CmbLabs Ransomware
Safeguarding personal and business data from cyber threats has never been more crucial. Ransomware attacks continue to evolve, targeting individuals and organizations with devastating consequences. One such sophisticated strain is the CmbLabs Ransomware, a newly identified threat designed to encrypt files and demand ransom payments. Understanding how this ransomware operates and implementing strong cybersecurity measures can help users defend against potential attacks.
Table of Contents
The CmbLabs Ransomware: A Threat that Encrypts and Extorts
Cybersecurity researchers recently identified the CmbLabs Ransomware, a strain designed to lock victims out of their data by encrypting files and demanding restoration payments. However, despite its misleading name, this ransomware is not connected to Consolidated Medical Bio-Analysis, Inc. (CMB Laboratory).
Once it infiltrates a system, the CmbLabs Ransomware appends the '.cmblabs' extension to encrypted files, making them inaccessible. For instance, a document named 'report.pdf' would be transformed into 'report.pdf.cmblabs,' rendering it useless without the corresponding decryption key.
Ransom Notes and the Attackers’ Demands
After encrypting files, the CmbLabs Ransomware delivers two ransom notes:
- DECRYPT_INFO.hta (an HTML application)
- DECRYPT_INFO.txt (a plain text file)
Both documents inform victims that their data has been encrypted and exfiltrated. While many ransomware operations threaten to leak stolen data if the ransom is not paid, the note left by the CmbLabs Ransomware does not explicitly make such threats.
The message also discourages victims from modifying encrypted files or using third-party decryption tools, warning that doing so could result in permanent data loss.
Data Theft and Potential Consequences
Although the ransom note does not include direct threats regarding data exposure, the CmbLabs Ransomware is believed to exfiltrate sensitive information before encrypting files. Collected data may include:
- Network credentials (local and remote login details)
- Financial records (budgets, annual reports, banking information)
- Personal data (employee and client information)
Cybercriminals often use stolen data as leverage, either to extort additional payments or to sell it on illicit markets. Even if the ransom is paid, attackers are not guaranteed to return the stolen files or refrain from misusing them.
The Ransom Payment Dilemma
Unfortunately, once a device is compromised, decrypting files without the cybercriminals' assistance is typically impossible. However, paying the ransom is highly discouraged for several reasons:
- No guarantee of data recovery – Attackers may not provide a decryption key, even after receiving payment.
- Encouraging future attacks – Paying ransoms fuels the ransomware industry, funding the development of more sophisticated threats.
- Potential legal risks – In some jurisdictions, making payments to certain cybercriminal groups could result in legal consequences.
Instead of paying, victims are encouraged to remove the ransomware from their systems and restore files from backups if available.
How the CmbLabs Ransomware Spreads
Like many modern ransomware threats, CmbLabs Ransomware employs multiple attack vectors to infiltrate systems. Some of the most common distribution methods include:
- Phishing Emails and Fraudulent Attachments – Fraudulent emails often carry infected attachments or links, leading to malware downloads.
- Compromised Software and Websites – Unofficial downloads, pirated software, and shady websites may harbor ransomware-laced files.
- Drive-By Downloads and Exploits – Cybercriminals may exploit software vulnerabilities to inject ransomware onto unpatched systems.
- Malvertising and Fake Updates – Deceptive ads and bogus software updates can serve as delivery mechanisms for ransomware infections.
- Network and USB Spreading – Some ransomware variants can propagate across networks and external storage devices.
Given the variety of infection tactics, users must remain alert and proactive in securing their digital environments.
Strengthening Your Defenses: Best Security Practices
To minimize the risk of ransomware infections like the CmbLabs Ransomware, users should implement robust cybersecurity measures and follow best practices:
- Regular Backups – Maintain offline and cloud backups of essential data to ensure recovery without relying on attackers.
- Up-to-Date Software – Keep operating systems, browsers, and security tools updated to patch known vulnerabilities.
- Email Caution – Avoid opening unexpected attachments or clicking on suspicious links, especially in emails from unknown senders.
- Strong Authentication – Use multi-factor authentication (MFA) for critical accounts to prevent unauthorized access.
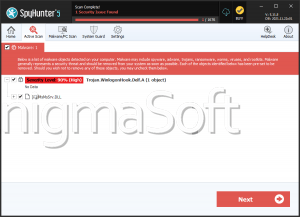
- Reputable Security Solutions – Employ advanced threat detection tools to identify and block unsafe files before they are executed.
- Network Segmentation – Isolate sensitive systems to minimize the spread of ransomware in case of an attack.
- Restrict Administrative Privileges – Limit user permissions to prevent ransomware from gaining complete control over a system.
- Avoid Pirated and Unverified Software – Download applications only from official sources to reduce exposure to malicious installers.
Final Thoughts
The CmbLabs Ransomware serves as yet another reminder of the growing sophistication of cyber threats. While ransomware infections can be devastating, proactive security measures and regular backups can significantly reduce the risks. Instead of relying on cybercriminals for file restoration, users should prioritize prevention, preparedness, and vigilance to keep their data safe.