Azor Ransomware
The Azor Ransomware is one of the newest spotted data-locking Trojans in the wild. There are numerous file-encrypting Trojans released each year, and malware researchers are struggling to combat them.
Table of Contents
Propagation and Encryption
There are various propagation methods that can be utilized in the distribution of ransomware threats. Many creators of data-encrypting Trojans, like the Azor Ransomware, opt to use spam emails as an infection vector. The con usually goes by a user receiving an email, which would contain either one of the two tricks below:
- A corrupted attachment such as a bogus document or spreadsheet.
- A misleading link to a corrupted file.
To convince the target to launch the attachment or download the corrupted file, the bogus email would contain a fraudulent message riddled with various social engineering tricks. Naturally, there are other commonly used propagation methods such as torrent trackers, fake application downloads and updates, malvertising, etc. Once the Azor Ransomware takes over your computer, it will begin encrypting all your files. It is likely that the Azor Ransomware is capable of encrypting a large amount of filetypes - .mp4, .mp3, .mov, .jpg, .jpeg, .gif, .png, .xls, .xlsx, .ppt, .pptx, .doc, .docx, .rar, .pdf, etc. To lock the targeted data, the Azor Ransomware would use an encryption algorithm. After encrypting a file, the Azor Ransomware appends a ‘.azor’ extension. For example, a file named ‘marble-plot.jpg’ will be renamed to ‘marble-plot.jpg.azor’ after the encryption process has been completed.
The Ransom Note
To inform the user of their demands, the attackers would make sure that a ransom note is dropped on the infected host. The ransom note that the Azor Ransomware drops is called ‘!read_me!.txt.’ In the note, the attackers make it clear that they demand to be contacted, and offer three options:
- Email – ‘azor2020@protonmail.ch’ and ‘azor@rape.lol.’
- Jabber – ‘azor2020@jxmpp.jp.’
- ICQ – ‘@azor2020.’
The ransom note – called “!read_me!.txt” explains to victims that they must write to the developers behind Azor. These developers can be reached at azor2020@protonmail.ch or at azor@rape.lol for more information. It is also possible to contact the attackers through Jabber and ICQ at azor2020@jxmp.jp and @azor2020 respectively.
Do you want to return your files?
Write to our email:
azor2020@protonmail.ch
azor@rape.lol
Or contact us via jabber
azor2020@jxmpp.jp
Jabber (Pidgin) client installation instructions,
you can find on youtube
https://www.youtube.com/results?search_query=pidgin+jabber+install
ICQ: @azor2020
!!!Any of your attempts to return files
will result in complete loss of the database!!!
tell your unique ID
For users who are not certain how to use Jabber, the authors of the Azor Ransomware have included instructions. It is likely that the victim would be informed about the ransom fee once they get in touch with the attackers.
The attackers will eventually get back to their victims and explain the important details such as the price of their decryption key and the cryptocurrency address they need to make the payment to. More often than not, it is impossible to decrypt files affected by ransomware without tools owned by the developers. Ransomware such as this use only the strongest encryption protocols to make data retrieval impossible.
The only way to safely recover lost data without paying the cybercriminals is by using a secure backup. Experts recommend against paying the ransom and trusting the cyber criminals as, more often than not, people get scammed. The attackers don’t send the decryption keys or tools after getting the payment. It’s worth noting that you should always remove the ransomware at the very least. Taking this step won’t restore your data, but it will prevent files from being encrypted again.
Unfortunately, there is currently no way to decrypt data encrypted by Azor without help from the attackers. It may be possible to do this in the future, however, should there be flaws in the program or if someone leaks decryption keys from the server. If you don’t have a data backup then, at the very least, you can consider copying your encrypted files to potentially decrypt them at a later date.
How Does Ransomware Get on Computers?
Ransomware has several potential infection vectors, just like any other kind of virus. The main techniques for spreading ransomware are spam campaigns, trojan viruses, and illegal activation tools. Other common methods are fake software updates and untrustworthy download pages and websites.
Spam campaigns involve sending thousands of scam emails to as many people as possible. The emails have an infectious file or link attached to them. Once someone interacts with the compromised attachment, their computer is infected. The malicious file could be a document, a PDF file, an archive, an executable file, or any other kind of file. The point is that they contain code that triggers an infection when the file is activated. Trojan viruses are a kind of malware used to trigger chain infections and download other malware, such as the Zorgo ransomware.
Software pirates use illegal activation tools – also known as "cracks" – to activate pirated software. These tools also download and install malicious programs and viruses. A fake software update works on a similar principle. Sometimes they exploit the flaws in an application and sometimes they just install a virus rather than the update they should.
It's possible for a person to unwittingly download malicious content through untrustworthy download resources like peer-to-peer networks, third-party websites, and unofficial free file-hosting websites.
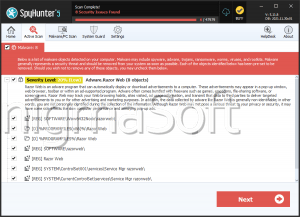
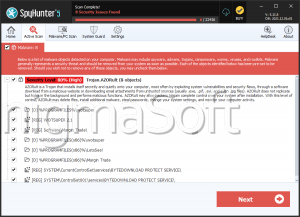
It is not advisable to bother with contacting or paying cybercriminals. These are untrustworthy individuals who will likely never provide you with the decryption key that you need to recover your data. It is best to remove the Azor Ransomware from your computer with the help of a genuine anti-malware application.