BadRabbit Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 75 |
| First Seen: | October 25, 2017 |
| Last Seen: | November 29, 2023 |
| OS(es) Affected: | Windows |
The BadRabbit Ransomware is an encryption ransomware Trojan that seems to be related to Petya, a high-profile Trojan that received widespread attention after it carried out devastating attacks in Ukraine and other European counties. The BadRabbit Ransomware has been responsible for various attacks in Kiev, as well as numerous organizations in Turkey, Russia and Germany. Apparently, the use of the BadRabbit Ransomware was implemented through backdoor access to various websites, which may have been obtained through the use of corrupted WordPress plugins. Visitors to the websites would receive a pop-up notification that prompted the victim to install a fake Adobe Flash update (a typical way of delivering threats). The victim would receive the following notification:
'An update to Adobe Flash Player is available.
This update includes improvements in usability, online security and stability,
as well as new features which help content developers deliver rich and engaging experiences.
Did you know...
The top 10 Facebook
Most of the top
Flash Player
Note: If you have selected to allow Adobe install update, this update will be installed on your system automatically.
[REMIND LATER|BUTTON] [INSTALL|BUTTON]'
Table of Contents
How the BadRabbit Ransomware may be Installed
Regardless of the button clicked in the above message, a file named 'Uninstaller 27.0' is downloaded on the victim's computer. This will display a program window that looks like an updated for the Adobe Flash Player. However, this is just to hide the BadRabbit Ransomware's true attack, which involves connecting to its Command and Control servers and the download of a program named 'DiskCryptor,' which is used to encrypt the victim's files. The BadRabbit Ransomware uses the AES 256 encryption to encrypt the victim's drive, which makes the victim's files inaccessible. The BadRabbit Ransomware, apart from encrypting the victim's files, has an interesting ability that involves spreading through SMB connections, an ability observed in the WannaCry, which may have been a precursor of the BadRabbit Ransomware. The BadRabbit Ransomware uses rootkit-like functionality to infect the victim's computer at the highest level possible, encrypting the victim's entire drive. The BadRabbit Ransomware does not need Windows to remain functional to deliver its ransom note since the BadRabbit Ransomware changes the infected computer's BIOS message so that it displays the following text on the infected computer when it reboots:
'Oops? Your files have been encrypted.
If you see this text, your files are no longer accessible. You might have been looking for a way to recover your files. Don't waste your time. Ho one will be able to recover them without our 'ecryption service.
We guarantee that you can recover all your files safely. All you need to do is submit the payment and get the decryption password.
Visit our web service at caforssztxqzf2nm.onion
our personal installation key#1:
[358 RANDOM CHARCTERS]
If you have already got the password, please enter it below.
Password#1:_'
Dealing with a BadRabbit Ransomware Infection
The victim is expected to use a different computer and the TOR browser to pay a ransom of approximately 300 USD at the current exchange rate. However, agreeing to pay the ransom just allowing these crooks to continue developing and distributing the BadRabbit Ransomware. Unluckily, there is no way to restore the affected files without a decryption key that the crooks hold in their possession. If the BadRabbit Ransomware has infected your computer, it will be necessary to wipe the infected hard drive thoroughly and reinstall the Windows operating system. Because of this, the best protection against the BadRabbit Ransomware and similar threats is to have backup copies of your files. Backups allow you to recover from the BadRabbit Ransomware by restoring your files from the backup after wiping your hard drive completely. Computer users without backup copies of their data may not have any recourse to recover their files since payment is unlikely to yield positive results.
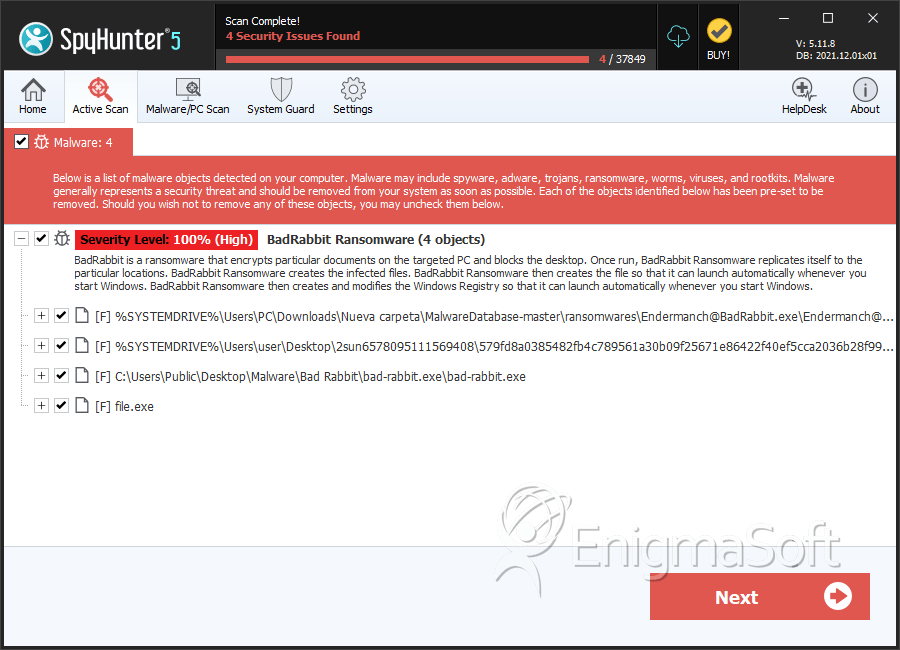
SpyHunter Detects & Remove BadRabbit Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Endermanch@BadRabbit.exe | fbbdc39af1139aebba4da004475e8839 | 37 |
| 2. | bad-rabbit.exe | b14d8faf7f0cbcfad051cefe5f39645f | 4 |
| 3. | 579fd8a0385482fb4c789561a30b09f25671e86422f40ef5cca2036b28f99648 | 1d724f95c61f1055f0d02c2154bbccd3 | 3 |
| 4. | file.exe | 7b5b089320d83de636b9befa84c47c3e | 0 |