Banjo Ransomware
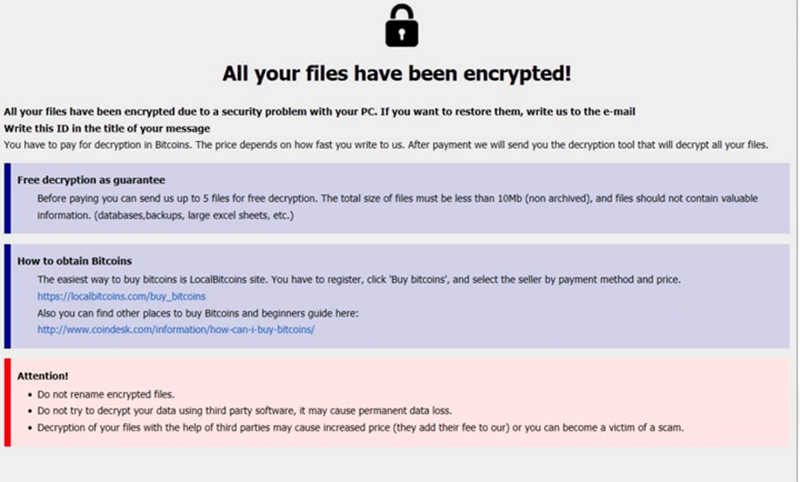
Banjo Ransomware Image
The Banjo Ransomware is one of the latest ransomware threats that have been spawned from the infamous Phobos malware family. As such, the Banjo Ransomware behaves as a standard Phobos Ransomware variant with very little deviation. It encrypts most file types found on the compromised computer and demands payment of a ransom in exchange for their potential restoration. Each encrypted file name will be modified according to the pattern - [Original Name].[Victim's ID].[Email of the hackers].[Ransomware Extension]. In Banjo's case, the email address is 'mutud@airmail.cc' while the file extension is '.banjo.' The threat leaves a ransom note in instructions for its victims both as text files named 'info.txt' and as a pop-up window.
The text files provide little information besides the three possible ways that victims can use to establish contact with the hackers. The first method is through the same email placed in the names of the encrypted files. If 24 hours pass and affected users do not receive an answer, they can turn to the secondary email address at 'krasume@tutanota.com.' Finally, victims also can chat with the criminals directly by contacting their Telegram account '@krasume.' The instructions displayed in the pop-up window provide a bit more details. It is specified that the ransom must be paid in Bitcoin, with the exact amount being dependent on how fast victims contact the hackers. The ransom note also states that up to 5 files that do not exceed 4MB in total size can be sent for free decryption.
The instructions found in the text files are:
'!!!All of your files are encrypted!!!
To decrypt them send email to this address: mutud@airmail.cc.
If we don't answer in 24h., send email to this address: krasume@tutanota.com
Our online operator is available in the messenger Telegram: @krasume'
The full text of the pop-up ransom note is:
'All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the email: mutud@airmail.cc
Write this ID in the title of your message -
In case of no answer in 24 hours write us to this e-mail:krasume@tutanota.com
Our online operator is available in the messenger Telegram: @krasume
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 5 files for free decryption. The total size of files must be less than 4Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.'

