Cloudnanoconnnection.info
Cloudnanoconnnection.info is a suspicious Web domain that on the surface may appear to be a brand new search provider. In fact, this site serves as an adware platform and is associated with browser hijackers. The threat is created with the intention of taking control of the most popular browsers such as Chrome, Mozilla and Internet Explorer. If you notice that your default homepage has been switched to Cloudnanoconnnection.info without your desire, this is a certain sign that the infiltration is present in your system. This adware changes a lot of the configuration settings, and the search results may be manipulated in order to lead to sponsored sites. You may witness redirects and a large quantity of advertisements, which slow down the performance of your browser and as a whole make using the Internet an unpleasant task.
How does the Browser Hijacker Reach Your PC?
Usually, the browser hijacker associated with Cloudnanoconnnection.info gets installed as an addition to another program. The process is called bundling and is a standard distribution method for Potentially Unwanted Programs (PUPs) that you otherwise may not even consider installing. Although the authors of this extension try to conceal its presence, a careful user will be able to detect the extra program he is about to download before it is too late. To do this, however, the user must choose the custom installation method and not the often recommended quick guide. It is best never to install anything unless you know what its purpose is. Regardless of the warnings in the installation wizard, if you are not aware of a certain program, just unmark it. In case you are in doubt if an application is helpful or potentially harmful, it is worth checking on-line for the impressions of other people. If you haven't downloaded anything recently but you still detect the browser hijacker connected to Cloudnanoconnnection.info, most likely you have followed a corrupt link or opened a contaminated e-mail attachment. As a rule, adware products have a complex distribution organization so that they can reach as many people as possible.
What is the Main Purpose of this Adware Platform and How does It Achieve It?
The ultimate goal of this browser hijacker is to generate traffic towards third-party sites. To accomplish it, the browser hijacker uses a few quite annoying methods. Each time when you start your browser or open a new tab, what you see will be the Cloudnanoconnnection.info search engine. Unlike the legitimate search providers, however, this suspicious site will not display the proper results corresponding to the information you need. Instead, Cloudnanoconnnection.info will manipulate them and show sponsored pages. With each transfer towards them, they will appear in a better position in Google or Bing even though they may be totally irrelevant. Some of these pages may be full advertisement sites and visiting them may just waste your time. Do not try to purchase anything from these sites because they may have threatening intentions. Some sponsored pages may attempt to install additional adware, Potentially Unwanted Programs or even harmful applications. The overall performance of your browser may be disrupted because there may be several advertisements in the form of banners or animations, which take time to load and unnecessarily seize a part of your system resources.
In order to adapt the advertisements towards your taste, the browser hijacker associated with Cloudnanoconnnection.info may monitor your on-line activity and gather the related information such as search history, cookies and even location. Unlike more severe threats, this adware doesn't need this data for harmful activities such as collecting your bank account credentials, but nevertheless you should keep this information to yourself.
What can be done to Eliminate the Infiltration?
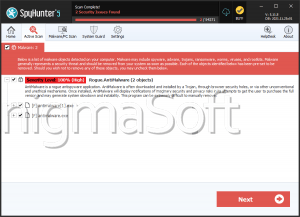
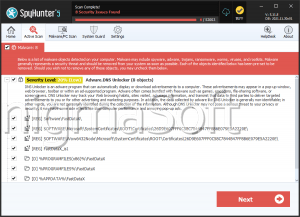
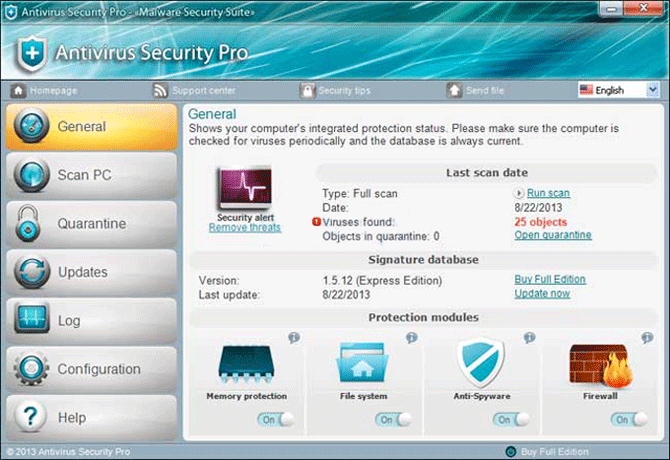
If you wish to restore your browser to its previous state and stop the constant redirects to irrelevant pages, you should remove the hijacker behind Cloudnanoconnnection.info as soon as possible. The untrustworthy extension can be found in the Control Panel and disabled from there. However, some traces of Cloudnanoconnnection.info may still be present in the system as Cloudnanoconnnection.info modifies many files. You can always count on an anti-malware application to conduct this tricky task for you and clean your system entirely from this infiltration. Moreover, after completing its work, the security software will remain and prevent various unreliable programs from being downloaded.
Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.