Zyklon Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
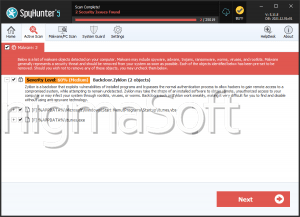
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 14,606 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 37 |
| First Seen: | May 23, 2016 |
| Last Seen: | July 25, 2023 |
| OS(es) Affected: | Windows |
A new ransomware Trojan called Zyklon Ransomware is attacking computer users. The most efficient method of deployment used by the Zyklon Ransomware is via spam emails containing a threatening attachment. However, file sharing networks, spam bots, social media spam, fake Java or Flash updates, etc. also may be infection vectors. The modus operandi of the Zyklon Ransomware is the same as most ransomware Trojans; the Zyklon Ransomware can make your files totally unemployable until you have the key to decrypt them by changing the files extensions to .zyklon. After infecting a computer, the Zyklon Ransomware will exhibit a ransom note in your desktop, explaining why you can't use your files and how to pay the demanded ransom to get your files back to normal. The Zyklon Ransomware uses the AES-512 cipher, which is a very strong encryption method and targets the following file types:
PNG .PSD .PSPIMAGE .TGA .THM .TIF .TIFF .YUV .AI .EPS .PS .SVG .INDD .PCT .PDF .XLR .XLS .XLSX .ACCDB .DB .DBF .MDB .PDB .SQL .APK .APP .BAT .CGI .COM .EXE .GADGET .JAR .PIF .WSF .DEM .GAM .NES .ROM .SAV CAD Files .DWG .DXF GIS Files .GPX .KML .KMZ .ASP .ASPX .CER .CFM .CSR .CSS .HTM .HTML .JS .JSP .PHP .RSS .XHTML. DOC .DOCX .LOG .MSG .ODT .PAGES .RTF .TEX .TXT .WPD .WPS .CSV .DAT .GED .KEY .KEYCHAIN .PPS .PPT .PPTX ..INI .PRF Encoded Files .HQX .MIM .UUE .7Z .CBR .DEB .GZ .PKG .RAR .RPM .SITX .TAR.GZ .ZIP .ZIPX .BIN .CUE .DMG .ISO .MDF .TOAST .VCD SDF .TAR .TAX2014 .TAX2015 .VCF .XML Audio Files .AIF .IFF .M3U .M4A .MID .MP3 .MPA .WAV .WMA Video Files .3G2 .3GP .ASF .AVI .FLV .M4V .MOV .MP4 .MPG .RM .SRT .SWF .VOB .WMV 3D .3DM .3DS .MAX .OBJ R.BMP .DDS .GIF .JPG ..CRX .PLUGIN .FNT .FON .OTF .TTF .CAB .CPL .CUR .DESKTHEMEPACK .DLL .DMP .DRV .ICNS .ICO .LNK .SYS .CFG.
The perpetrators of the Zyklon Ransomware ask for approximately 250 Euros to provide the decryption key that will make it possible to decrypt the compromised files. Security experts didn't find a decryption application for the files encrypted by the latest version of the Zyklon Ransomware yet. Therefore, the solution is to use backups (if you have it) from an external drive. However, before taking any steps to recover your files, you need to clean your computer and remove the Zyklon Ransomware with an appropriate threat removal tool.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.