Core (Makop) Ransomware
The growing sophistication of cyber threats makes it fundamental for users to protect their devices from ransomware and other malicious programs. The Core (Makop) Ransomware is a prime example of how threat actors deploy advanced techniques to encrypt files and demand payment for decryption. Understanding how this threat operates and implementing strong security measures are critical to preventing data loss and system compromise.
Table of Contents
What is the Core (Makop) Ransomware?
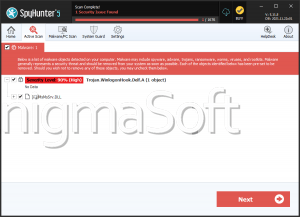
Cybersecurity researchers have identified the Core Ransomware as part of the Makop Ransomware family, a known group of file-encrypting threats. Once inside an infected system, this ransomware encrypts stored data and modifies file names by appending a unique victim ID, the attackers' email address, and the '.core' extension. For instance, a file initially named '1.png' could be altered to '1.png.[2AF20FA3].[corecrypt@hotmail.com].core,' making it inaccessible without the appropriate decryption key.
Upon completing the encryption process, the Core (Makop) Ransomware delivers a ransom note, typically saved in a text file named '+README-WARNING+.txt,' while also altering the desktop wallpaper. The message warns victims that their files have been encrypted and, in some cases, stolen. It discourages independent decryption attempts, claiming that such efforts could lead to permanent data loss.
Can Victims Retrieve Their Files?
Recovering files encrypted by ransomware is rarely feasible without the attackers' cooperation. Unless the ransomware is poorly designed or security experts find vulnerabilities in its encryption, the only known way to restore files is through backups. Even when victims meet ransom demands, there is no certainty that they will receive a functional decryption tool. In many cases, cybercriminals either disappear after receiving payment or demand additional sums. This is why cybersecurity experts strongly advise against paying ransoms, as doing so fuels further criminal activities.
Eliminating the Core (Makop) ransomware from an infected device is crucial to prevent further encryption, but removal does not restore affected files. Without pre-existing backups, recovery options remain limited.
How Does the Core (Makop) Ransomware Spread?
Ransomware infections often begin with deceptive tactics designed to trick users into executing malicious files. The Core (Makop) Ransomware spreads primarily through phishing emails, fake software downloads, compromised websites, and backdoor trojans. Attackers disguise ransomware as seemingly harmless files, such as software installers, media files or document attachments.
Some of the most common distribution methods include:
- Fraudulent email attachments or embedded links
- Drive-by downloads from infected websites
- Fake software updates that deliver ransomware instead of legitimate patches
- Pirated software and illegal activation tools that secretly install threats
- Exploiting weak remote desktop protocol (RDP) settings to gain unauthorized access
- Self-propagation through removable storage devices and local networks
Strengthening Your Defense against Ransomware
To minimize the risk of ransomware infections, users should implement strict cybersecurity practices. The following measures can significantly enhance a system's resilience against threats like Core (Makop) Ransomware:
- Maintain Secure Backups: Regularly create offline or cloud-based backups of essential data. This ensures that files remain accessible even in the event of encryption.
- Exercise Caution when receiving Emails. Avoid clicking on dubious links or opening unexpected attachments, especially if the senders are unknown.
- Use Robust Security Software: A reliable security solution can help uncover and block ransomware before it executes.
- Keep Software Updated: Regularly install updates for the operating system, applications, and security tools to patch vulnerabilities that cybercriminals may exploit.
- Disable Macros in Documents: Cybercriminals often use malicious macros in Microsoft Office documents to execute ransomware payloads. Disable macros unless they are absolutely necessary.
- Restrict Remote Access: If remote desktop services (RDP) are not essential, disable them or use vigorous passwords and multi-factor authentication to block unauthorized access.
- Download Software from Trusted Sources: Avoid using unofficial websites, torrents, or cracked software, as they may contain hidden threats.
- Be Wary of Unexpected Pop-ups and Advertisements: Some threats spread through malicious advertisements (malvertising), which redirect users to harmful sites or initiate drive-by downloads.
Ransomware threats like the Core (Makop) are a persistent danger, encrypting files and pressuring victims into paying for decryption. Since paying the ransom does not guarantee data recovery, maintaining backups and adopting proactive security measures is the best defense against these attacks. By staying informed and practicing good cybersecurity hygiene, users can minimize their possibilities and protect their valuable data from encryption-based threats.
Core (Makop) Ransomware Video
Tip: Turn your sound ON and watch the video in Full Screen mode.