Reveton
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 112 |
| First Seen: | February 23, 2012 |
| Last Seen: | December 3, 2020 |
| OS(es) Affected: | Windows |
 Reveton, also detected as Trojan:Win32/Reveton.A is a malicious Trojan that hijacks the victim's web browser in order to direct the infected computer to specific websites. The Reveton Trojan modifies the Windows Registry that allows Reveton to launch automatically when Windows starts up. Reveton will be disguised as a legitimate file process, making Reveton difficult to remove. Because Reveton makes dangerous changes that must be undone, ESG malware analysts discourage manual removal when dealing with this threat. Instead, Reveton should be removed with a strong anti-malware tool. Since the Reveton Trojan will usually be part of a larger malware attack on your computer, it is also a good idea to scan the infected computer's hard drives with an updated anti-malware scanner.
Reveton, also detected as Trojan:Win32/Reveton.A is a malicious Trojan that hijacks the victim's web browser in order to direct the infected computer to specific websites. The Reveton Trojan modifies the Windows Registry that allows Reveton to launch automatically when Windows starts up. Reveton will be disguised as a legitimate file process, making Reveton difficult to remove. Because Reveton makes dangerous changes that must be undone, ESG malware analysts discourage manual removal when dealing with this threat. Instead, Reveton should be removed with a strong anti-malware tool. Since the Reveton Trojan will usually be part of a larger malware attack on your computer, it is also a good idea to scan the infected computer's hard drives with an updated anti-malware scanner.
Table of Contents
Why Criminals Use the Reveton Trojan to Control Your Online Activity
The main component of a Reveton Trojan attack involves forcing the victim's computer to visit malicious websites. Other symptoms may be present due to the effects of other malware components associated with the Reveton Trojan. ESG malware analysts have compiled the following list of common symptoms associated with Reveton Trojan activity in order to allow computer users to detect the presence of this threat on their computers:
- The Reveton Trojan has been associated with browser redirects taking computer users to attack websites, phishing websites or websites promoting known scams (such as rogue security programs). Phishing websites and attack websites may not be immediately apparent, so caution should be taken whenever your web browser forces you to visit a website without your authorization.
