Zarok Ransomware
Ransomware threats lock users out of their files, disrupt business operations, and often lead to significant data loss. To stay safe, individuals and organizations must remain alert, adopt robust cybersecurity practices, and understand the tactics used by these malicious programs. One of the latest examples highlighting this ongoing threat is Zarok Ransomware, a sophisticated malware strain designed to encrypt data and extort its victims.
Table of Contents
Understanding the Zarok Ransomware Threat
Zarok Ransomware is a newly identified variant. Once executed, the malware begins encrypting data stored on the infected device. Each affected file is renamed with an additional four-character extension — for example, '1.jpg' becomes '1.jpg.ps8v' and '2.png' turns into '2.png.ps8v'. Alongside encryption, Zarok drops a ransom note titled 'README_NOW_ZAROK.txt' and alters the desktop wallpaper to display its demands.
The ransomware’s note informs victims that their files have been encrypted and instructs them to pay a ransom of approximately 200 EUR in Bitcoin. Victims are directed to send proof of payment to the attackers via Telegram (@stfuhq). The note claims that once payment is confirmed, a decryption tool will be provided, and stolen data will be deleted. However, the desktop wallpaper shows a different ransom demand — 500 EUR — suggesting that the attackers may attempt to pressure victims by using inconsistent payment instructions.
Data Encryption and Extortion Mechanics
Zarok operates according to the same fundamental principles as most ransomware campaigns. Once a device is compromised, the malware scans storage drives for valuable data and applies strong encryption algorithms to make the files inaccessible. Victims are then faced with a demand for payment in exchange for a decryption utility.
However, complying with the cybercriminals’ instructions is extremely risky. There is no guarantee that the attackers will deliver a working decryptor or honor their promise to delete stolen files. In many cases, victims who pay end up losing both their money and their data. The only reliable way to restore affected files without paying the ransom is by using safe, isolated backups or legitimate third-party decryption tools (if available).
Infection Vectors and Distribution Channels
Zarok Ransomware appears to spread through several deceptive techniques frequently exploited by threat actors. Common distribution vectors include infected executables, malicious documents, compressed archives, and scripts shared through fraudulent websites or phishing campaigns. Cybercriminals often disguise these files as legitimate downloads, fake updates, or cracked software to trick users into execution.
Other infection sources may include:
- Malicious advertisements, compromised websites, or fake online services.
- Spam and phishing emails with harmful links or attachments.
- Infected USB devices, peer-to-peer file-sharing networks, and third-party downloaders.
Once inside a system, the ransomware can deploy itself rapidly, encrypting data within minutes and, in some cases, attempting to spread across a local network.
Best Security Practices to Prevent Ransomware Attacks
Defending against ransomware requires proactive habits, layered protection, and consistent vigilance. Users should prioritize the following security measures to strengthen their defenses:
Core Preventive Steps:
- Keep your operating system, software, and security tools fully updated to close known vulnerabilities.
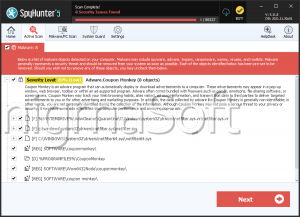
- Use reputable antivirus and anti-malware solutions capable of real-time detection and automatic scanning.
- Regularly back up critical data and store copies on offline or cloud-based storage systems that are not constantly connected to the device.
Safe Behavior and Online Hygiene:
- Avoid opening attachments or clicking links in unsolicited emails, especially those from unfamiliar senders.
- Refrain from downloading software from unverified sources, torrent sites, or cracked software repositories.
- Steer clear of suspicious advertisements, pop-ups, or browser notifications from unreliable websites.
- Disable macros in documents unless absolutely necessary and only enable them in trusted files.
The Importance of Prompt Removal
If Zarok Ransomware or any similar threat compromises a system, it should be removed immediately to prevent additional data loss or network propagation. Security researchers strongly advise against paying the ransom, as doing so supports criminal operations and rarely guarantees recovery. A thorough malware scan using trusted security software, followed by system restoration from clean backups, remains the safest recovery path.
Conclusion
Zarok Ransomware exemplifies how modern cyber threats continue to evolve with more refined extortion tactics and complex encryption mechanisms. Its ability to corrupt data, demand cryptocurrency payments, and exploit human trust underscores the importance of strong cybersecurity habits. Maintaining backups, staying alert to phishing attempts, and employing reliable security software are critical steps for ensuring that ransomware attacks like Zarok do not lead to irreversible damage.