'yoursalvations@protonmail.ch' Ransomware
The 'yoursalvations@protonmail.ch' Ransomware is an encryption ransomware Trojan that was released on November 22, 2018. The 'yoursalvations@protonmail.ch' Ransomware is similar to various other ransomware Trojans released previously in 2018, and it is likely to be part of a larger ransomware family. Like most threats of this type, the 'yoursalvations@protonmail.ch' Ransomware is designed to take the victim's files hostage, encrypting them and then demanding a ransom payment in exchange for the decryption key needed to recover them.
How the 'yoursalvations@protonmail.ch' Ransomware Attack Works
The 'yoursalvations@protonmail.ch' Ransomware uses the AES and RSA encryptions in its infection process, to make the victim's files inaccessible. The 'yoursalvations@protonmail.ch' Ransomware will target the user-generated files, which may include a wide variety of media files, databases, documents, and many other commonly used files. The 'yoursalvations@protonmail.ch' Ransomware appends a contact email address to the name of each affected file, and there have been several variants of the 'yoursalvations@protonmail.ch' Ransomware, which use different contact email addresses besides the 'yoursalvations@protonmail.ch.' The 'yoursalvations@protonmail.ch' Ransomware and similar encryption ransomware Trojans target certain file types in these attacks, which may include:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
The 'yoursalvations@protonmail.ch' Ransomware delivers a ransom note in the form of an HTML file named '!=How_recovery_files=!.html,' which is dropped on the infected computer's desktop. The 'yoursalvations@protonmail.ch' Ransomware's ransom note contains the text:
'All your important files are encrypted
Your files has been encrypted using RSA2048 algorithm with unique public-key stored on your PC. There is only one way to get your files back: contact with us, pay, and get decryptor software. We accept Bitcoin, and other cryptocurrencies, you can find exchangers on bestbitcoinexchange.io
You have unique idkey (in a yellow frame), write it in letter when contact with us. Also you can decrypt 1 file for test, its guarantee what we can decrypt your files.
IDKEY:
[TEXT BOX]
Contact information:
primary email: yoursalvations@protonmail.ch
reserve email: neverdies@tutanota.com'
Protecting Your Data from Threats Like the 'yoursalvations@protonmail.ch' Ransomware
The best protection against threats like the 'yoursalvations@protonmail.ch' Ransomware is to have backup copies of your data. This allows computer users to recover any data that was compromised by the attack without having to risk negotiating with the criminals that handle the 'yoursalvations@protonmail.ch' Ransomware. Unfortunately, there may not be a way to decrypt the data that has become compromised with the RSA and AES encryptions. Because of this, file backups are the best way to recover the data that has been compromised this way. Apart from file backups, a reliable, strong program can prevent the 'yoursalvations@protonmail.ch' Ransomware attacks and remove this threat in the case of an infection.
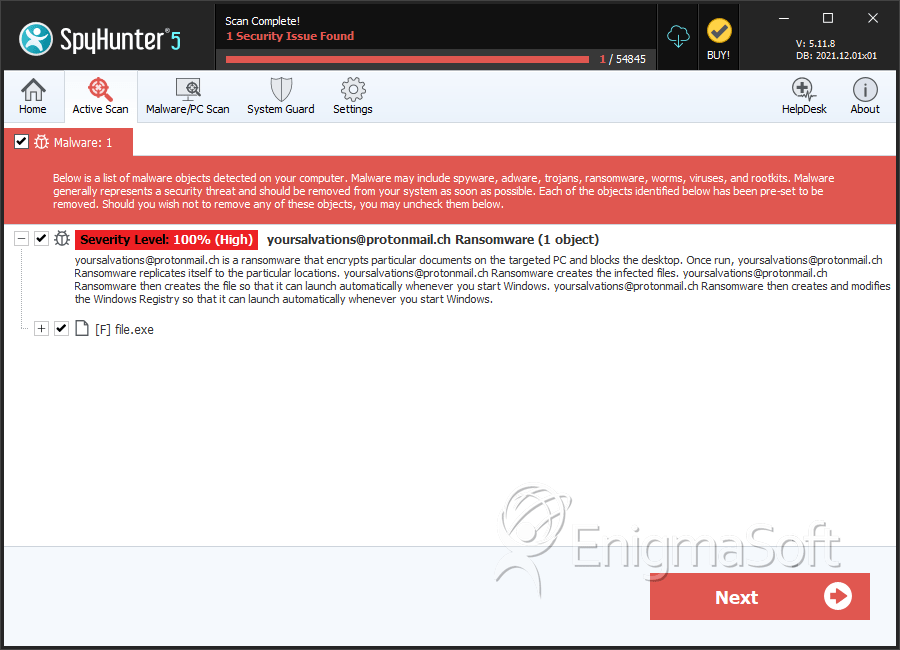
SpyHunter Detects & Remove 'yoursalvations@protonmail.ch' Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 75795c8ef2b35b12e73305c32b010e84 | 0 |

