Antivirus Studio 2010
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 6,538 |
| First Seen: | October 5, 2010 |
| Last Seen: | April 6, 2024 |
| OS(es) Affected: | Windows |
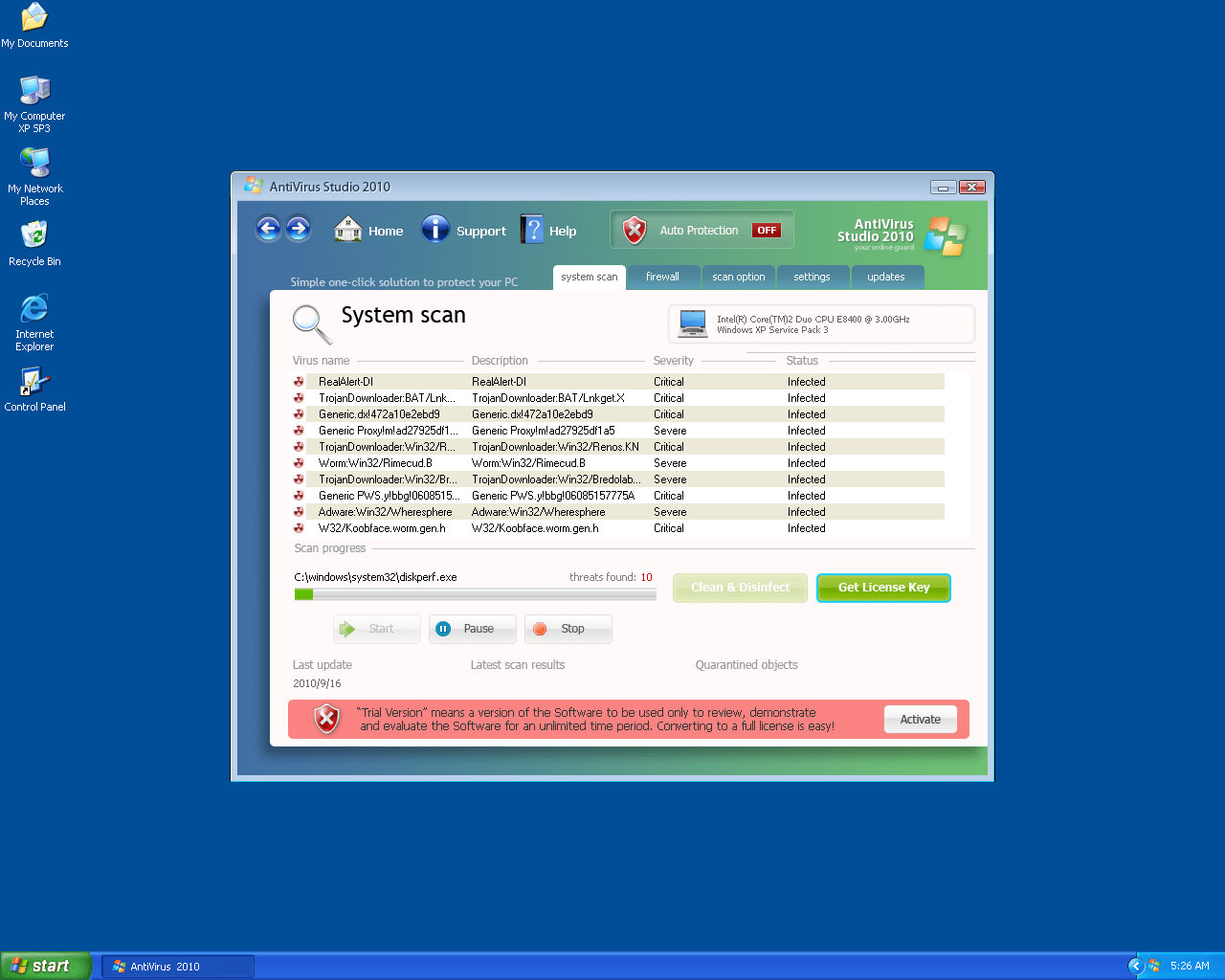
Antivirus Studio 2010 Image
Antivirus Studio 2010 aka AntivirusStudio2010 is a rogue security application that belongs to the UnVirex family and secretly spreads via Trojans. On infiltrating a system, AntivirusStudio2010 will simulate a fake system scan and display fake security alerts to convince a victim that his/her system is severely infected with dangerous malware. The victim will be coerced into purchasing the supposed "full version" of AntivirusStudio2010 to remove the detected malware. All security alerts and scan reports generated by Antivirus Studio 2010 are not to be trusted; instead users should have Antivirus Studio 2010 removed from their systems upon detection.
Among Antivirus Studio 2010 numerous clones are UnVirex, Desktop Security 2010, Securityinspector2010, Antivirus System 2011, Antivirus Antispyware 2011, Security Solution 2011, Antivirus Protection 2012.




Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Sophos | Sus/UnkPacker |
| McAfee | Generic PUP.l |
| AVG | Crypt.ADNR |
| Ikarus | Trojan-Downloader.Win32.Vundo |
| Ikarus | Trojan-Downloader.Win32.Mufanom |
| NOD32 | a variant of Win32/Cimag.DZ |
| DrWeb | Trojan.FakeAV.1267 |
| Symantec | SecurityEssentialFraud |
| NOD32 | a variant of Win32/Adware.FakeAntiSpy.P |
| AVG | Agent2.BSGW |
| AntiVir | TR/Hiloti.1.111 |
| Sunbelt | VirTool.Win32.Obfuscator.ah!e (v) |
| NOD32 | a variant of Win32/Kryptik.HZW |
| McAfee | FakeAlert-SecurityTool.q |
| Sunbelt | VirTool.Win32.Obfuscator.hg!a (v) |
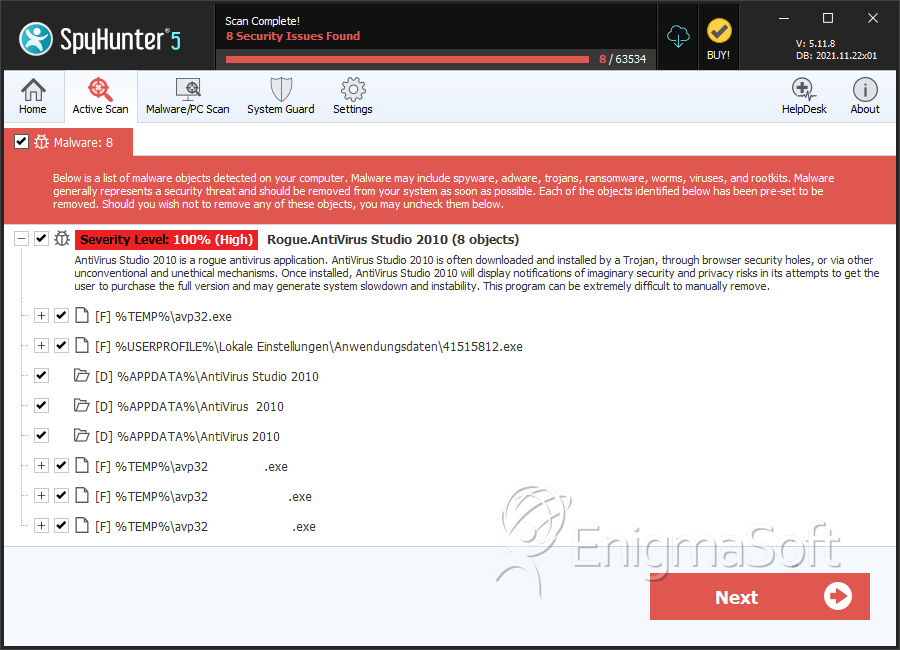
SpyHunter Detects & Remove Antivirus Studio 2010
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | avp32.exe | 5352ac17e2c8257838ab1afa4cbd2dda | 1 |
| 2. | avp32 .exe | f45158deb15e257fa757aab46143fa6c | 1 |
| 3. | avp32 .exe | 9ae069581b6efcd2b194ea99f54a272e | 1 |
| 4. | avp32 .exe | 0878cb5752553203ac15337b829231e9 | 1 |
| 5. | avp32 .exe | 124295ed1f28a6620ed0144aa96cdaad | 1 |
| 6. | avp32 .exe | 1da4d31943e859da43ccbd5376f292ff | 1 |
| 7. | avp32 .exe | 7d2dd180d32c76b85016a9cb311246f5 | 1 |
| 8. | avp32 .exe | 1d99b657ef901b46f9bed021004c04dc | 1 |
| 9. | avp32 .exe | 3b41eff136ec7d111b73a7026e867124 | 1 |
| 10. | avp32 .exe | 0ada4c640c5d71c02bba93422c0c03ba | 1 |
| 11. | avp32 .exe | 37ae5fb1f46c1b42f039146cf8bd3b5d | 1 |
| 12. | avp32 .exe | 94495ad4f83d846f4941a727ab68a341 | 1 |
| 13. | avp32 .exe | 87d0461aa9577fa2191f02d467c7a91a | 1 |
| 14. | avp32 .exe | 9bfccc717c394bb2ab03160dc9c96e28 | 1 |
| 15. | avp32 .exe | 8d0e9039f0353090272f6cfb5bf0bba2 | 1 |
| 16. | avp32 .exe | 7b1edd18c342a89b32bc2f6a52ea366d | 1 |
| 17. | avp32 .exe | d7840f76d184686a1767df1417793a8f | 1 |
| 18. | avp32 .exe | f8a695eb7d3e873d38a46050ad6a446e | 1 |
| 19. | avp32.exe | 46c309c6c6e822e375655ea446bf198c | 1 |
| 20. | avp32 .exe | 2db6194f05cc3b62fecf1684b39d6938 | 1 |
| 21. | avp32 .exe | 7b367bf8f65f044ac2b6473e33c5ace1 | 1 |
| 22. | avp32 .exe | 49fd7dc11577e56b8ff5e591689039c1 | 1 |
| 23. | avp32 .exe | 75b0f61b0c8682c179e725b83a4df404 | 1 |
| 24. | avp32 .exe | 4e04245ac18b064abc6af71bc0e9f287 | 1 |
| 25. | avp32 .exe | 5567698cf071d7dcb12a8c1e6bd0ae07 | 1 |
| 26. | avp32 .exe | 32305ccf65dc089a0dfd91701ae8a318 | 1 |
| 27. | avp32 .exe | b72101a349c9e1656ef07695de17771f | 1 |
Directories
Antivirus Studio 2010 may create the following directory or directories:
| %APPDATA%\AntiVirus 2010 |
| %APPDATA%\AntiVirus 2010 |
| %APPDATA%\AntiVirus Studio 2010 |
