AI-Driven PromptMink Malware Campaign
Cybersecurity researchers have uncovered malicious code hidden inside an npm package after a harmful dependency was introduced into a project through code co-authored by Anthropic's Claude Opus large language model (LLM). The discovery highlights how software supply-chain threats are evolving through the misuse of AI-assisted development workflows.
The package at the center of the campaign, '@validate-sdk/v2,' was presented on npm as a utility software development kit for hashing, validation, encoding and decoding, and secure random generation. In reality, it was designed to steal sensitive secrets from compromised systems. Investigators noted indicators suggesting the package may have been 'vibe-coded' using generative AI. It was first uploaded to npm in October 2025.
Table of Contents
PromptMink Linked to North Korean Threat Activity
Researchers have named the campaign PromptMink and believe it is connected to the North Korean threat actor Famous Chollima, also known as Shifty Corsair. This group has previously been associated with the long-running Contagious Interview operation and fraudulent IT Worker scams.
The campaign demonstrates a continued focus on the open-source ecosystem, especially environments tied to cryptocurrency and Web3 development.
AI-Coauthored Commit Introduced Dangerous Dependency
The malicious package was inserted through a February 28 commit to an autonomous trading agent repository. That commit was reportedly co-authored by Anthropic's Claude Opus model. Once included, the package enabled attackers to gain access to cryptocurrency wallets and steal funds.
The dependency chain moved through multiple packages. '@validate-sdk/v2' was listed inside '@solana-launchpad/sdk,' which was then used by a third package named openpaw-graveyard. This package was described as an autonomous AI agent capable of building a social on-chain identity on the Solana blockchain through the Tapestry Protocol, trading cryptocurrency through Bankr, and interacting with other agents on Moltbook.
A February 2026 source code commit added the tainted dependency, causing malicious code to execute and leak credentials that could expose wallet assets.
Layered Infection Strategy Designed to Avoid Detection
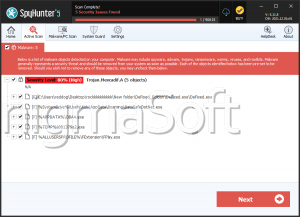
The attackers used a phased package structure. Initial packages appeared clean and contained no obvious malicious code. Instead, they imported secondary packages where the real harmful functionality was stored. If one malicious secondary package was detected or removed, it was quickly replaced.
Some first-layer packages identified in the campaign included:
@solana-launchpad/sdk
@meme-sdk/trade
@validate-ethereum-address/core
@solmasterv3/solana-metadata-sdk
@pumpfun-ipfs/sdk
@solana-ipfs/sdk
These packages claimed to provide cryptocurrency-related functions and included many trusted dependencies such as axios and bn.js, helping them appear legitimate. Hidden among those trusted libraries were smaller numbers of malicious dependencies.
Stealth Techniques Used by the Attackers
Threat actors used several methods to reduce suspicion and improve persistence:
- Creating malicious versions of functions already found in legitimate popular libraries
- Using typosquatting package names and descriptions that closely resembled trusted tools
- Splitting the malware into a harmless-looking loader and a second-stage payload
- Rapidly rotating, removed, or detected secondary packages
The first known package tied to the campaign, '@hash-validator/v2,' was uploaded in September 2025.
Expansion Beyond npm and Malware Evolution
Researchers noted signs of this activity months later, confirming the use of transitive dependencies to run malicious code on developer machines and steal valuable data. The campaign later expanded to the Python Package Index through a malicious package named scraper-npm, uploaded in February 2026 with similar functionality.
More recent versions of the operation reportedly established persistent remote access through SSH and used Rust-compiled payloads to steal entire source code projects and intellectual property from infected systems.
From Basic Stealer to Multi-Platform Threat
Early versions of the malware were obfuscated JavaScript stealers that recursively searched working directories for .env and .json files before preparing them for exfiltration to a Vercel-hosted domain previously linked to Famous Chollima activity.
Later versions embedded PromptMink as a Node.js single executable application. However, this increased payload size from roughly 5.1KB to nearly 85MB, making delivery less efficient. To overcome that limitation, attackers reportedly transitioned to NAPI-RS, allowing precompiled Node.js add-ons written in Rust.
Growing Risk to the Open-Source Supply Chain
The campaign's progression from a simple information stealer into a specialized multi-platform malware family targeting Windows, Linux, and macOS shows a significant escalation in capability. Its functions now include credential theft, SSH backdoor deployment, and theft of complete development projects.
Researchers concluded that Famous Chollima is combining AI-generated code with layered package-delivery methods to evade detection and manipulate automated coding assistants more effectively than human developers.