Adventure Wallpaper Extension
After examining the Adventure Wallpaper Extension application, information security researchers have established that it functions as a browser extension designed to hijack browsers by altering crucial settings. Upon installation, the Adventure Wallpaper Extension forces users to visit a particular promoted website, thereby artificially increasing traffic towards it. It is strongly recommended to promptly uninstall and remove applications of this nature from affected browsers to mitigate potential risks and restore normal browser functionality.
The Adventure Wallpaper Extension Operates as an Intrusive Browser Hijacker
The Adventure Wallpaper Extension forcefully directs users to perform searches through adventurewallpaper.com by configuring it as the default search engine, homepage and new tab page of their browsers. Despite the outward appearance of adventurewallpaper.com as a functional search engine, it lacks the capability to produce search results independently. Instead, users attempting to conduct searches on a browser hijacked by the Adventure Wallpaper Extension are automatically redirected from adventurewallpaper.com to bing.com. It is crucial to recognize that deceptive search engines of this nature cannot be relied upon.
These counterfeit search engines often manipulate search rankings, present irrelevant or misleading content and divert users to untrustworthy websites. Additionally, such search engines, along with browser hijackers, may be crafted to harvest various data, including browsing history, geolocation data, and search queries.
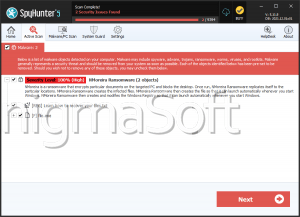
The potential misuse of collected data by the developers of browser hijackers and fake search engines poses substantial risks to user privacy, security, and overall online well-being. Therefore, if Adventure Wallpaper Extension is detected in a browser, it is highly recommended to promptly remove it to mitigate these potential risks and restore the browser to a secure and reliable state.
Always Pay Attention When Installing Applications from Unproven Sources
Browser hijackers and Potentially Unwanted Programs (PUPs) often employ various deceptive distribution methods to infiltrate users' devices unnoticed. These tactics are designed to exploit user vulnerabilities, lack of awareness, and trust. Here are common strategies used by these unwanted programs:
- Bundled Software: Browser hijackers and PUPs are frequently bundled with legitimate software during the installation process. Users may unintentionally install the unwanted program when installing another application if they do not carefully review the installation prompts or opt-out options.
- Deceptive Installers: Fraudulent actors create installers that mimic legitimate software updates, security patches, or essential system components. Users may be misled into downloading and installing browser hijackers or PUPs, thinking they are obtaining critical updates.
- Freeware and Shareware: Users often download free software or shareware from third-party websites. These sources may not adequately disclose the inclusion of additional software, allowing browser hijackers or PUPs to be installed alongside the desired program.
- Fake Updates: Some distribution methods involve presenting users with fake alerts indicating that their software needs an update. Clicking on these deceptive prompts can lead to the download and installation of unwanted programs instead of legitimate updates.
- Phishing Campaigns: Social engineering tactics are employed in phishing campaigns to trick users into clicking on malicious links or downloading infected files. Users may receive emails or messages posing as legitimate notifications, urging them to download a file that contains a browser hijacker or PUP.
- Malvertising: Rogue advertising involves placing deceptive ads on legitimate websites. Clicking on these advertisements may trigger the download and installation of unwanted programs, taking advantage of users' trust in the websites they visit.
- Fake Browser Extensions: Some browser hijackers disguise themselves as seemingly harmless browser extensions. Users may be enticed to install these extensions, believing they provide useful features, only to realize later that they have unwittingly introduced a browser hijacker or PUP.
To protect against these tactics, users should exercise caution when downloading and installing software, especially from unfamiliar sources. It's crucial to use reputable download platforms, read installation prompts thoroughly, keep software updated from official sources, and employ security software to detect and prevent the installation of browser hijackers and PUPs. Regularly reviewing installed programs and browser extensions can also help users identify and remove any unwanted software from their devices.