba43db591332d8b41b50 | 5 |
| 6. | conhost.exe | 2d9c89f874fd2f341595046ad75efd01 | 4 |
| 7. | conhost.exe | 4527a86f7e1ad9328f091684618fc17d | 4 |
| 8. | conhost.exe | fdde3778c52f5a2d4de67ef8c049f856 | 4 |
| 9. | winlogon.exe | 2c613d71ba14be086195c9fd58a79fa9 | 3 |
| 10. | winlogon.exe | 297fa6182b74c19a7a894f0aa7437a01 | 3 |
| 11. | conhost.exe | e4d7596676b884563d9af2eef3642b1f | 3 |
| 12. | conhost.exe | 87ff17a6a8776dc211f8fe25e34a8120 | 3 |
| 13. | winlogon.exe | 9be2fea8003eef818fe399f537242fce | 3 |
| 14. | winlogon.exe | 5390a705d12f0befe460163341991e42 | 2 |
| 15. | winlogon.exe | 5ccd8fcc98b2e0fdac08ed01a381a66f | 2 |
| 16. | winlogon.exe | 83fd59daa3aae7f1fbfcdcb3a25104d8 | 2 |
| 17. | adobe_1233452.exe | 4e773fbd20d0bdd3fc6505e8ef19f621 | 2 |
| 18. | winlogon.exe | ab4fb0e72cd3d56967215acfa9712754 | 1 |
| 19. | conhost.exe | 71c906dad53d2cacc2640b2b4a11f609 | 1 |
| 20. | conhost.exe | 5f0179ce907ddb4492b7561ec2846c9c | 1 |
| 21. | adobe_1233452.exe | b4b6750d1bc64deb1aee0fa23ad56885 | 1 |
| 22. | file.exe | 2b110975ece5a5478f68aa1e98bed678 | 1 |
| 23. | file.exe | aa33bdac973488e3cee9e64c3c5b7158 | 1 |
| 24. | file.exe | e0d52cc8793592184a854fde5afaf152 | 1 |
Registry Details
Directories
CryptoShield 2.0 Ransomware may create the following directory or directories:
| %ALLUSERSPROFILE%\MicroSoftTMP |
| %ALLUSERSPROFILE%\MicroSoftWare |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.