Worm.Mira
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 10,972 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 4,132 |
| First Seen: | September 16, 2015 |
| Last Seen: | February 8, 2026 |
| OS(es) Affected: | Windows |
Worm.Mira is a polymorphic worm capable of spreading by creating copies of itself in several folders on infected systems. What is a polymorphic threat? A malware of this kind continually changes the features it possesses to avoid detection for as long as possible. Many of the known threats today can be polymorphic, not just worms but trojans, keyloggers, and more. Polymorphic techniques often include changing identifiable characteristics to threats, such as file names, encryption algorithms, and more to ensure the threat stays ahead of detection techniques.
In this case, Mira mimics existing folders and files by creating an executable bearing the same name. Mira then marks the original folder or file as hidden to replace it in the 'eyes' of the system. This mimic uses a folder or file icon and opens the associated folder when executed, same as the original. The mimics may be spotted if the Windows settings are tweaked to show hidden files. Mira attempts to add files to all removable drives as well, so users should keep that in mind if they try to restore backups to an already infected system.
Signs of infection may include the creation of new files with the following names:
- %APPDATA%\Saaaalamm\Mira.h
- %APPDATA%\[a-z]{5,6}.exe
- %SYSTEMDRIVE%\TEMP.exe
- %SYSTEMDRIVE%\Program Files .exe
\System Volume Information .exe
Table of Contents
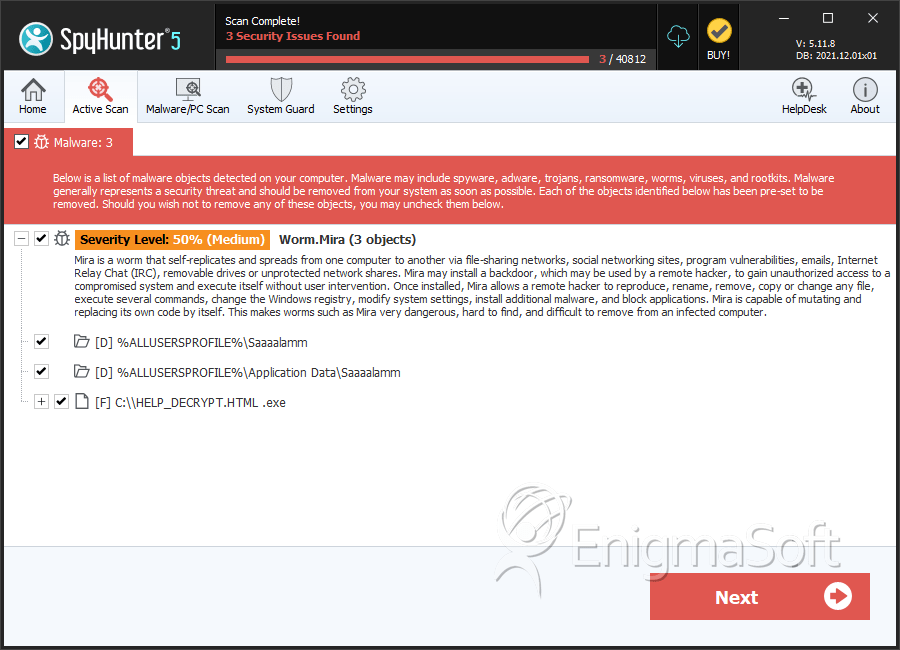
SpyHunter Detects & Remove Worm.Mira
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | HELP_DECRYPT.HTML .exe | 670dbb2ddd39c981830eeab5229ced3a | 0 |
Directories
Worm.Mira may create the following directory or directories:
| %ALLUSERSPROFILE%\Application Data\Saaaalamm |
| %ALLUSERSPROFILE%\Saaaalamm |
Analysis Report
General information
| Family Name: | Worm.Mira |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
9c5017e89b8a20c3083204a76f9d3a35
SHA1:
360e8734001e6e6a706e65ea4d7f82a438994c91
SHA256:
C1C21EAD5A10804CE929FACA2601EAEE45D805C75EB7D5C758DD1A9439270244
File Size:
5.87 MB, 5865984 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have security information
- File has exports table
- File has TLS information
- File is 64-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- 2+ executable sections
- HighEntropy
- No Version Info
- x64
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 379 |
|---|---|
| Potentially Malicious Blocks: | 7 |
| Whitelisted Blocks: | 42 |
| Unknown Blocks: | 330 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
