United Kingdom Police Ukash Virus
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | February 11, 2013 |
| Last Seen: | July 23, 2019 |
| OS(es) Affected: | Windows |
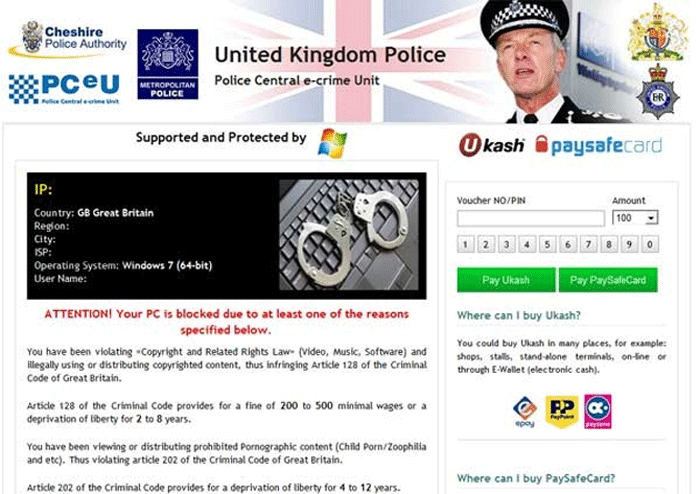
United Kingdom Police Ukash Virus Image
The United Kingdom Police Ukash Virus is one of the many variants of the Reveton Trojan, a dangerous ransomware Trojan that has been responsible for variants of the same scam all around the world. European variants of this Trojan, like the United Kingdom Police Ukash Virus, use the Ukash money transfer service in order to charge their victims while North American variants tend to use MoneyPak for these kinds of scams. It is important to note that MoneyPak and Ukash are both a genuine money transfer deliverance that are not directly associated with malware like the United Kingdom Police Ukash Virus. In fact, if you have made the mistake of paying these ransomware Trojans' ransoms, you can often receive a refund from these companies if you report the scam immediately.
Table of Contents
How the United Kingdom Police Ukash Virus Is Distributed into Its Victims’ Computers
There are several ways in which criminals distribute the United Kingdom Police Ukash Virus. The following methods are the most common ways of distributing this dangerous ransomware Trojan:
- The United Kingdom Police Ukash Virus may be installed on a computer that has been directed to an attack website, which may use an exploit kit (such as the infamous Black Hole Exploit Kit) to take advantage of vulnerabilities in the victim's computer in order to infect it with malware.
- Attack websites are not the only ones that pose a threat. Legitimate, normally harmless websites may be compromised by criminals. By taking advantage of weak passwords or outdated software, criminals may insert malicious scripts into these websites which then distribute malware to computer users visiting the affected website.
- The United Kingdom Police Ukash Virus is often distributed through spam email messages containing malicious attachments or embedded links, which then point to websites used to infect visitors' computers.
- Like most Trojans, the United Kingdom Police Ukash Virus is often downloaded directly by the victim, who has been made to think that the United Kingdom Police Ukash Virus is actually a harmless file containing a particularly popular file in a file sharing website or an innocuous freeware application.
Like most ransomware Trojans, the United Kingdom Police Ukash Virus displays a bogus message from the police. This message accuses you of numerous criminal activities, which include viewing illegal pornographic content and distributing copyrighted material illegally. The United Kingdom Police Ukash Virus blocks access to the victim's computer and threatens the victim with prosecution unless a fine of one hundred pounds is paid within 72 hours.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | C:\ProgramData\[RANDOM CHARACTERS].plz | |
| 2. | C:\ProgramData\[RANDOM CHARACTERS].ctrl | |
| 3. | C:\ProgramData\[RANDOM CHARACTERS].pff |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.