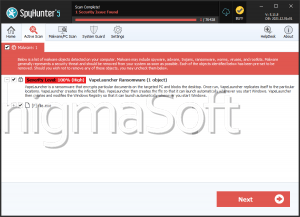
VapeLauncher
VapeLauncher is a ransomware Trojan that has been released as a 'proof of concept' on GitHub. VapeLauncher is a variant of CryptoWire, a well-known ransomware threat. VapeLauncher is being used to target individual computer users and may be distributed using corrupted documents attached to spam email messages. These documents may take the form of text documents that include macros to execute corrupted code on the infected computer. VapeLauncher has been released disguised as a hacking component or another component for the Minecraft game. VapeLauncher behaves in a way that is very similar to other 'educational' ransomware Trojans such as EDA2 or HiddenTear.
Table of Contents
VapeLauncher Performs Various Harmful Actions on Your Computer
VapeLauncher uses various Windows tools during its attack, including batch files, access tools such as schtasks.exe and vssadmin.exe and others. VapeLauncher also empties the Recycling Bin on the infected computer, deletes the Shadow Volume Copies, and the System Restore points in an attempt to prevent computer users from restoring their files using these methods. VapeLauncher uses the AES 256 encryption to encrypt the victims' files and make them inaccessible completely. VapeLauncher loads a Windows service named RASMAN to establish communications with its Command and Control server. Unlike many other encryption ransomware Trojans, VapeLauncher does not add a file extension to the infected files. VapeLauncher carries out an attack particularly curious, encrypting the first 1024 bytes of the file headers to prevent the victim from accessing the files on the infected computer. During its attack, VapeLauncher avoids the following directory:
AppData
Program Data
Program Files
Program Files (x86)
Windows
During its attack, VapeLauncher targets numerous file types, including media files, image files, databases, documents of various types, spreadsheets, and numerous other files. VapeLauncher encrypts files on all drives on the infected computer, including external memory devices connected to the infected computer and directories shared on the network.
How VapeLauncher Demands Its Ransom Payment from the Victim
After VapeLauncher encrypts the victims' files, VapeLauncher displays a pop-up window in an HTA application named 'VapeLauncher.' The VapeLauncher message displays the following content:
'Your files has been encrypted
[LIST OF ENCRYPTED FILES]
Buy Bitcoins Decrypt Files [TEXT BOX]
The only way you can recover your files is to buy a decryption key
The payment method is Bitcoins. The price is: $200 = Bitcoins
Click on "Buy Decryption key" button'
VapeLauncher demands that the victim pays $200 USD using BitCoins, which allows anonymous payments. C security researchers strongly advise computer users to avoid paying the VapeLauncher ransom.
Dealing with the VapeLauncher Infection
In many cases, con artists will not follow through on their promise to provide the decryption key after the victim pays the ransom. It is also possible that these people will demand additional ransom payments. Most importantly, paying the VapeLauncher ransom allows them to continue carrying out these attacks and financing their activities. Unfortunately, the files that have been encrypted by VapeLauncher are seldom recoverable in their entirety. However, the fact that VapeLauncher only encrypts files partially means that it is possible that malware researchers will release a way to decrypt these files or recover the affected data eventually.
In its current iteration, though, it may be necessary for victims of the VapeLauncher attack to restore the affected files from backup copies. This is, in fact, the best protection against VapeLauncher and other encryption ransomware Trojans. Having backups on an external memory device or the cloud means that computer users can recover their files without needing to pay the ransom, removing any advantage enjoyed by the people responsible for the attack. In the event of an attack, computer users are required to use a reliable security program that is fully up-to-date to remove the VapeLauncher infection itself, and then restore the files from the backup copies.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.