Zeta Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 194 |
| First Seen: | June 6, 2016 |
| Last Seen: | October 17, 2024 |
| OS(es) Affected: | Windows |
The Zeta Ransomware is a ransomware Trojan that is used to encrypt the victims' files so that they will pay a ransom to recover their files. The Zeta Ransomware adds the extension '.id_email_zeta@dr.com.scl' to every file it encrypts. The Zeta Ransomware also displays messages claiming that it is necessary to pay between 0.5 and 1.5 BitCoin ($225.18 – $675.53 at the time of writing) to decrypt the affected files. It is not viable to decrypt the files encrypted by the Zeta Ransomware currently. In most cases, the best solution for computer users is to remove the Zeta Ransomware infection itself with an anti-malware program that is fully up-to-date and then restore the affected files from a backup.
Table of Contents
How the Zeta Ransomware may Enter a Computer
The Zeta Ransomware may be delivered by corrupted email attachments or embedded links that lead to threatening websites.These email messages may contain fake information that is designed to trick inexperienced computer users into installing the Zeta Ransomware on their computers. Once the Zeta Ransomware has entered the victim's computer, it will attempt to encrypt data files on the victim's hard drives. The Zeta Ransomware may infect computers using the Windows operating system, ranging from Windows XP to Windows 10. Once the Zeta Ransomware is installed, it searches files with the following extensions:
.sql, .mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .dba, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt.
After encrypting the victim's files and changing their file extensions, the Zeta Ransomware will drop files named 'HELP_YOUR_FILES.txt' in each directory where the files were encrypted. This file is also dropped on the affected computer's desktop. The Windows desktop wallpaper is changed to 'HELP_YOUR_FILES.png,' which is a version of the Zeta Ransomware's ransom note in image form. The following is the Zeta Ransomware's ransom note, which contains information on how to pay the ransom and what has happened to the victim's computer:
NOT YOUR LANGUAGE? USE https://translate.google.com
What happened to your files?
All of your files were protected by a strong encryption with RSA-2048. More information about the encryption keys RSA-2048 can be found here: http://en.wikipedia.org/wiki/RSA_(cryptosystem)
How did this happen?
!!!Specially for your PC was generated personal RSA-2048 KEY, both public and private.
!!! ALL YOUR FILES were encrypted with the public key, which has been transferred to your computer via the Internet.
!!! Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our Secret Server.
What do I do?
So, there are two ways you can choose: wait for a miracle and get your pride doubled, or start obtaining BITCOIN NOW!, and restore your data easy way. If You have really valuable data, you better not waste your time, because there is no other way to get your files, except make a payment.
For more specific instructions:
Contact is by email only, send us an email along with your ID number and wait for further instructions. Our specialist will contact you within 12 hours. For you to be sure, that we can decrypt your files – you can send us a single encrypted file and we will send you back it in a decrypted form. This will be your guarantee.
E-MAIL1: pchelp_@_post.com
E-MAIL2: xerx_@_usa.com
YOUR_ID: (removed)
PC security analysts advise computer users to avoid paying the Zeta Ransomware ransom and instead ensure that all their files are adequately backed up. This way, they can recover from an attack by restoring any files from the backup copy.
