Win32/Delf.NRJ
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 4,950 |
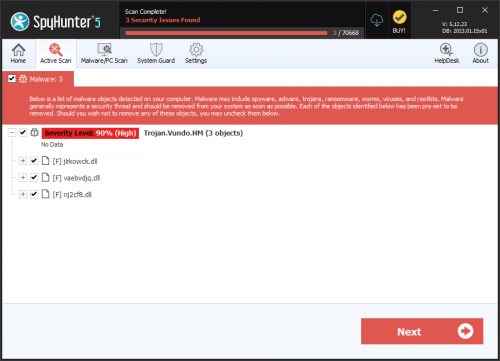
| Threat Level: | 90 % (High) |
| Infected Computers: | 386 |
| First Seen: | January 12, 2016 |
| Last Seen: | April 14, 2026 |
| OS(es) Affected: | Windows |
Win32/Delf.NRJ is a threatening program that is a Backdoor Trojan. The Win32/Delf.NRJ Backdoor Trojan is written in the Delphi programming language that allows it to load plug-ins and use COM independent interfaces. In other words, the handlers of the Win32/Delf.NRJ malware can expand its functionality and launch custom-made attacks on compromised computers and networks. The Win32/Delf.NRJ Backdoor Trojan may be deployed to users via malvertising involving exploit kits like Angler and Infinity. Security analysts add that the Win32/Delf.NRJ malware may be used in spear phishing attacks too. The Win32/Delf.NRJ Backdoor Trojan may be detected by security scanners under the names of Backdoor:Win32/Spamchn and Virus:Win32/Grenam as well. The Win32/Delf.NRJ Backdoor Trojan has interesting features that include the modification of executable files and shellcode execution.
The Win32/Delf.NRJ malware can use behavioral algorithms to recognize the user's preferred programs and alter their main executable to spread it to other users. For example, a user that is infected with the Win32/Delf.NRJ malware and may use Google Chrome as his default Internet client is very likely to have its primary executable altered by Win32/Delf.NRJ. When the infected user runs the corrupted Google Chrome browser, the Win32/Delf.NRJ Backdoor Trojan may copy itself to other computers and notify its operators of successful infiltration. Still, Win32/Delf.NRJ is a backdoor Trojan that can allow its handlers to close, and run and install programs on infected systems remotely. Additionally, the Win32/Delf.NRJ malware may use unencrypted HTTP channels to relay data from your computer to a remote host if instructed to. Security analysts reveal that the Win32/Delf.NRJ Backdoor Trojan may be used in DDoS attacks at servers and corporate networks. The Win32/Delf.NRJ malware may place its files in the Temporary Internet Files folder and label them as persistent cookies to hide them from security scanners. The Win32/Delf.NRJ malware can be deleted by a reputable anti-malware application that is worth investing in.
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Klone.A |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
f7bacd4f795411eb2aaa923761fba789
SHA1:
613b2f039f2762cd80e91bb3083f9817355e1f5a
SHA256:
AA5CD6EC750F81F45B7D25685BA14724716405EBB8B0AD0BE46FA290F5756390
File Size:
3.28 MB, 3277032 bytes
|
|
MD5:
2592261c2805582f88172f7fecfb2424
SHA1:
2875f02ca49ddbf825dd5650a0f3ffd8106cffbf
SHA256:
AAEFD1097E3347A7C3B8AF0D149BB5AA9242AEC047DFE3E81C24C56F889CD0E1
File Size:
91.43 KB, 91434 bytes
|
|
MD5:
3ca17a48e261f5e2f84826419d2b4f2c
SHA1:
9fa5ba5399ae1b7fd9905a983f12ab2a684134b9
SHA256:
C1042187A04C3C894324A35620B53CFF7C09191B4ED53FBEA85E3B443754CE12
File Size:
2.30 MB, 2302464 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments |
|
| Company | Reversing Labs |
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Legal Trademarks | Password Memory(tm) |
| Original Filename | keynote.exe |
| Product Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Gretech Corp. | Thawte Premium Server CA | Root Not Trusted |
File Traits
- 2+ executable sections
- HighEntropy
- x86
- y0da
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2 |
|---|---|
| Potentially Malicious Blocks: | 1 |
| Whitelisted Blocks: | 1 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\nsac988.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
| c:\users\user\appdata\local\temp\nsqc999.tmp\langdll.dll | Generic Write,Read Attributes |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Anti Debug |
|
| User Data Access |
|