Vista Internet Security 2012
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 63 |
| First Seen: | December 14, 2011 |
| Last Seen: | May 9, 2023 |
| OS(es) Affected: | Windows |
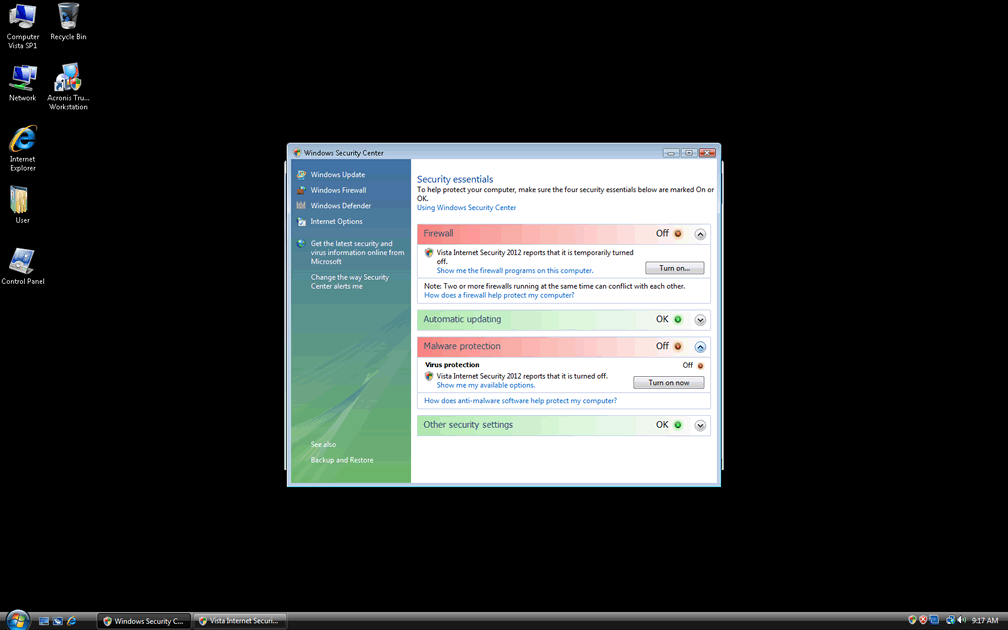
Vista Internet Security 2012 Image
Vista Internet Security 2012 is one of the manifestations of a family of rogue anti-spyware programs. These rogue anti-spyware programs have a high threat level and pose a significant security risk. If a user finds one of these programs on his computer, it is important to remove the program manually or with a legitimate anti-malware tool, and then scan the computer for additional harmful threats infecting the machine.
Table of Contents
What Exactly is Vista Internet Security 2012?
This harmful program has Vista Internet Security 2012's origins in the Russian Federation, a country that has produced many of the world's most dangerous and insidious viruses and malware. As the name of the program implies, Vista Internet Security 2012 goes under the guise it wascreated in 2012, and as an evolution of previous similar programs that lacked the ability to change, according to the user's operating system. The actual name of the file which makes possible the name changing is Ppn.exe. This file can also show up as Kdn.exe or with another three-letter name. This file can have dozens of different names. Ppn's main feature is that it changes names and skins according to the user's operating system. Therefore, it created three main sets of names and themes for Vista Internet Security 2012, corresponding to Windows 7, Windows XP, and Windows Vista. As can be seen from Vista Internet Security 2012's name, Vista Internet Security 2012 is the name that it takes when attacking PCs running Windows Vista.
Detecting a Vista Internet Security 2012 Infection
The way this family of harmful security applications installs is by a Trojan that mimics a Windows Automatic Update. A fake Windows Update notification is often the first sign that the computer is infected. This happens before the program is actually installed, and the name and theme customized to the user's particular operating system. The authors designed the notification to be very similar, and practically identical to a real Windows Automatic Update, making the user believe that his operating system is simply downloading a normal update. Here is where the Trojan detects the operating system being used and downloads the appropriate theme for the program. There have been cases in which the program downloads the wrong skin, resulting in a Vista Internet Security 2012 infection on an operating system that is not Windows Vista. However, these cases are rare. Once the program is installed, the rest of the warning signs are similar to other rogue anti-spyware applications. Some of these are:
- A fake system scan.
- Internet and file browsing problems.
- Constant misleading security alerts.
Things to Avoid When Dealing with Vista Internet Security 2012
When dealing with Vista Internet Security 2012, or similar rogue anti-spyware programs, there are several things which are important to avoid. Pay attention to these indications, to prevent you from becoming a victim of a scam, or irreparably damaging your computer.
- Do not enter your credit card number, under any circumstances. This will do nothing to stop the annoying security alerts and will not restore your computer's full operation.
- Do not delete the files showing up as infected in the fake system scan. These are often harmless files that are not infected at all. Some of them may be essential to your system's correct operation, and deleting them may irreparably corrupt your system.
-Do not enter personal or sensitive information into your computer, if you are concerned about being infected by Vista Internet Security 2012. These kinds of programs often reveal your personal information to third parties and follow your browsing habits on the Internet.







File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %AppData%\Local\(random 3 letters).exe | |
| 2. | %AllUsersProfile%\wrdgt6knnhg8qwxst6hfljs11 | |
| 3. | %Temp%\wrdgt6knnhg8qwxst6hfljs11 | |
| 4. | %AppData%\Roaming\Microsoft\Windows\Templates\wrdgt6knnhg8qwxst6hfljs11 | |
| 5. | %AppData%\Local\wrdgt6knnhg8qwxst6hfljs11 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.