W32.Ramnit
The W32.Ramnit worm was first detected in January of 2010. This malware infection can affect 32-bit Windows operating systems and is the one to be blamed for a high number of malware attacks since its discovery. Like most worms, W32.Ramnit can spread through removable memory devices and folders shared on a network. W32.Ramnit can also be classified as a Virus, since W32.Ramnit has the capacity to infect executable files. ESG security researchers consider that W32.Ramnit constitutes an extremely severe threat to an infected computer system. Due to the fact that this malware infection can corrupt executable files, W32.Ramnit can often render important files unusable.
Table of Contents
How the W32.Ramnit Virus Infects a Computer System
W32.Ramnit will typically create a folder in your Program Files folder with innocuous name of MNetwork. This is intended to mislead the victim and hide W32.Ramnit's real identity. W32.Ramnit is designed to spread on the infected computer system by searching out for any files with the .dll, .exe or .html extensions and then corrupting them by appending a dangerous bit of code the last part of the file. Whenever an infected file is executed, W32.Ramnit creates an additional copy of W32.Ramnit's executable file in the infected file's folder named srv.exe and runs it spreading the infection throughout the victim's computer system. W32.Ramnit also creates an autorun.inf file which executes itself whenever the victim's drive or Recycling bin is accessed. Whenever W32.Ramnit's executable runs, it attempts to establish a connection with the website rmnzerobased.com from where W32.Ramnit tries to download a malicious .dll file and register it on the victim's computer system. However, thanks to the actions of PC security analysts, this malicious website no longer hosts the malicious .dll file associated with W32.Ramnit.
Dealing With a W32.Ramnit Worm Infection
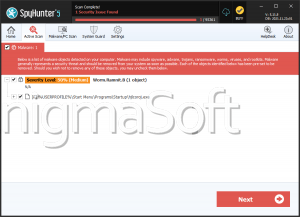
Because of W32.Ramnit's particular characteristics, ESG security researchers do not advise using manual removal to deal with this malware infection. A W32.Ramnit worm attack causes problems which are extremely difficult to deal with manually, but that can be fixed with an automated anti-virus application. Some of these problems include the fact that removal of W32.Ramnit necessarily must deal with all copies of this malware infection, which can be difficult considering that W32.Ramnit creates multiple copies of itself on the victim's hard drives. Removal of W32.Ramnit also involves fixing all corrupted files which will also require a decryption algorithm. Fortunately, most fully-updated anti-malware software on the market can deal with this malware infection.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | C:\UserProfile\Local-Settings\Application Data\\.exe | |
| 2. | C:\ProgramFiles\Microsoft\DesktopLayer.exe | |
| 3. | C:\Windows\System32\rundll32Srv.exe | |
| 4. | C:\Windows\System32\dmlconf.dat |