Aveo
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
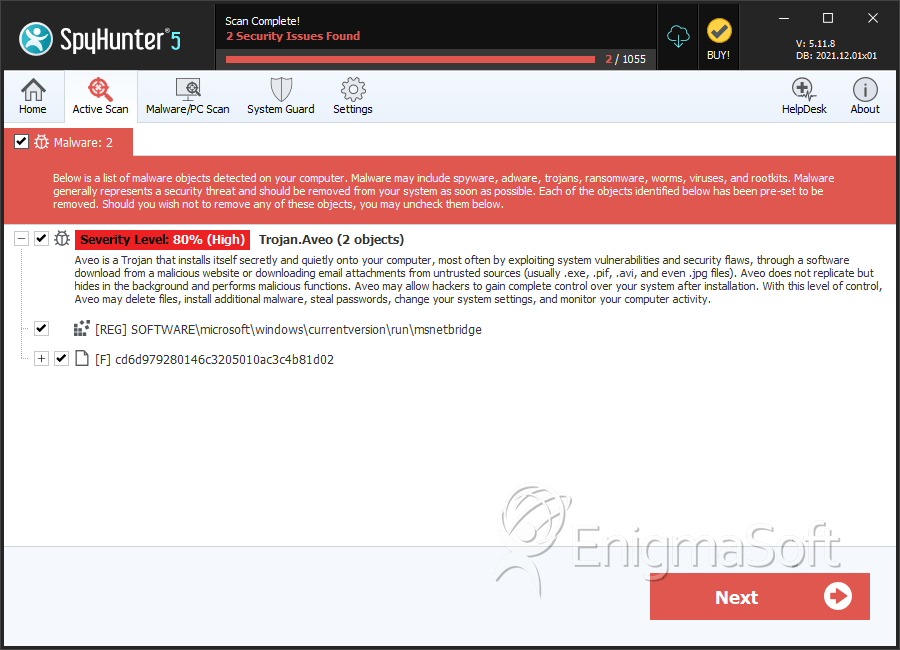
| Threat Level: | 80 % (High) |
| Infected Computers: | 71 |
| First Seen: | August 19, 2016 |
| Last Seen: | May 2, 2022 |
| OS(es) Affected: | Windows |
Aveo is a Trojan infection that is being used to target Japanese computer users. Aveo uses Command and Control servers located in the United States. Aveo seems to be related to FormerFirstRAT, a previously known threat. An Aveo distribution campaign currently being carried out in Japan has surfaced. Computer users are targeted with corrupted files that are used to install Aveo on their computers. The main distribution method associated with the latest Aveo distribution campaign is the use of spam email messages and fake documents, all using text in Japanese. PC security researchers have found links between Aveo and a family of threats known as FormerFirstRAT, which is also known by the name DragonOK. These were active in April of 2015 and were also used to carry out attacks against the Japanese public.
Table of Contents
Although not Possessing a High Degree of Complexity Aveo may be Very Harmful
Aveo's attack is simple, but may be quite harmful. Aveo is not particularly sophisticated. Aveo uses a self-extracting WinRAR file. This file will drop a decoy document, containing content in Japanese, the Aveo's executable, and a script designed to clean up after the attack and remove copies of Aveo (this may be done to prevent PC security analysts from obtaining Aveo easily and studying the attack). Aveo is being distributed through self-extracting binaries that use icons that make the file appear as a Microsoft Office Excel file. When the file is launched, Aveo is installed, but an Excel file is also loaded.
The main purpose of Aveo is to create a backdoor into the victim's computer. Aveo is also considered a RAT (Remote Access Trojan). These infections are used to gain access to the victims' computers, controlling them from a remote location. Aveo contacts its Command and Control server, located in the United States, and communicates through an unencrypted channel. Aveo will send a unique identifier for the victim, and collect the victim's IP address, the version of Microsoft Windows on the victim's computer, the username and other data. Aveo then receives commands that may include reading the victim's files, carrying out various types of tasks on the victim's computer, or granting remote access to the threat's developers. Threats like Aveo may be used for a variety of purposes such as collecting the victims' data or using the infected computer to carry out attacks on other targets.
Protecting Your Computer From Threats Like Aveo
Backdoor Trojans like Aveo can be devastating, especially because of their flexibility. Essentially, Aveo gives a remote user complete access to your computer. This can enable con artists to collect your banking information, spread threats to your email contacts, install other threats on your computer, delete your files and gather your data. Because of this, ensure that you are protected from these threats adequately using a reliable, fully updated security application. The following are some steps you can take to ensure that your computer is properly protected from Aveo and similar threats:
- Ensure that you exercise caution when browsing the Web and opening emailed content. Most threats, including Aveo, are distributed using corrupted links or files attached to spam email messages or delivered in other ways. Using caution when dealing with this kind of content can go a long way towards protecting you from Aveo and other threats.
- However, regardless of the amount of caution you exercise, it is still essential that your computer is protected with an anti-malware application. Therefore, it is crucial that you have adequate security software installed.
- Ensure that all of your software is fully up-to-date with the latest security patches.
SpyHunter Detects & Remove Aveo
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | cd6d979280146c3205010ac3c4b81d02 | cd6d979280146c3205010ac3c4b81d02 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.