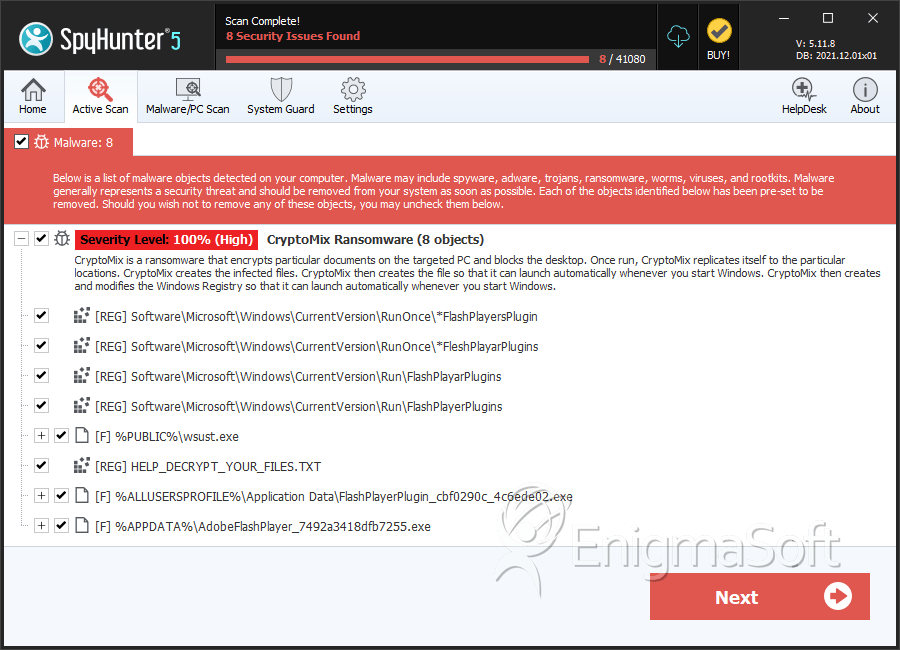
SpyHunter Detects & Remove Zeta Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | wsust.exe | 32b6f1ad13030cd9fe4d574377c41da6 | 30 |
| 2. | FlashPlayerPlugin_cbf0290c_4c6ede02.exe | f26be6279ec6092515d9dae51563660c | 16 |
| 3. | AdobeFlashPlayer_7492a3418dfb7255.exe | 0f43c5cf5f627ed0bc650fd61094d680 | 7 |
| 4. | AdobeFlashPlayer_94e30973ab4e2d2.exe | 818a0a4a3843f7eb7166a807a597898a | 5 |
| 5. | AdobeFlashPlayer_cc1414a71ab0ee.exe | a9e64c10bb40d127e7ae7d622eb47b8e | 4 |
| 6. | AdobeFlashPlayer_b8a94cdf1330f5.exe | ad66f350d86b140201fa0885f5d09fe0 | 4 |
| 7. | BC001B7832.exe | 7dca6ef84f0c99f34ca21fae124d4f1b | 4 |
| 8. | AdobeFlashPlayer_907b51565e5a75e5.exe | 8002bee84df90f2bd177bceb0ae604a9 | 3 |
| 9. | AdobeFlashPlayer_3207783b69ba0b7d.exe | 99f2ea85b58ed6b138a577d6782308a0 | 2 |
| 10. | AdobeFlashPlayer_70a333d85e797934.exe | 2728a5665ec6ae0b03321d0f4b2c8e2e | 2 |
| 11. | AdobeFlashPlayer_e82246b15d9a70f0.exe | 4ba02659f560b420d9f6dfe875e0e124 | 2 |
| 12. | FlashPlayerPlugin_cb8b2ee_681b245c.exe | ab352361300a6dbe645d332e838e5236 | 2 |
| 13. | AdobeFlashPlayer_502277412c7b42ee.exe | 1af6e689a041ab774233d5e620f78cc1 | 1 |
| 14. | AdobeFlashPlayer_b0619e261a7322d2.exe | 5bb7d85f7a5f1d2b01efabe5635e2992 | 1 |
| 15. | AdobeFlashPlayer_40942f642c280de6.exe | 7b2feb0796bb932d89437877d168de0d | 1 |
| 16. | AdobeFlashPlayer_8cd260f56cda739b.exe | 6b67d8d65b3f0c63dac45e246fb5f1d6 | 1 |
| 17. | AdobeFlashPlayer_7014f5a0fe9ca174.exe | 9cca586f1eee2bb729f5fc49421d5a8d | 1 |
| 18. | AdobeFlashPlayer_9c6c3b96dc3cb1eb.exe | 3ab3afb15dba15c7dd9391f4dc4d335b | 1 |
| 19. | FlashPlayerPlugin_9ddb30cf_c80c92f8.exe | 0995230b95584a48f405c25e3d370482 | 1 |
| 20. | cryptomix.exe | cacf78f42e19d6253351e97842d815da | 1 |
| 21. | file.exe | 0403db9fcb37bd8ceec0afd6c3754314 | 1 |
