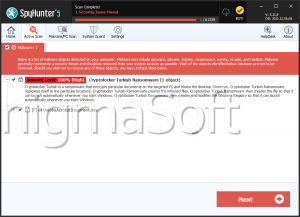
Turkish Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 109 |
| First Seen: | March 16, 2017 |
| Last Seen: | October 5, 2022 |
| OS(es) Affected: | Windows |
The Turkish Ransomware is a ransomware Trojan that has only been observed in a version in Turkish. PC security researchers first received reports of the Turkish Ransomware on March 15, 2017. The Turkish Ransomware is designed to attack computers using Windows and located in Europe. The Turkish Ransomware seems to be a one-off attack and does not seem to have variants or belong to a broader family of ransomware Trojans (although much of its code is recycled, as it happens with most of these attacks). Although the Turkish Ransomware can be delivered in a wide variety of ways, it is likely that the Turkish Ransomware attacks are being distributed through the use of corrupted links and attachments contained in spam email messages currently.
Table of Contents
The Turkish Ransomware may Cause a Lot of Harm
The Turkish Ransomware is typical ransomware Trojan that carries out an attack similar to most other encryption ransomware Trojans active in the last year. The Turkish Ransomware uses the AES-256 encryption to make the victim's files completely inaccessible. The files encrypted using this encryption method become completely unrecoverable without access to the decryption key, which the con artists keep in their possession. During the Turkish Ransomware attack, the files compromised will be identified by the addition of the extension '.encrypted' to the ending of each affected file's name. Once the Turkish Ransomware encrypts a file, it becomes completely unreadable and may appear on Windows as a blank icon. During its attack the Turkish Ransomware will encrypt the following types of files:
.3GP, .7Z, .APK, .AVI, .BMP, .CDR, .CER, .CHM, .CONF, .CSS, .CSV, .DAT, .DB, .DBF, .DJVU, .DBX, .DOCM, ,DOC, .EPUB, .DOCX .FB2, .FLV, .GIF, .GZ, .ISO .IBOOKS,.JPEG, .JPG, .KEY, .MDB .MD2, .MDF, .MHT, .MOBI .MHTM, .MKV, .MOV, .MP3, .MP4, .MPG .MPEG, .PICT, .PDF, .PPS, .PKG, .PNG, .PPT .PPTX, .PPSX, .PSD, .RAR, .RTF, .SCR, .SWF, .SAV, .TIFF, .TIF, .TBL, .TORRENT, .TXT, .VSD,.WMV, .XLS, .XLSX, .XPS, .XML, .CKP, .ZIP, .JAVA, .PY, .ASM, .C, .CPP, .CS, .JS, .PHP, .DACPAC, .RBW, .RB, .MRG, .DCX, .DB3, .SQL, .SQLITE3, .SQLITE, .SQLITEDB, .PSD, .PSP, .PDB, .DXF, .DWG, .DRW, .CASB, .CCP, .CAL, .CMX, .CR2.
The Turkish Ransomware Doesn’t Need an Internet Connection to Carry Out Its Attack
The Turkish Ransomware, unlike many encryption ransomware Trojans, does not need to be connected to the Internet to carry out its attack. After the Turkish Ransomware encrypts the victim's files, the Turkish Ransomware drops several files on the victim's computer. These files, 'Beni Oku.txt' (Readme .txt), 'images.xml,' 'publickKey.xml,' and 'privatekey.xm,' are dropped in the Documents directory. The Turkish Ransomware's lock screen is contained in a file named 'images.xml,' which appears after the encryption has been carried out. The text file contains the following message for the victim:
'1 - To remove the encryption on your files, you need to send bitcoin to the address of 13HP68KeuvocU7hvlf7XQMEox8DPR8odx5 bitcoin priced at 150 USD. After you pay :
2 - 150 USD, please send the privateKey.XML file located within the My Documents folder to d3cryptOr@lelantos.org. After sending the required file, your files will be sent the appropriate decryption key and you will open decrypt your files.
3 - Bitcoin purchases can be done via https://localbitcoins.com/ and other similar sites.
4 - Trying to find the password for your files will only cause damage to your files and cause data loss.
Within 24 hours, unencrypted files will be deleted automatically so that they will not be recoverable on your hard disk.
6 - For more information, you can send an email to d3crypt0r@lelantos.org.'
Dealing with the Turkish Ransomware
Computer users must avoid paying the Turkish Ransomware ransom. Computer users should have backup copies of all files to ensure that there is no need to pay the ransom. If PC users can recover their files from a backup, then the con artists lose all power to demand ransom payments from the victim. A reliable security program should be used to remove the Turkish Ransomware infection itself from the victim's computer.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.