Zegost
The malware continues to evolve, presenting new challenges for cybersecurity professionals and organizations worldwide. One such formidable adversary is the Zegost malware, a sophisticated information stealer that has gained notoriety for its stealthy tactics and potent capabilities. Zegost first emerged on the cybersecurity scene several years ago, showcasing a level of complexity and adaptability that sets it apart from traditional malware. Believed to be of Russian origin, Zegost has undergone several iterations, each more refined and elusive than its predecessor. The malware primarily targets Windows-based systems, exploiting vulnerabilities and employing a variety of tactics to infiltrate and compromise its targets.
Table of Contents
Zegost’s Functionality
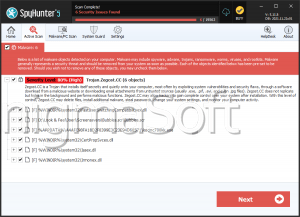
At its core, Zegost is categorized as an information stealer, designed to harvest sensitive data from infected systems surreptitiously. The malware achieves this by deploying various techniques, including keylogging, clipboard monitoring, and screen capturing. Zegost is also equipped with the ability to exfiltrate login credentials, financial information, and other personally identifiable information (PII) from compromised systems.
The Stealthy Tactics Used by Malware Stealers
What sets Zegost apart is its emphasis on remaining undetected for as long as possible. The malware employs advanced evasion techniques to bypass traditional security measures, including anti-malware software and intrusion detection systems. Zegost is known for its ability to camouflage itself within legitimate processes, making it exceptionally challenging to identify and mitigate.
The Propagation and Delivery of Zegost
Zegost typically spreads through phishing campaigns and corrupted attachments. Cybercriminals employ social engineering tactics to lure unsuspecting victims into opening infected documents or clicking on compromised links. Once executed, Zegost initiates its infiltration process, often remaining dormant to avoid immediate detection.
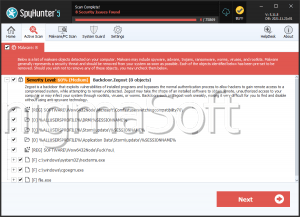
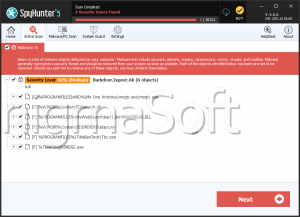
Zegost's persistent nature makes it a formidable threat to organizations. The malware is adept at establishing backdoors, allowing attackers to maintain control over compromised systems and ensuring longevity in their malicious activities. This persistence not only facilitates continuous data exfiltration but also enables Zegost to serve as a launchpad for additional cyber attacks.
Given the sophisticated nature of Zegost, organizations must adopt a multi-layered approach to cybersecurity. This includes implementing robust endpoint protection solutions, regularly updating and patching software, and conducting employee training to enhance awareness of phishing threats. Additionally, organizations should consider deploying advanced threat detection and response tools capable of identifying and mitigating evolving malware threats.