YouAreFucked Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 11 |
| First Seen: | February 22, 2017 |
| Last Seen: | September 11, 2021 |
| OS(es) Affected: | Windows |
The YouAreFucked Ransomware is a ransomware Trojan that encrypts the victims' files, essentially taking them hostage and preventing computer users from accessing their data. The YouAreFucked Ransomware then demands the payment of a ransom from the victims. The YouAreFucked Ransomware receives its name because of a hex code 'YouAreFucked' that is embedded in the file header of each encrypted file. The YouAreFucked Ransomware represents a real threat to servers and businesses since it tends to target high-profile victims like corporate networks and Web servers. PC security analysts have observed that the YouAreFucked Ransomware is being distributed using phishing email messages meant to trick computer users into downloading and opening a corrupted file. These corrupted files will use corrupted macros to download and install the YouAreFucked Ransomware on the victim's computer. Disabling macros on common applications like the Microsoft Word will protect computer users from these exploits.
Table of Contents
How the YouAreFucked Ransomware Attack Works
The YouAreFucked Ransomware is designed to encrypt numerous file types, targeting media files, common document formats, databases, and other types of files, without preventing Windows from functioning (since it needs the operating system to remain functional to display its ransom note and demand payment from the victim). During its attack, the YouAreFucked Ransomware will scan the infected computer and make a list of the potential files to be encrypted. Once the YouAreFucked Ransomware has listed these files, it will encrypt the affected files with a strong encryption algorithm. Unlike many other ransomware Trojans, it will not identify the files that are encrypted by changing their extension. Rather, the YouAreFucked Ransomware will alter the file headers. After the YouAreFucked Ransomware has finished encrypting the victim's files, it will display a message alerting the victim of the attack and demanding the payment of a ransom.
The Information Contained in the YouAreFucked Ransomware’s Ransom Note is Accurate
The YouAreFucked Ransomware displays the following message on the victim's computer, demanding the payment of a ransom:
'!!! IMPORTANT INFORMATION !!!!
All of your files are encrypted with RSA-2048 and AES-128 ciphers. More information about the RSA and AES can be found here:
[LINKS TO ARTICLES ON WIKIPEDIA]
Decrypting of your files is only possible with the private key and decrypt program. secret server. To receive your private key follow one of the links:
[LINKS TO PAGES ON THE TOR NETWORK]'
Unfortunately, the contents of the above message are accurate in that it is not possible to recover the files affected by the YouAreFucked Ransomware without having access to the decryption key or program. However, computer users should refrain from paying the YouAreFucked Ransomware ransom. It is not uncommon for con artists to ignore the ransom payment or ask for more money from the victims of attacks like the YouAreFucked Ransomware.
Dealing with a YouAreFucked Ransomware Infection
If your files have become inaccessible because of an attack by the YouAreFucked Ransomware or a similar threat, PC security researchers strongly advise you to refrain from paying the ransom. Since the files affected by the YouAreFucked Ransomware cannot be recovered without the decryption key, it is compulsory to take preventive measures to stop the YouAreFucked Ransomware and similar ransomware Trojans. Computer users are advised to use a reliable security application that is fully up to date to protect their computers. Most importantly, it is imperative to have file backups of all files on the cloud or external memory devices. If computer users can recover the affected files from a backup, then the people responsible for the YouAreFucked Ransomware attack lose any leverage they have over the victim that allows them to demand a ransom payment. File backups are the single most effective measure to stop ransomware Trojans like the YouAreFucked Ransomware and limit the damage of an attack involving one of these threats. Since the YouAreFucked Ransomware may be distributed using corrupted email attachments, caution when dealing with this content also is essential.
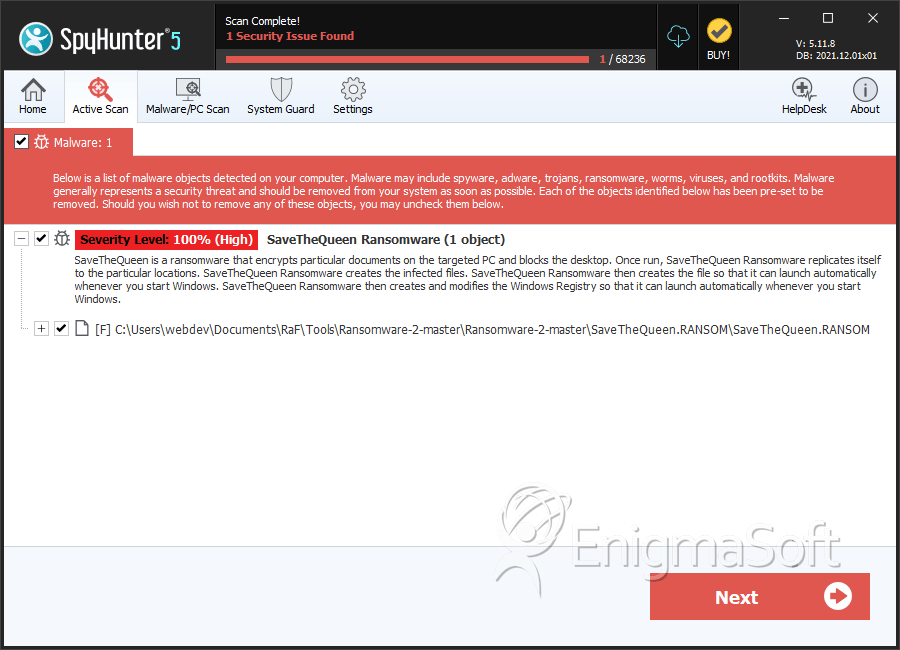
SpyHunter Detects & Remove YouAreFucked Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | SaveTheQueen.RANSOM | 8775ed26068788279726e08ff9665aab | 5 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.