Velso Ransomware
The Velso Ransomware is an encryption ransomware Trojan. PC security researchers first received reports of the Velso Ransomware infection on January 15, 2018. The Velso Ransomware is being distributed using spam email messages. The method used to deliver the Velso Ransomware uses a method that has been observed in countless other encryption ransomware Trojans. Victims of the Velso Ransomware attack will receive a spam email message with an attached PDF or DOCX file that uses embedded macros to download and install the Velso Ransomware onto the victim's computer. Corrupted files that seem to be named with random strings of letters and numbers deliver the Velso Ransomware.
Table of Contents
A Galactic Civil War Fighter that will Attack Your Files
The Velso Ransomware carries out a typical version of these infections, using a strong encryption algorithm (a combination of AES 256 and RSA 1024 encryption) to make the victim's files inaccessible. The Velso Ransomware will deliver a ransom note demanding the payment of several hundred dollars in Bitcoin as a condition to get the decryption key necessary to recover the affected files once the victim's files have been compromised. Threats like the Velso Ransomware will take the victim's files hostage in exchange for a ransom payment. The Velso Ransomware and similar threats will target the user-generated files such as videos, images, and various document types, while avoiding the Windows system files (this is because the Velso Ransomware requires Windows to remain functional to demand a ransom payment from the victim). The Velso Ransomware will identify the files encrypted in its attack by adding the file extension '.velso' to each of the encrypted files. The file types that are targeted by infections like the Velso Ransomware include:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The Velso Ransomware’s Ransom Demand
After the Velso Ransomware has finished encrypting the victim's files, the Velso Ransomware will deliver a ransom note, with a message asking the victim to contact the cybercrooks via email to recover the affected files. Victims of the Velso Ransomware attack have reported that the Velso Ransomware will drop a text file named 'get_my_files.txt' on the infected computer's desktop. The full text of the Velso Ransomware ransom note reads:
'Hello. If you want to return files, write me to e-mail MerlinVelso@protonmail.com
Your userkey: [base64 string]'
The Velso Ransomware ransom note demands that the victim contact its perpetrators. When victims write to the provided email address, these people will typically ask the victim to make a payment to a Bitcoin wallet. The ransom amount for most of these threats varies between 500 and 2000 USD, although the amounts involved in these attacks can vary wildly and the cybercrooks also may adjust the amount of the ransom depending on the profile of the victim if the attack has affected an individual versus a business or institution particularly.
Protecting Your Data from the Velso Ransomware
If your data has been compromised by a Velso Ransomware attack, PC security researchers advise restoring the affected files from a backup copy. An updated security program can be used to remove the Velso Ransomware itself (although it will not restore affected files). Malware researchers advise against paying the ransom demanded by these attacks.
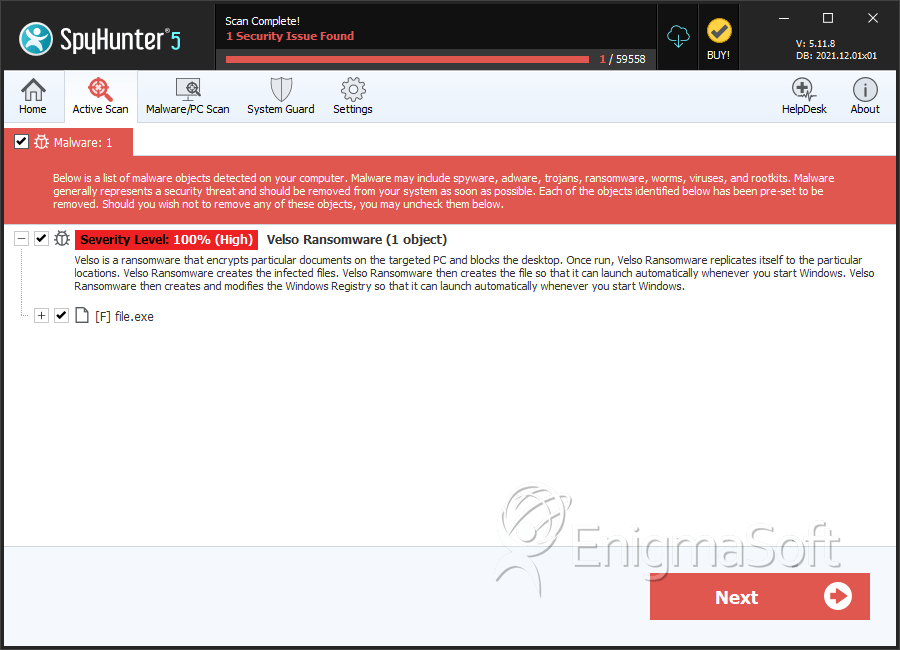
SpyHunter Detects & Remove Velso Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 41acc186c5955a7495898a09f2b3484b | 0 |

