Zoldon Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 5 |
| First Seen: | August 16, 2018 |
| Last Seen: | May 9, 2019 |
| OS(es) Affected: | Windows |
PC security researchers first observed the Zoldon Ransomware, an encryption ransomware Trojan, on August 9, 2018. The Zoldon Ransomware is an encryption ransomware Trojan that has some characteristics of another threat known as XMRig. The Zoldon Ransomware is also associated with a Bitcoin mining malware that also is installed onto the victim's computer. These mining Trojans will use up the system resources, causing a wide variety of problems.
Table of Contents
Why the Zoldon Ransomware Attacks a Compute
Most of the Zoldon Ransomware infection have come as a result of computer users installing a program named 'Bitcoin Miner Pro V3.1.exe,' which supposedly helps computer users improve their Bitcoin mining. However, the Zoldon Ransomware and a crypto-mining threat will be installed by this program onto the victim's computer. Once they are installed, the victim's files will be encrypted with the AES 256 encryption, making them inaccessible, and the Zoldon Ransomware's mining component will use the victim's computer to mine for Bitcoins. The following are the types of files that threats like the Zoldon Ransomware will encrypt certain files in these attacks, which include:
.ebd, .jbc, .pst, .ost, .tib, .tbk, .bak, .bac, .abk, .as4, .asd, .ashbak, .backup, .bck, .bdb, .bk1, .bkc, .bkf, .bkp, .boe, .bpa, .bpd, .bup, .cmb, .fbf, .fbw, .fh, .ful, .gho, .ipd, .nb7, .nba, .nbd, .nbf, .nbi, .nbu, .nco, .oeb, .old, .qic, .sn1, .sn2, .sna, .spi, .stg, .uci, .win, .xbk, .iso, .htm, .html, .mht, .p7, .p7c, .pem, .sgn, .sec, .cer, .csr, .djvu, .der, .stl, .crt, .p7b, .pfx, .fb, .fb2, .tif, .tiff, .pdf, .doc, .docx, .docm, .rtf, .xls, .xlsx, .xlsm, .ppt, .pptx, .ppsx, .txt, .cdr, .jpe, .jpg, .jpeg, .png, .bmp, .jiff, .jpf, .ply, .pov, .raw, .cf, .cfn, .tbn, .xcf, .xof, .key, .eml, .tbb, .dwf, .egg, .fc2, .fcz, .fg, .fp3, .pab, .oab, .psd, .psb, .pcx, .dwg, .dws, .dxe, .zip, .zipx, .7z, .rar, .rev, .afp, .bfa, .bpk, .bsk, .enc, .rzk, .rzx, .sef, .shy, .snk, .accdb, .ldf, .accdc, .adp, .dbc, .dbx, .dbf, .dbt, .dxl, .edb, .eql, .mdb, .mxl, .mdf, .sql, .sqlite, .sqlite3, .sqlitedb, .kdb, .kdbx, .1cd, .dt, .erf, .lgp, .md, .epf, .efb, .eis, .efn, .emd, .emr, .end, .eog, .erb, .ebn, .ebb, .prefab, .jif, .wor, .csv, .msg, .msf, .kwm, .pwm, .ai, .eps, .abd, .repx, .oxps, .dot.
The Zoldon Ransomware also delivers a ransom note in a program window named 'ZOLDON Crypter V3.0,' which contains the following message:
'Alert: Your computer and Files are encrypted By Zoldon Virus
$150 within 24 hours. $400 after 24 hours
Write this information down
How to remove the virus?
After the payment send to Bitcoin Address,
send email to [zoldon-staff@mail.ru] containing Your Machine ID
Once payment is received, you will get the decryption password
and simple instructions to restore all your files and computer to normal instantly
Without the decryption password, you will not get them back.
If we do not reach the amount within 72 hours
We will punish all the contents of your device on the Internet
IF YOU LOOSE THIS INFO, YOU WILL NOT BE ABLE TO CONTACT US
Start Time
[current date of infection]
Your Files will be lost on
[three days from the date of infection]
Bitcoin Address: [random characters]
Machine ID: [random number]
Password: [TEXT BOX] [Decrypt|BUTTON]'
Dealing with the Zoldon Ransomware Infection
Unfortunately, after their encryption, these files will be unrecoverable. Because of this, the best precaution against threats like the Zoldon Ransomware is to have file backups stored on detached hard drives and cloud storage networks with protected logins. This can allow computer users to recover their files by replacing them with backup copies. Apart from backup copies of your data, it is also important to have a strong security program that is fully up-to-date running on your computer. This can help intercept threats like the Zoldon Ransomware before they are installed. A reliable security application can also remove the Zoldon Ransomware, and its associated Bitcoin mining component can be eliminated by a solid anti-malware application.
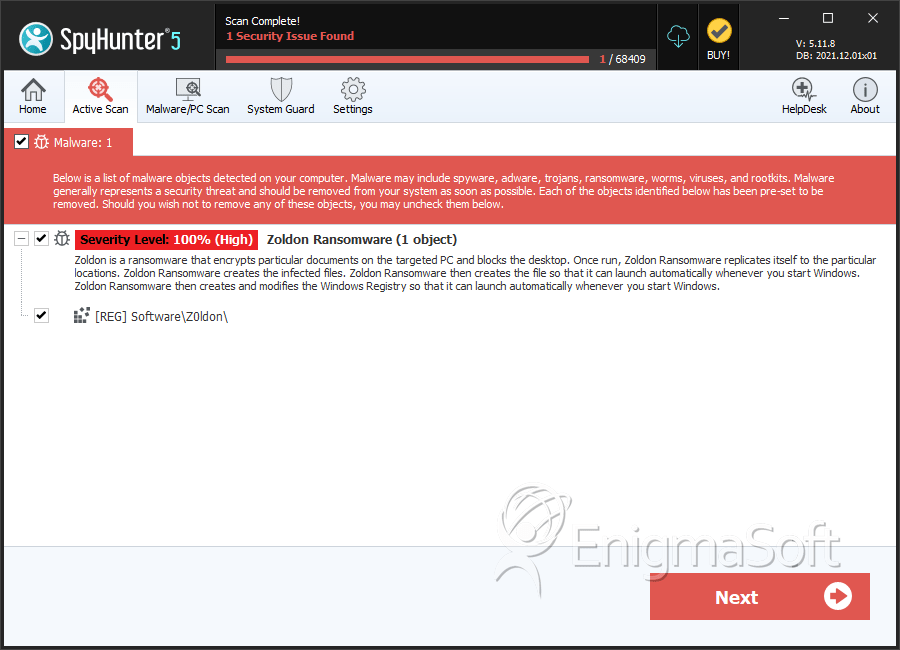
SpyHunter Detects & Remove Zoldon Ransomware