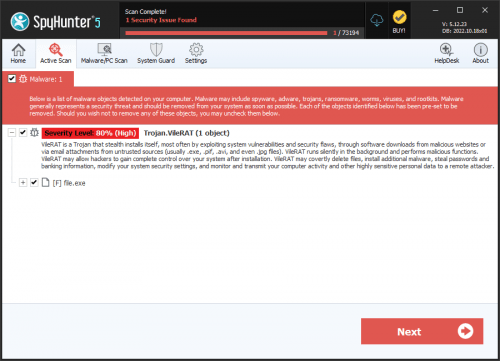
VileRAT Malware
The VileRAT Malware is a potent threat used by cybercriminals to target foreign currency and cryptocurrency exchange brokers. Targeted or compromised organizations have been identified across a wide range of geographic locations, including Kuwait, the UAE, the Russian Federation, Germany, Bulgaria and more.
According to a report published by malware experts, VileRAT has been attributed to the DeathStalker cybercrime group, an organization believed to offer hacking-for-hire services. The VilerRAT campaign exhibits DeathStalker's improved capabilities to avoid detection through the use of state-of-art obfuscations, multi-layer, as well as low-layer packing, in-memory PE loader with multi-stage execution, and even heuristic bypasses designed to fool specific security solutions. However, the final VileRAT payload is still sitting at a massive 10MB in size.
Once the RAT (Remote Access Trojan) has been executed on the breached system, it allows the threat actors to execute arbitrary commands via Command Prompt. The hackers also can download additional files or payloads, execute chosen files, manipulate the file system, kill processes, open websites and more. VileRAT can establish keylogging routines to obtain sensitive information, such as account credentials, log in details, payment data, etc.
To ensure its continued presence on the infected system, VileRAT activates a persistence mechanism by creating scheduled tasks via Windows Task Scheduler. The DeathStalker hackers can push updates to the threat from the Command-and-Control server of the operation.