AndroMut
AndroMut Image
A new downloader malware is being deployed by the hacker group "TA505." The malware, called "AndroMut" downloads a Remote Access Trojan (RAT) called "FlawedAmmyy." The campaign is deployed against banks and other commercial, financial services organizations in the United States, Singapore, the United Arab Emirates and South Korea currently. The name "AndroMut" comes from the similarities to a previously known malware called "Andromeda" and a "mutex" created by the malware called "mutshellmy777." Researchers do not believe the AndroMut malware is connected to the Andromeda malware necessarily. It also shares similarities with another downloader called "QtLoade."
What is the AndroMut Malware and Its Goals
AndroMut is a "downloader malware," meaning that its goal is to download a compromised tool or ransomware onto an infected device. It shares features with the Andromeda malware that came before it. The AndroMut malware was developed in June 2019 using the C++ code. It uses the AES-256 encryption, which hinders the ability of researchers to analyze it properly. It also uses advanced features to further avoid detection and analysis. These features include:
- Debugger detection.
- Memory clearance.
- Mac/Linux Wine Emulator detection.
- Sandbox detection.
- Mouse movement Detection.
How AndroMut Works
Like most malware, AndroMut's attack begins with spam email containing corrupted attachments or links that download an unsafe file. The email usually contains a ".html," ".htm," ".xls," ".doc" or similar attachment. The Web files usually contain a link to an MS Office document as well. Macros within the MS Office file run when the file is executed, running a "Msiexec" command to download AndroMut malware, or sometimes even FlawedAmmyy directly. Two campaigns have been detected so far. The first targeted bank employees in South Korea, while the second targeted the USA, Singapore, South Korea and the United Arab Emirates.
South Korea Sample:
Sender Name: 최성은
Subject: 송금증 $123.12
Attachment Names:
- 20.06.2019 송금증 123.12.doc
- 20.06.2019 송금증 123.12.xls
- 20.06.2019 송금증 123.12.htm
- 20.06.2019 송금증 123.12.html
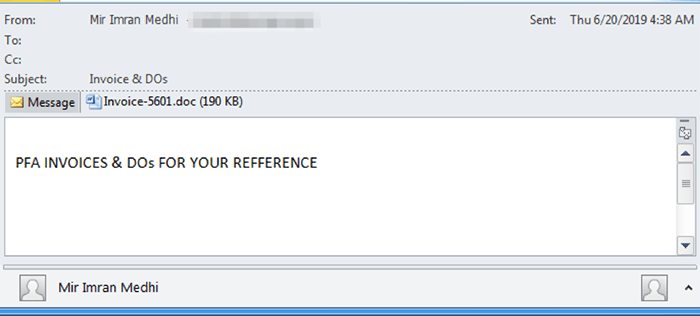
Other Countries:
Sender: Mir Imran Medhi
Subject: Invoice & DOs
Attachments Names:
- invoice-5601.doc
- invoice.xls?
The AndroMut malware, once downloaded, uses multiple anti-analysis features to detect whether it is in a "safe" sandboxed environment. It also checks for things like mouse movement, debuggers, and the Wine emulator, which some researchers use to run windows processes and programs on a Mac or other Linux based operating system.
The AndroMut malware then creates an LNK file and places it in the Recycle Bin. Depending on the current user's privileges, the AndroMut malware runs the newly created file using either a method called "Registry Run" (that depends on Registry Keys to execute a command without creating new processes), or schedules a task that will execute the file.
Configuration:
- Command and control host
- Command and control port
- Command and control URI
- Encryption key
- JSON key
Anti-analysis:
- Mouse movement detection
- Wine emulator detection using Registry Subkey "HKEY_CURRENT_USER\SOFTWARE\Wine"
- Debugger detection using debugging flags in NtGlobalFlag field from Process Environment Block
- Sandbox detection using process names:
- xenservice.exe
- VMSrvc.exe
- SbieSvc.exe
- cmdvirth.exe
- Memory zeroing

