XRTN Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 6 |
| First Seen: | December 17, 2015 |
| Last Seen: | March 28, 2023 |
| OS(es) Affected: | Windows |
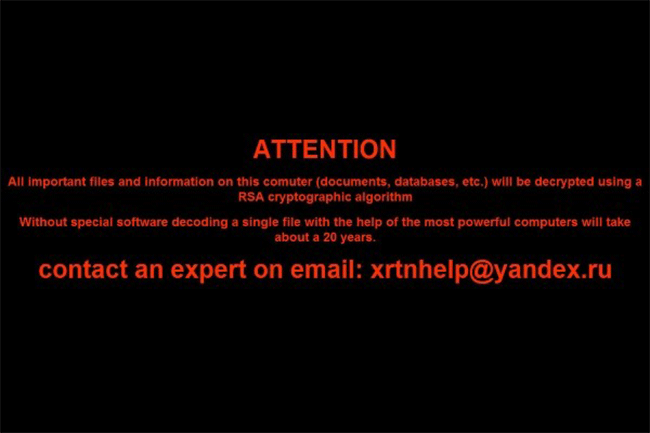
XRTN Ransomware Image
The XRTN Ransomware is a ransomware infection that encrypts data by using batch files. PC security researchers have recently detected the XRTN Ransomware for the first time. When viewed in the wild, the XRTN Ransomware uses RSA-1024 encryption to encrypt the victim's data. To carry out the encryption, the XRTN Ransomware uses the GnuPG (Gnu Privacy Guard), an open source encryption program that is freely available. The XRTN Ransomware is closely related to Vaultcrypt, a threatening ransomware infection that first appeared in spring of 2015. The XRTN Ransomware uses an HTA document that appears during start-up to deliver the XRTN Ransomware's ransom note. This message claims that computer users should contact a Russian email address, xrtnhelp@yandex.ru, to decrypt their files. No price is quoted, meaning that it is likely that the ransom is adjusted depending on the severity of the attack and quality of the files. At this date, there is no way to decrypt the encrypted files without the decryption key.
The Serious Consequences of a XRTN Ransomware Infection
The XRTN Ransomware has a unique architecture, which contains batch files to carry out the encryption process. The XRTN Ransomware is installed using an unwanted JavaScript file that connects to its command and control domain, gusang.vpscoke.com, to download and install its associated files. The XRTN Ransomware downloads the GnuPG executable file, a Microsoft Word file, and the batch file used for the XRTN Ransomware's encryption. It is likely that the JavaScript file that delivers the XRTN Ransomware is included as a threatening email attachment in the form of a fake Word document. Microsoft Word macros may be used to deliver threatening code to the victim's computer, making these types of documents far from safe.
When the XRTN Ransomware's batch file is executed, the XRTN Ransomware generates the decryption key and scans all the infected computer's drives in search for its target files. After the XRTN Ransomware encrypts a file, it adds the XRTN extension to the end of the file. The XRTN Ransomware targets the following file types, making it likely that the XRTN Ransomware will encrypt files that could be important to the computer user:
.xls, *.doc, *.xlsx, *.docx, *.pdf, *.rtf, *.cdr, *.psd, *.dwg, *.cd, *.mdb, *.1cd, *.dbf, *.sqlite, *.jpg, *.zip
The XRTN Ransomware deletes shadow volume copies of the encrypted files, making it impossible for computer users to recover their files using a shadow volume browser of some sort. As part of the XRTN Ransomware encryption process, the XRTN Ransomware will create a file named XRTN.key that contains the private encryption key and data about the infected computer and then encrypt it. The XRTN Ransomware will overwrite all free disk space on targeted hard drives to prevent computer users from using file recovery programs to recover from the XRTN Ransomware attack. The XRTN Ransomware then displays its ransom note.
Recovering from a XRTN Ransomware Attack
PC security researchers suspect that victims of the XRTN Ransomware will be asked to deliver the XRTN.key file and then to pay the ransom amount. The threat developer can decrypt this file using a master decryption key and then deliver the victim's the specific decryption key. There is currently no way to decrypt the files without access to the key. Because of this, the best way of handling ransomware infections like the XRTN Ransomware is prevention. PC security researchers strongly stress the importance of a backup method, either on an external memory device or using the Cloud. This way, computer users can recover from an attack by wiping the affected hard drive and reinstalling their files from the backed up location. Future attacks can be prevented by avoiding email attachments from unsolicited sources.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.