TSPY_FAREIT.ACU
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 3 |
| First Seen: | June 28, 2013 |
| Last Seen: | November 18, 2019 |
| OS(es) Affected: | Windows |
TSPY_FAREIT.ACU is a dangerous spy Trojan that has made headlines because TSPY_FAREIT.ACU uses a security certificate stolen from the developers of the popular Opera Web browser. Opera's website was hacked and the stolen security certificate was then used in a malware attack that targeted thousands of computer users. This breach came about as a consequence of a 'targeted attack on the internal network infrastructure', according to a company spokesman. Through this attack, criminals were able to get their hands on an expired Opera signing certificate which has been used in TSPY_FAREIT.ACU. This is particularly dangerous because now TSPY_FAREIT.ACU appears as if TSPY_FAREIT.ACU was published by the makers of the Opera browser, Opera Software. The real danger in this attack is that between 1AM and 1:36AM UTC the day of the attack, which was June 19th, TSPY_FAREIT.ACU may have been sent automatically to thousands of computer users.
Table of Contents
What to Do If You Were Exposed to TSPY_FAREIT.ACU After the Opera Breach
If you use the Opera Web browser and suspect that you were exposed to TSPY_FAREIT.ACU, ESG security researchers advise taking the following steps:
- Remove Opera from your computer, uninstalling it and deleting its files.
- Use a reliable anti-malware program that has been completely updated to scan your computer.
- Delete and found malware files. TSPY_FAREIT.ACU has been associated with ransomware attacks and spy Trojans, all of which are also using the stolen Opera certificate.
- Once you have disinfected your computer, it is safe to reinstall the Opera Web browser or to switch to another of the top alternatives on the market.
Other Infections Installed by TSPY_FAREIT.ACU Using the Opera Security Breach
TSPY_FAREIT.ACU stores passwords and other private information saved in your applications, including email clients, FTP clients and Web browsers. This data is then sent to a remote server in order to steal your money or hack into your online accounts. TSPY_FAREIT.ACU also connects to a remote server in order to download and install other malware onto your computer. So far, TSPY_FAREIT.ACU installs three other malware infections:
- TR.Ransom.GQ.1: a dangerous Police Ransomware Trojan that blocks access to infected computer systems in order to demand a ransom from the computer user.
- TR/Kazy.adag: a Trojan designed to steal information from the infected computer.
- Bds/ZAccess.BS: a Zeus Trojan variant that allows criminals to gain access to your computer and to your private information, establishing a dangerous backdoor that gives a third party full access to the infected computer.
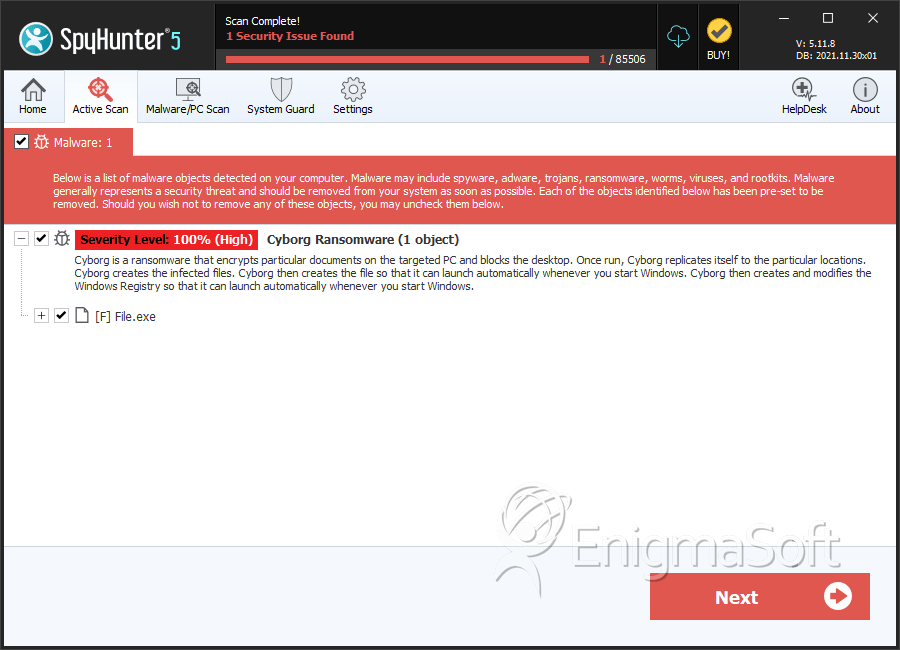
SpyHunter Detects & Remove TSPY_FAREIT.ACU
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | File.exe | a9750200274a60c274312c30f57c24d1 | 1 |
| 2. | file.exe | 74bfab32741f15b9fcfb32aacffab584 | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.