Win32/Delf.QCZ
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
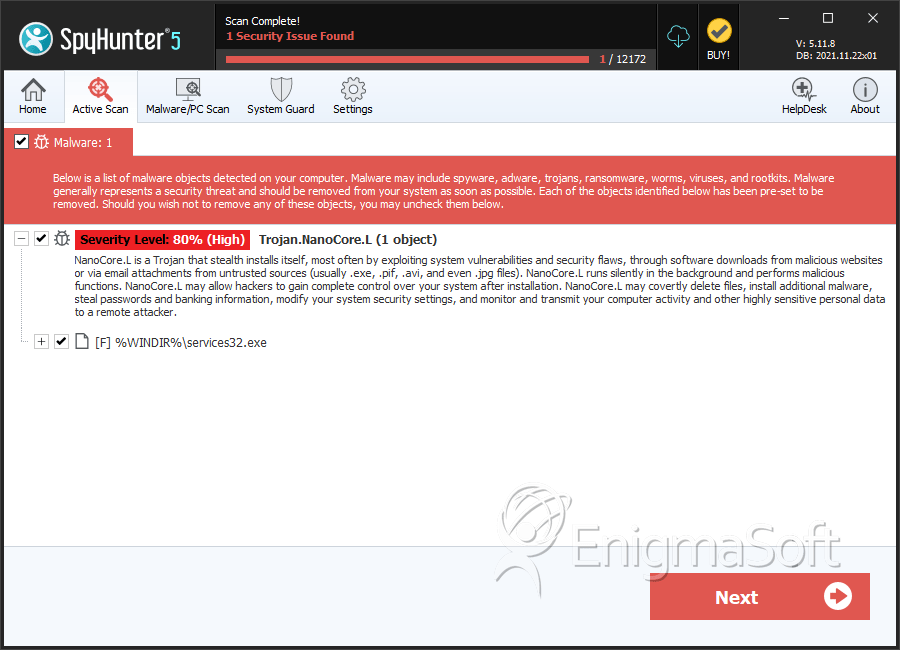
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 41 |
| First Seen: | August 31, 2011 |
| Last Seen: | November 29, 2021 |
| OS(es) Affected: | Windows |
Win32_Delf.QCZ is a devious and chatty Trojan that knows how to make its way around the friendly Facebook platform. Trojan_Win32Delf.QCZ uses an old trick to lure PC users; it pretends to be a codec component to view a video supposedly containing the victim's likeness. However, what makes Trojan_Win32_Delf.QCZ most interesting is Win32_Delf.QCZ's ability to engage victims into a dialogue, as opposed to just posting a one-liner and poisonous link.
If you look at the samples collected below, it is obvious that cybercriminals are enjoying the gullibility offered by social networks and are putting their social engineering skills to good use.
Friend (aka virus): Hi, how are you?
Victim: Hi, friend (aka virus)
Friend (aka virus): good. Wanna laugh?
Victim: Absolutely
Friend (aka virus): It is you on the video?)) want to see?)
Victim: Yes, yes, yes … send me the link
Friend (aka virus): http:\\poisonous link
Cybercriminals exploit any and everything, including software, hardware and human behavior and often hack or spoof accounts, so victims or recipients will fall trap and trust the lies.
The poisonous link routes to a rogue YouTube webpage and, in order to watch the video, you'll need to upgrade your Adobe Flash Player. Of course, this is a trap and the update is fake. To add to the deception, there are validating comments from other friends. Here are a few examples:
Friend2 (aka virus): He must have been shamed to do that
Friend3 (aka virus): had to update Flash Player, but it was worth it this video is the very best!
Friend4 (aka virus): one word for it – TERRIBLE!!
Another interesting twist deals with the payload of Trojan_Win32_Delf.QCZ. Trojans are known to drive or simulate a security breach in hopes of tricking a PC user into buying a useless anti-virus program. However, Trojan_Win32_Delf.QCZ looks for and impersonates a particular anti-virus or security program already in place. Why? This most likely is a distraction ploy, so that the victim will not suspect other malicious behaviors such as these:
- Theft of vital data stored on the system or being entered into web-based forms.
- Theft of the email address book so a spammer can spam persons on the lists.
- Downloading more malicious programs, including a rogue security program that uses fake scans, alerts and reporting.
ESG Security researchers tested the malicious behavior of Win32_Delf.QCZ and have noticed the plantation and installation of a mining application called Bitcoin, indicating the builder (malware maker or hacker) is up to more malicious activity. In a nutshell, Bitcoins are a decentralized, P2P virtual currency and are mainly used underground to buy all sorts of things, legal or illegal, without government interference. Bitcoins can be bought, traded or generated through CPU usage, which means at a minimum, your system resources will be secretly used to generate Bitcoins.
Trojan_Win32_Delf.QCZ performs the following malicious functions:
- Search for specific AV programs to delete and later impersonate.
- Disable administrative controls such as Task Manager, so it can't be used to stop its process from running.
- Modify the registry by editing sub-keys and making an entry to loop its venomous executable, so it runs at every boot.
- Download a binary via HTTP over port 80 and 8080.
- Survey the system and check to see if an ATI graphic card exist and, if so, download drivers.
- Modify the system to run its venomous executable in Safe Mode.
If the victim doesn't restart their system in a specific window of time, automatic boot will occur.
Not all malware announces its arrival, but there usually are subtle hints of an evasion such as these:
- System running slow due to hidden programs running in the background, like the evasive Bitcoin application or venomous executables of Trojan_Win32_Delf.QCZ.
- System booting on its own,
- Browser redirects to unwanted or malicious websites.
- An assault of alerts or warnings indicating an intrusion, such as the one Trojan_Win32_Delf.QCZ intends to exhibit when it impersonates AV programs you may have installed.
- Applications not running properly or at all.
At the first hint of an infestation, you really need to act fast. Use aggressive methods to search for and remove all malware off your PC. To catch viruses fortified by a rootkit, you need to use a stealth anti-malware containing an anti-rootkit component. Don't waste time on useless anti-virus or anti-spyware programs that are incapable of searching your system's kernel and safely remove ALL types of malware or ones that do not update definitions around the clock. Some Trojans may mutate often, to oppose combative measures taken by the Internet security community and this could leave you experiencing deja vu each and every time your computer boots up.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Suspicious file |
| AVG | Generic26.BSXU |
| Fortinet | W32/Menti.IPY!tr |
| Microsoft | Backdoor:Win32/Bafruz.B |
| Antiy-AVL | Trojan/Win32.AntiAV.gen |
| Sophos | Troj/Bafruz-B |
| AntiVir | BDS/Bafruz.B.3 |
| BitDefender | Trojan.Generic.6794711 |
| eSafe | Win32.TRCrypt.Ulpm |
| Avast | Win32:MalOb-IJ [Cryp] |
| Symantec | Trojan.Malcol |
| F-Prot | W32/Agent.JXZ |
| K7AntiVirus | Riskware |
| McAfee | Generic-FABJ!19A418E0400D |
| CAT-QuickHeal | Trojan.AntiAV.omn |
SpyHunter Detects & Remove Win32/Delf.QCZ
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | services32.exe | 19a418e0400d554dda9b54520bdf52b4 | 33 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.