Xctdoor Backdoor
A South Korean ERP (Enterprise Resource Planning) vendor's update server was discovered compromised, distributing a Go-based backdoor named Xctdoor. Researchers uncovered this attack in May 2024, and while they didn't pinpoint a specific threat actor or group, they noted similarities with tactics used by Andariel, a subgroup linked to the notorious Lazarus Group.
These tactics echo past incidents involving the North Korean adversary, who previously exploited the ERP solution to disseminate malware such as HotCroissant (also known as Rifdoor) in 2017. This was achieved by implanting malicious code into a software update mechanism.
Table of Contents
The Xctdoor Backdoor Provides Attackers with Numerous Harmful Capabilities
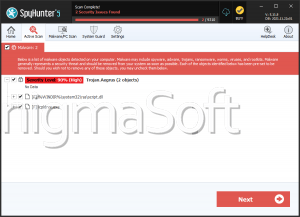
During the attack analysis, it was determined that the executable was altered to run a DLL file from a specific path using the regsvr32.exe process instead of initiating a downloader. This DLL file, known as Xctdoor, possesses capabilities for capturing system information such as keystrokes, screenshots and clipboard contents, and executing commands issued by the attacker.
Xctdoor communicates with a Command-and-Control (C2) server over HTTP, with packet encryption utilizing the Mersenne Twister (MT19937) and Base64 algorithms. The attack also involves another malware variant named XcLoader, designed to inject Xctdoor into legitimate processes like 'explorer.exe.' Recent findings indicate instances where inadequately secured Web servers have been compromised to install XcLoader since at least March 2024.
The Same Process Abused by Other Malware Threats
The regsvr32.exe process has been exploited in other campaigns linked to North Korea, notably by the Kimsuky APT group. They have utilized an undisclosed backdoor named HappyDoor, operational since at least July 2021.
These attack sequences typically start with spear-phishing emails distributing a compressed file. Within this archive, an obfuscated JavaScript or dropper is found, which, upon execution, launches HappyDoor alongside a decoy file. HappyDoor, implemented as a DLL file through regsvr32.exe, establishes communication with a remote server via HTTP. Its functionalities include data theft, file download/upload capabilities, and the ability to self-update and terminate processes.
Backdoor Infections can Have Severe Consequences for Victims
Victims of backdoor malware infections can face severe consequences due to the stealthy and persistent nature of these threats. Here are some potential impacts:
- Data Theft: Backdoors often allow attackers to harvest private information such as login credentials, financial data, intellectual property and personal files. This collected data can be exploited for financial gain or used in further attacks.
- Surveillance and Monitoring: Backdoors may enable attackers to monitor and surveil the victim's activities, including keystrokes, screenshots, webcam feeds and microphone input. This invasion of privacy can lead to personal or corporate espionage.
- Unauthorized Access: Attackers can gain prolonged unauthorized access to compromised systems. This access can be used to manipulate or sabotage systems, disrupt operations or even deploy additional malware.
- System Compromise: Backdoors often weaken the overall security posture of the system, making it vulnerable to further exploitation. This can lead to the compromise of other connected systems or resources within the network.
- Financial Loss: Businesses may suffer financial losses due to theft of funds, loss of business opportunities, legal liabilities and costs associated with remediation and recovery efforts.
- Reputation Damage: For organizations, a backdoor infection can lead to reputational damage, loss of customer trust and diminished brand value. This can have long-term consequences on business relationships and operations.
- Operational Disruption: Backdoors can disrupt normal operations by causing system crashes, slowdowns or denial of service conditions. This can result in downtime, loss of productivity and financial impacts due to disrupted services.
- Regulatory and Compliance Issues: Organizations may face regulatory fines and legal consequences if the compromised systems handle sensitive data subject to privacy laws or industry regulations.
- Difficulty in Detection and Removal: Backdoors are designed to evade detection by security measures such as anti-malware software and firewalls. Detecting and removing them completely can be challenging, requiring specialized knowledge and tools.
- Long-Term Vulnerability: Even after initial remediation, compromised systems may remain vulnerable to future attacks or persistent backdoor reactivation attempts by determined attackers.
Overall, the consequences of backdoor malware infections can be severe and multifaceted, impacting both individuals and organizations in terms of financial, operational, and reputational damage, as well as compromising their privacy and security.