Blm Ransomware
The Blm Ransomware, as its name shows, is a ransomware threat that encrypts the files on any compromised computer with strong encryption algorithms and then extorts money from the affected users in exchange for the supposed restoration of the data. Although the Blm Ransomware is not wholly unique, its potency to cause damage shouldn't be underestimated as it belongs to the prolific Dharma family of ransomware threats.
Once it has found its way inside the targeted computer, the Blm Ransomware 'locks' the most popular filetypes and changes their names by following the pattern - [Original Filename].[Victim's ID].[Email of the hackers].[blm extension]. For example, a file with an original name of 'Picture1.png' will be renamed 'Picture1.[ID string].[blacklivesmatter@qq.com].blm' following its successful encryption. The criminals behind the Blm Ransomware leave instructions for their victims both in a text file named 'FILES ENCRYPTED.txt' and in a pop-up window.
The text file barely contains any details apart from the email that is provided for contact - blacklivesmatter@qq.com. The note displayed as a pop-up window, on the other hand, is significantly more detailed. It tells the Blm Ransomware victims that if they want to receive a supposed decryption tool, they will have to send a payment in Bitcoin. The exact amount of the ransom is not specified in the note, but the hackers clarify that the sum will depend on the time it takes the affected users to initiate contact. A single file no bigger than 1MB can be attached to the email to be decrypted for free.
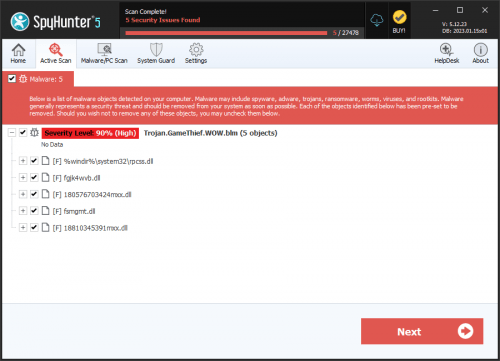
Handling the aftermath of a ransomware attack poses a significant challenge. One of the most important steps is to use a professional anti-malware program to clean the compromised computer to prevent any further encryption of files from taking place.
The text displayed in the pop-up window is:
'All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the email blacklivesmatter@qq.com
Write this ID in the title of your message -
In case of no answer in 24 hours write us to theese e-mails:blacklivesmatter@qq.com
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.'
The message found in the text files is:
'all your data has been locked us
You want to return?
Write email blacklivesmatter@qq.com.'
Table of Contents
How Did BLM Ransomware Get on My Computer?
It is currently unknown who is behind the BLM virus. The virus is likely to use the same infection vectors and attack methods as other Dharma ransomware. After looking through various reports from victims, the following attack strategies were uncovered;
Phishing Emails
Phishing emails are among the most common infection methods for ransomware and viruses in general. Hackers send hundreds of messages to random emails. The emails are designed to look legitimate but have compromised links and attachments. Users interact with the email and infect their computer in the process.
Payload Files Delivery
The code for the virus can be injected into other files. These files are downloaded from the internet by unsuspecting users. Macro-infected documents and spreadsheets are standard payload delivery methods. These documents are created to be compatible with Office and trick the users into activating macros (built-in scripts) to view the content on the file correctly. One such script installs the virus on the computer. Another alternative is to create infected program installers. These installers are executable files that install the virus code and can be disguised as freeware programs or software updates.
Internet Services and Websites
The installation file for BLM can be uploaded to different download portals and online communities, including chat rooms, forums, and social media. Hackers can also post links using fake and stolen accounts to make them seem more legitimate and trick users.
Outside of these infection methods, BLM ransomware uses many of the same techniques as other viruses – such as trojan installations.
What Does BLM Ransomware Do?
The virus gets to work as soon as it is installed. Like other viruses of this nature, the infection begins with information gathering. The local information gathering module scans apps installed on the computer and the hard drive for files to encrypt. It also gathers data on the hardware components of the computer. The information is seen by the hackers who can use it to learn more about their victim and assign them a unique ID.
BLM ransomware may have a security bypass component that lets it bypass antivirus and antimalware software on the computer. It can bypass intrusion detection systems, firewalls, antivirus programs, and more. The bypass features could be active or inactive depending on the nature of the infection.
Dharma family members are known to install other security threats on a target computer, delivering chain infections through trojan horse infections. These viruses make the host computer connect to a server to download other infection modules that give the hacker control over the system.
The main payload for BLM is the ransomware component. This component encrypts data on the host computer with a cipher. The virus uses a built-in list of file extensions to find files to encrypt. The processed files are appended with the ".BLM" file extension to make them inaccessible. Victims are blackmailed and told to pay a ransom to get the tools they need for decryption.
How to Protect Against Ransomware Attacks
One of the most important things you can do to protect against malicious programs is not to download and install software through unofficial websites and installers, third-party downloaders, and peer-to-peer networks such as torrent sites. You should always use official channels to get your software and avoid using pirated software. Illegal software is packed with "cracks" that activate the software. More often than not, these tools install malware instead of, or along with, activating the software. Programs and operating systems should be updated whenever possible, but make sure these updates come from official channels.
You should avoid interacting with website links and attachments in emails sent from suspicious and unknown addresses. There is the chance that these emails have been sent by cybercriminals to spread their malicious programs and catch you in a trap.
Last but not least, you should keep an antivirus program on your computer. Make sure this program is updated regularly with all the latest virus databases, detection, and removal methods. Be sure to run a virus scan regularly to detect infections like ViluciWare to keep your computer safe.