TSPY_ZBOT.FAZ
ESG security researchers have identified a ZBOT variant named TSPY_ZBOT.FAZ found in a Facebook scam. This variant of ZBOT has a way of generating the domain from which it downloads TSPY_ZBOT.FAZ's configuration file, making a preset URL very difficult to block. ESG security researchers advise staying alert for suspicious Facebook friend notifications or other kinds of messages. Even though Facebook in itself is not associated with malware, many hackers have found ways to take advantage of different security holes in this social network. A fully-updated anti-malware program should remove most known ZBOT variants. However, only the latest malware database updates will contain ways to fight TSPY_ZBOT.FAZ's domain generation techniques.
The TSPY_ZBOT.FAZ scam will usually appear initially as a fake friend request on Facebook. Unlike normal friend requests, this message will contain a malicious link. This link will be labeled as 'Approve Friend Request'. However, experienced Facebook users will quickly recognize the difference between this friend request and the real thing. When this link is clicked, it leads the user to a page that claims that the Adobe Flash Player needs to be updated or installed. This fake update for Adobe Flash is really TSPY_ZBOT.FAZ. This is why ESG security researchers strongly recommend that all updates come directly from the software's manufacturer, and never from a third party. The case of the TSPY_ZBOT.FAZ infection is a typical illustration of how malware can disguise itself as software updates from a third party.
Table of Contents
How TSPY_ZBOT.FAZ Uses Domain Generation Techniques to Contact a Remote Server
Most ZBOT variants need to connect to a remote server to download their configuration data. This usually takes the form of a configuration file with a list of websites that TSPY_ZBOT.FAZ will monitor to steal passwords, personal identification numbers, and other sensitive information. While this connection to a remote server can often be blocked with a legitimate anti-malware program, the TSPY_ZBOT.FAZ ZBOT variant uses a domain-generation algorithm that allows TSPY_ZBOT.FAZ to gain access to a random URL to download this configuration data. This makes blocking this connection more difficult than normal. TSPY_ZBOT.FAZ uses the computer's date as a seed number to randomize the domain TSPY_ZBOT.FAZ generates.
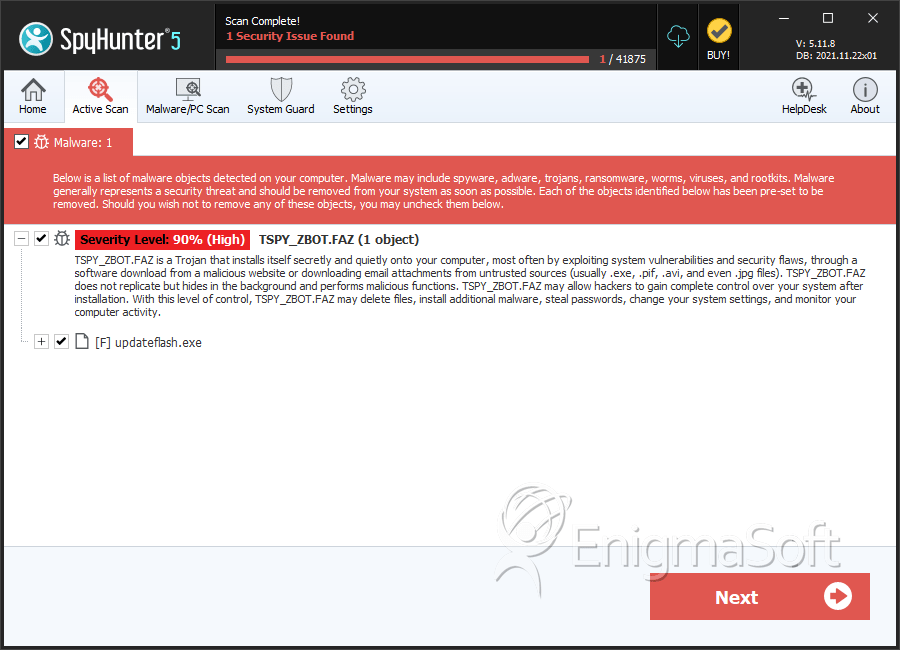
SpyHunter Detects & Remove TSPY_ZBOT.FAZ
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | %Application Data%\{RANDOM CHARACTERS1}\{RANDOM CHARACTERS}.exe | ||
| 2. | %Application Data%\{RANDOM CHARACTERS2}\{RANDOM CHARACTERS}. | ||
| 3. | updateflash.exe | 6f86e5939e7bca1d0a57689e6d4e3e57 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.