AeR Ransomware
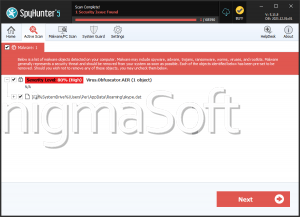
AeR is a threatening program strategically crafted to encrypt files on compromised devices, demanding ransom payments for their decryption. The discovery of AeR ransomware occurred during thorough analyses conducted by information security researchers while investigating potential malware threats.
Upon activation within the compromised devices, AeR initiates the encryption process, targeting a diverse array of file types and modifying their original filenames. The initial titles of files undergo a transformation, with the addition of a unique ID assigned to the victim, the email address belonging to the cybercriminals, and the '.AeR' extension. To illustrate, a file originally labeled as '1.doc' would be transformed into '1.doc.id-9ECFA74E.[aerossh@nerdmail.co].AeR.'
Following the encryption process, the AeR Ransomware generates two distinct ransom notes. Text files named 'info.txt' are strategically placed on the desktop and within affected directories. Simultaneously, a ransom-demanding message is prominently displayed in a pop-up window. It's noteworthy that the AeR Ransomware is classified as part of the Dharma family of malware threats, indicating its association with a specific lineage of threatening software.
The AeR Ransomware Takes the Files Hostage and Demands Ransom
The ransom notes generated by the AeR Ransomware are delivered in two different formats. While the text file named 'info.txt' essentially urges the victim to establish contact with the cybercriminals responsible for the attack, the accompanying pop-up window provides more detailed information about the situation. In the pop-up, the victim is informed that their files have undergone encryption.
The ransom message in the pop-up window includes assurances that data recovery is feasible. Still, it implies that the decryption process hinges on the payment of a ransom in Bitcoin cryptocurrency. Additionally, the victim is offered a limited opportunity to test the decryption process for up to three files, subject to specific criteria. The message concludes with explicit warnings regarding the consequences of non-compliance.
The AeR Ransomware is identified as part of the Dharma malware group, indicating its association with a specific lineage of malicious software. Programs within this group exhibit the capability to modify or encrypt both local and network-shared files. Notably, the Dharma Ransomware employs a strategy of terminating processes linked to open files, such as text file readers or database programs. This approach helps the ransomware evade exemptions from encryption that may occur due to the content being considered 'in use.'
Certain data is automatically excluded from the encryption process to prevent potential operational issues, such as system files, which, if encrypted, could render the device nonoperational. Additionally, files already locked by other ransomware are exempted from encryption based on a predetermined malware list. However, this mechanism is not flawless, as it does not encompass all possible ransomware-type programs, leaving potential vulnerabilities in the exclusion process.
The Dharma Ransomware Variants Establish Persistence Mechanisms
The Dharma software employs various techniques to ensure its persistence on compromised systems. One method involves copying the malware to the %LOCALAPPDATA% path and registering it with specific Run keys, enabling automatic execution upon each system restart. To further thwart recovery efforts, the ransomware takes the proactive step of deleting the Shadow Volume Copies.
In addition to these persistence measures, Dharma programs exhibit a level of sophistication by considering victims' geolocation. This functionality allows them to tailor their attacks, avoiding regions with economic challenges where home users may be less likely to afford ransom payments. The malware can also select targets based on geopolitical considerations.
Drawing on extensive analysis and research of numerous ransomware infections, it becomes evident that decryption without the involvement of the attackers is typically an insurmountable challenge. Even in cases where victims opt to pay the ransom, there is no guarantee of receiving the necessary decryption keys or software. As a result, it is strongly advised against succumbing to ransom demands, as such actions not only fail to ensure file recovery but also contribute to the perpetuation of illegal activities.
While the removal of the AeR Ransomware from the system is crucial to prevent further data encryption, it is essential to note that this process alone will not restore files already compromised. The primary solution lies in recovering files from a secure backup, assuming one is available. This underscores the importance of maintaining regular and reliable backup practices as an integral component of an effective cybersecurity strategy.
The ransom note AeR shows as a pop-up window is:
'All your files have been encrypted!
Don't worry, you can return all your files!
If you want to restore them, write to the mail: aerossh@cock.li YOUR ID -
If you have not answered by mail within 12 hours, write to us by another mail:aerossh@proton.meFree decryption as guarantee
Before paying you can send us up to 3 files for free decryption. The total size of files must be less than 3Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.The text files generated by the threat contain the following message:
You want to return?
write email aerossh@nerdmail.co or aerossh@cock.li or aerossh@proton.me'