Worm:Win32/Morto.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 15,181 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 4,218 |
| First Seen: | August 30, 2011 |
| Last Seen: | February 4, 2026 |
| OS(es) Affected: | Windows |
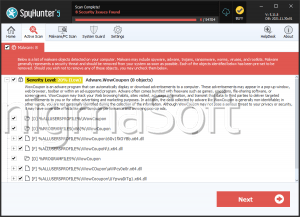
Worm:Win32/Morto.A is a malicious worm that allows attackers obtain unauthorized access to a compromised PC system. Worm:Win32/Morto.A spreads by attempting to attack administrator passwords for Remote Desktop connections on the network. Worm:Win32/Morto.A corrupts PC systems that have weak passwords. Worm:Win32/Morto.A is also able to download and install other malware threats. Worm:Win32/Morto.A consists of some components that include an executable dropper component (the installer) and a DLL component, which executes the payload. Worm:Win32/Morto.A copies itself by using other parasites like Trojan.DownLoader4.48720 or Trojan horse Generic24.OJQ. Worm:Win32/Morto.A will connect to a remote server without its victim's awareness and will block you from using all anti-virus software to evade detection and deletion. You should delete Worm:Win32/Morto.A from the affected machine immediately after detection.
Table of Contents
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %windows%\temp\ntshrui.dll | |
| 2. | %Windows%\clb.dll | |
| 3. | \sens32.dll | |
| 4. | %Windows%\clb.dll.bak | |
| 5. | c:\windows\offline web pages\cache.txt |
Analysis Report
General information
| Family Name: | Worm.Runouce.A |
|---|---|
| Signature status: | Hash Mismatch |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
74ec84ad6a3590959d66ae0f9acabcb5
SHA1:
9c72c6199d08fc05daaf657442af56a2c453ca0a
SHA256:
C0B998CADAAB36D1BC3FAD60472FF118885CAB8BCFDEDEA3E221FBAB59835213
File Size:
194.79 KB, 194790 bytes
|
|
MD5:
aa956247b158dd9abb55d50332352210
SHA1:
72aafca0185684c1da47356efa7b6e5b55a1827c
SHA256:
A7DE8932C72A0C7662567FBF5397F4E8FAFBCAFC79066CC92A717114A421D392
File Size:
283.74 KB, 283740 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | Microsoft Corporation |
| File Description | Microsoft Edge Update |
| File Version | 1.3.211.7 |
| Internal Name | Microsoft Edge Update |
| Legal Copyright | Copyright 2018 Microsoft Corporation |
| Original Filename | MicrosoftEdgeUpdate.exe |
| Product Name | Microsoft Edge Update |
| Product Version | 1.3.211.7 |
| Upstream Version | 1.3.99.0 |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Microsoft Corporation | Microsoft Code Signing PCA 2011 | Hash Mismatch |
File Traits
- 2+ executable sections
- HighEntropy
- Installer Manifest
- nosig nsis
- No Version Info
- Nullsoft Installer
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 1,067 |
|---|---|
| Potentially Malicious Blocks: | 52 |
| Whitelisted Blocks: | 995 |
| Unknown Blocks: | 20 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block