- The Reveton Trojan has also been known to block websites dealing with computer security or promoting legitimate anti-virus products. Whenever the victim tries to visit these websites, they will be greeted with an error message claiming that these websites are infected with malware. In some cases, the Reveton Trojan will simply direct the victim to another web page.
- Malware like the Reveton Trojan seldom plays well with other applications and will often hog your computer's resources. Because of this, a common symptom of a Reveton Trojan infection is poor system performance, frequent system and application crashes, and poor connection speed.
ESG malware analysts have observed that the Reveton Trojan has been present along with rootkit infections as well as with known ransomware attacks. It has also been used to distribute rogue security software from the FakeVimes and VirusDoctor families of malware.
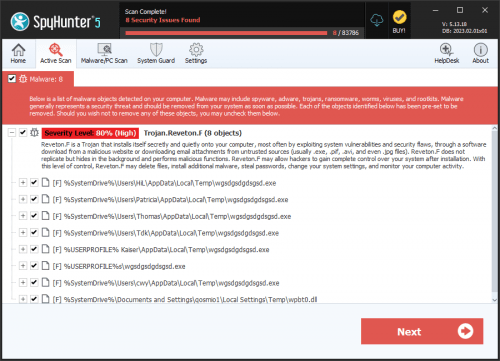
SpyHunter Detects & Remove Reveton
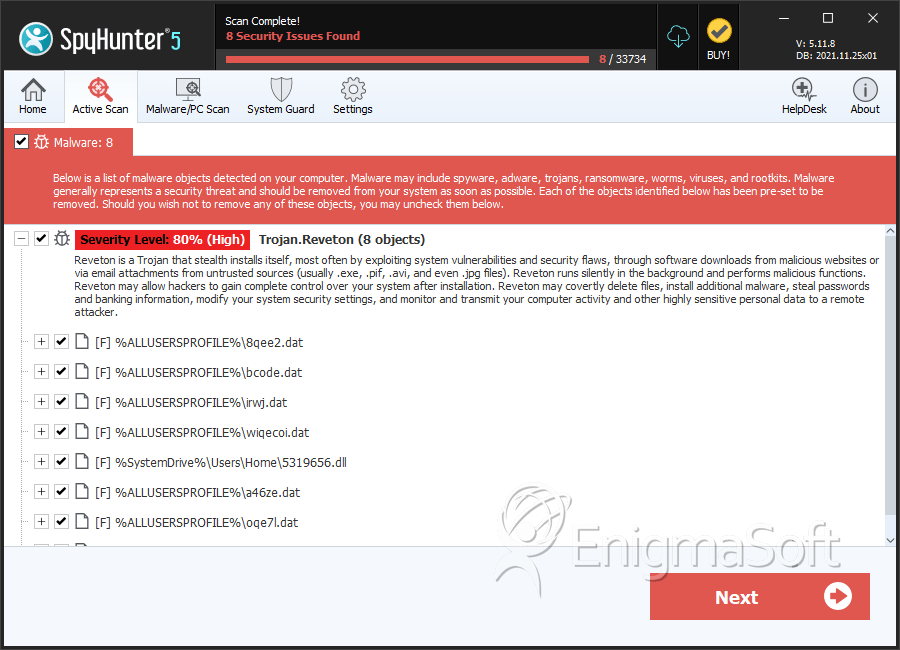
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 8qee2.dat | 347ec4535f27cbf943dd1c962025aa1b | 4 |
| 2. | bcode.dat | d3fbef9502ebcf2d4aff654e9db2467d | 4 |
| 3. | irwj.dat | 0b5a7ca9b16ea1002dccf826abdc9f16 | 3 |
| 4. | wiqecoi.dat | fc8f697b164e025f9e3e08f926a1f6f8 | 3 |
| 5. | 5319656.dll | 71c6c98f2808d3787e86e16764bb3343 | 2 |
| 6. | a46ze.dat | d24671ac9318f18c3b2435c1e3ef4709 | 2 |
| 7. | oqe7l.dat | 037c13babf93065426de07a155e985cd | 2 |
| 8. | 6941006.dll | 98b525d17cfe9c1155be083148bf01be | 1 |
| 9. | 5673474.dll | 673b8caf1e29058094bd8273b24f803b | 1 |
| 10. | 3WsIMd3.exe | cd7eaa7b69f01bab0f6dee939facabba | 1 |
| 11. | wpbt0.dll | b5d99dc7243033b4b0a6cd76ed20e04d | 1 |
| 12. | bl0b.dat | fcc68b087076a2cc935f2073b7befa97 | 1 |
| 13. | tocolb.dat | f5a1364d6f7154ee3f5fa5a44c419f7b | 1 |
| 14. | vjezdjm.dat | dbbdbb9664f7acc769fc441f7ef6e151 | 1 |
| 15. | ijewido.dat | 4825e40eb19713133c4561b94e8ca598 | 1 |
| 16. | 6zldto.dat | b07f1e55adbed6af1d87be8fee50bd25 | 1 |
| 17. | j1aa.dat | 7fde75f7fc571aa1446a65d72084ccab | 1 |
| 18. | 034ni.dat | 10249aaa09516a5cfdb1ff22a4da6cb1 | 1 |
| 19. | 3foid.dat | 4c85ed28eb4ac442cf0601e0a77e1383 | 1 |
| 20. | fv3a.dat | 531369ac91993675eec379ecc848ccbc | 1 |
| 21. | 2ni6zb.dat | b6850b73e679e709bb5c12e79ba2549f | 1 |
| 22. | fowidoje.dat | 22a581545f904ee72a2bbb3b60a7408a | 1 |
| 23. | zdrifo1.dat | 69bd66ab75ce15b07945ae41ad65be1d | 1 |
| 24. | llo0g.dat | ac49d31165d10e81b977a44d9ffec7ee | 1 |
| 25. | 0wiriri.dat | 3bd398ab9c27862c2694787b2be24a27 | 1 |
| 26. | nijwi7.dat | db96cdef4b146cbf005ec5f49b32d01e | 1 |
| 27. | zdnidr.dat | d0d4acde777b2a0328f57075dc244c3e | 1 |
| 28. | KapoBome.ggq | dbe82982d88130ee354aaa4fdd393645 | 1 |