Worm.Slogod
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 19,847 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 1,579 |
| First Seen: | December 23, 2011 |
| Last Seen: | February 4, 2026 |
| OS(es) Affected: | Windows |
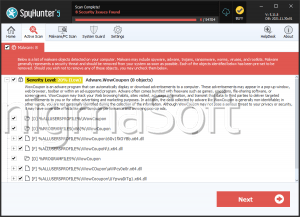
Worm.Slogod is a malicious computer worm that infiltrates into the corrupted PC system stealthily through removable drives. Once installed, Worm.Slogod executes MS Notepad and shows an IT themed parody of the 'Our Father' prayer created in French. Worm.Slogod will also disable the system's Autorun settings for removable drives and it will disable the 'File' drop down menu for all system folders. Worm.Slogod will also disable 'System Restore'. Worm.Slogod will cover or deactivate various computer settings, options and tabs such as the 'Documents' shortcut on the Start Menu, or the 'Hardware tab' for the Sounds and Multimedia and the Keyboard and Mouse on the Control Panel. Worm.Slogod also frequently empties the recycle bin without the computer user's knowledge or interruption. Worm.Slogod will also close the 'Command Prompt' when executed. Worm.Slogod will edit the computer's mouse settings and block you from changing or restoring them. Worm.Slogod will load various screensavers. You need to remove Worm.Slogod immediately after detection.
Table of Contents
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | ALCMTR.EXE | |
| 2. | kJbIGuFtdKeYyWT.exe | |
| 3. | gpag.exe | |
| 4. | server.exe | |
| 5. | MTW.exe | |
| 6. | AudioTreiber_x64.exe | |
| 7. | Aimza bYpAsS 358.exe | |
| 8. | audiohd.exe | |
| 9. | winupdate.exe | |
| 10. | firefox.exe | |
| 11. | Explorer.exe | |
| 12. | m.vbs | |
| 13. | imwin.jpg | |
| 14. | system.vbe | |
| 15. | MLN4.vbs | |
| 16. | system32.db | |
| 17. | Imel.dll.vbs | |
| 18. | su_virus.vbs | |
| 19. | NewFile.vbs | |
| 20. | winrun.dll.vbs | |
| 21. | winjpg.jpg | |
| 22. | sVirusprotection.vbe |
Analysis Report
General information
| Family Name: | Worm.Runouce.D |
|---|---|
| Signature status: | Hash Mismatch |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
fc94a8b1e93a492d65d2261115f68445
SHA1:
9bffc5fd9dcace928354033070ec35b5d922a1b9
SHA256:
581F9CECD5BF8C7F421FC2295FCDABD3C76C64BD7EB75973FDE46CB4B20C4FB6
File Size:
120.32 KB, 120316 bytes
|
|
MD5:
d4b31d754400780a83cf9d54a33e61db
SHA1:
745e3796c36748ee017a5fd4048c5da8e7d02e8d
SHA256:
C7AB81F62D801C137EE2066AC676869F175D2DBCBD9041BF3972F78136425DD8
File Size:
1.42 MB, 1419684 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename |
|
| Product Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| QIHU 360 SOFTWARE CO. LIMITED | Symantec Class 3 SHA256 Code Signing CA | Hash Mismatch |
| QIHU 360 SOFTWARE CO. LIMITED | VeriSign Class 3 Code Signing 2010 CA | Hash Mismatch |
File Traits
- 2+ executable sections
- HighEntropy
- Installer Manifest
- Installer Version
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 1,929 |
|---|---|
| Potentially Malicious Blocks: | 438 |
| Whitelisted Blocks: | 1,427 |
| Unknown Blocks: | 64 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block