TrumpLocker Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 73 |
| First Seen: | February 22, 2017 |
| Last Seen: | May 2, 2022 |
| OS(es) Affected: | Windows |
The TrumpLocker Ransomware is a ransomware Trojan that receives its name because it features an image of the United States President Donald Trump as part of its ransom note. The TrumpLocker Ransomware is simply a repackaged version of VenusLocker, a known ransomware family that has been around since August of 2016 and was last updated in December of 2016. At the moment, it is not certain whether the same team responsible for VenusLocker is responsible for the TrumpLocker Ransomware attacks or if this threat was co-opted by a third-party.
Table of Contents
The Controversial Name of a Ransomware
The TrumpLocker Ransomware uses an executable file named TrumpLocker.exe, which encrypts the victim's files. Although it is not certain how the TrumpLocker Ransomware is being distributed to its victims, it is highly likely that the distribution method involves the use of corrupted email attachments since this is the most commonly used method to distribute malware of this kind. As soon as the TrumpLocker Ransomware is installed, it connects to its Command and Control server. The TrumpLocker Ransomware carries out its attack by encrypting the victim's files and then demanding the payment of a ransom. At the moment, the TrumpLocker Ransomware demands the payment of 0.145 BitCoin, which is approximate $165 USD at the current exchange rate.
How the TrumpLocker Ransomware may Attack a Computer
The encryption routine associated with the TrumpLocker Ransomware is slightly different from other ransomware Trojans. The TrumpLocker Ransomware encrypts the full contents of only certain file types. In other cases, it will only encrypt the first 1024 bytes of the affected file. This is a behavior that also is typical of the thrat in the VenusLocker family. The files encrypted by the TrumpLocker Ransomware will receive the extension '.TheTrumpLockerf.' The TrumpLocker Ransomware fully encrypts the following file types:
.txt, .ini, .php, .html, .css, .py, .c, .cpp, .cc, .h, .cs, .log, .pl, .java, .doc, .dot, .docx, .docm, .dotx, .dotm, .rtf, .wpd, .docb, .wps, .msg, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .class, .jar, .csv, .xml, .dwg, .dxf, .asp.
However, the file types below are only encrypted partially during a the TrumpLocker Ransomware attack:
.asf, .pdf, .xls, .docx, .xlsx, .mp3, .waw, .jpg, .jpeg, .txt, .rtf, .doc, .rar, .zip, .psd, .tif, .wma, .gif, .bmp, .ppt, .pptx, .docm, .xlsm, .pps, .ppsx, .ppd, .eps, .png, .ace, .djvu, .tar, .cdr, .max, .wmv, .avi, .wav, .mp4, .pdd, .php, .aac, .ac3, .amf, .amr, .dwg, .dxf, .accdb, .mod, .tax2013, .tax2014, .oga, .ogg, .pbf, .ra, .raw, .saf, .val, .wave, .wow, .wpk, .3g2, .3gp, .3gp2, .3mm, .amx, .rpt, .avs, .bik, .dir, .divx, .dvx, .evo, .flv, .qtq, .tch, .rts, .rum, .rv, .scn, .srt, .stx, .svi, .swf, .trp, .vdo, .wm, .wmd, .wmmp, .wmx, .wvx, .xvid, .3d, .3d4, .3df8, .pbs, .adi, .ais, .amu, .arr, .bmc, .bmf, .cag, .cam, .dng, .ink, .ini, .jif, .jiff, .jpc, .jpf, .jpw, .mag, .mic, .mip, .msp, .nav, .ncd, .odc, .odi, .opf, .qif, .xwd, .abw, .act, .adt, .aim, .ans, .asc, .ase, .bdp, .bdr, .bib, .boc, .crd, .diz, .dot, .dotm, .dotx, .dvi, .dxe, .mlx, .err, .euc, .faq, .fdr, .fds, .gthr, .idx, .kwd, .lp2, .ltr, .man, .mbox, .msg, .nfo, .now, .odm, .oft, .pwi, .rng, .rtx, .run, .ssa, .text, .unx, .wbk, .wsh, .7z, .arc, .ari, .arj, .car, .cbr, .cbz, .gz, .gzig, .jgz, .pak, .pcv, .puz, .rev, .sdn, .sen, .sfs, .sfx, .sh, .shar, .shr, .sqx, .tbz2, .tg, .tlz, .vsi, .wad, .war, .xpi, .z02, .z04, .zap, .zipx, .zoo, .ipa, .isu, .jar, .js, .udf, .adr, .ap, .aro, .asa, .ascx, .ashx, .asmx, .asp, .indd, .asr, .qbb, .bml, .cer, .cms, .crt, .dap, .htm, .moz, .svr, .url, .wdgt, .abk, .bic, .big, .blp, .bsp, .cgf, .chk, .col, .cty, .dem, .elf, .ff, .gam, .grf, .h3m, .h4r, .iwd, .ldb, .lgp, .lvl, .map, .md3, .mdl, .nds, .pbp, .ppf, .pwf, .pxp, .sad, .sav, .scm, .scx, .sdt, .spr, .sud, .uax, .umx, .unr, .uop, .usa, .usx, .ut2, .ut3, .utc, .utx, .uvx, .uxx, .vmf, .vtf, .w3g, .w3x, .wtd, .wtf, .ccd, .cd, .cso, .disk, .dmg, .dvd, .fcd, .flp, .img, .isz, .mdf, .mds, .nrg, .nri, .vcd, .vhd, .snp, .bkf, .ade, .adpb, .dic, .cch, .ctt, .dal, .ddc, .ddcx, .dex, .dif, .dii, .itdb, .itl, .kmz, .lcd, .lcf, .mbx, .mdn, .odf, .odp, .ods, .pab, .pkb, .pkh, .pot, .potx, .pptm, .psa, .qdf, .qel, .rgn, .rrt, .rsw, .rte, .sdb, .sdc, .sds, .sql, .stt, .tcx, .thmx, .txd, .txf, .upoi, .vmt, .wks, .wmdb, .xl, .xlc, .xlr, .xlsb, .xltx, .ltm, .xlwx, .mcd, .cap, .cc, .cod, .cp, .cpp, .cs, .csi, .dcp, .dcu, .dev, .dob, .dox, .dpk, .dpl, .dpr, .dsk, .dsp, .eql, .ex, .f90, .fla, .for, .fpp, .jav, .java, .lbi, .owl, .pl, .plc, .pli, .pm, .res, .rsrc, .so, .swd, .tpu, .tpx, .tu, .tur, .vc, .yab, .aip, .amxx, .ape, .api, .mxp, .oxt, .qpx, .qtr, .xla, .xlam, .xll, .xlv, .xpt, .cfg, .cwf, .dbb, .slt, .bp2, .bp3, .bpl, .clr, .dbx, .jc, .potm, .ppsm, .prc, .prt, .shw, .std, .ver, .wpl, .xlm, .yps, .1cd, .bck, .html, .bak, .odt, .pst, .log, .mpg, .mpeg, .odb, .wps, .xlk, .mdb, .dxg, .wpd, .wb2, .dbf, .ai, .3fr, .arw, .srf, .sr2, .bay, .crw, .cr2, .dcr, .kdc, .erf, .mef, .mrw, .nef, .nrw, .orf, .raf, .rwl, .rw2, .r3d, .ptx, .pef, .srw, .x3f, .der, .pem, .pfx, .p12, .p7b, .p7c, .jfif, .exif, .docb, .xlt, .xltm, .xlw, .ppam, .sldx, .sldm, .class, .db, .pdb, .dat, .csv, .xml, .spv, .grle, .sv5, .game, .slot, .aaf, .aep, .aepx, .plb, .prel, .prproj, .eat, .ppj, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .svg, .as3, .as.
This encryption method may allow the TrumpLocker Ransomware to carry out its encryption routine faster. The TrumpLocker Ransomware will not encrypt the files located in the following directories:
Program Files, Program Files (x86), Windows, Python27, Python34, AliWangWang, Avira, wamp, Avira, 360, ATI, Google, Intel, Internet Explorer, Kaspersky Lab, Microsoft Bing Pinyin, Microsoft Chart Controls, Microsoft Games, Microsoft Office, Microsoft.NET, MicrosoftBAF, MSBuild, QQMailPlugin, Realtek, Skype, Reference Assemblies, Tencent, USB Camera2, WinRAR, Windows Sidebar, Windows Portable Devices, Windows Photo Viewer, Windows NT, Windows Media Player, Windows Mail, NVIDIA Corporation, Adobe, IObit, AVAST Software, CCleaner, AVG, Mozilla Firefox, VirtualDJ, TeamViewer, ICQ, Java, Yahoo!
The TrumpLocker Ransomware’s Ransom Note
The TrumpLocker Ransomware demands the payment of a ransom from its victims by dropping a ransom note on the targeted computer. The TrumpLocker Ransomware's ransom note is contained in a text file named 'What happen to my files.txt,' which will be located on the infected computer's Desktop. Apart from the text file ransom note, the TrumpLocker Ransomware also will execute an executable file named 'RansomNote.exe.', which displays an image of Donald Trump, accompanied by the text 'YOU ARE HACKED!!'
The full text of the TrumpLocker Ransomware's ransom note is similar to the ones displayed by VenusLocker variants:
--- The Trump Locker ---
Unfortunately, you are hacked.
1. What happened to my files?
Your personal files, including your photos, documents, videos and other important files on this computer, have been encrypted with RSA-4096, the strongest encryption algorithm. RSA algorithm generates a public key and a private key for your computer. The public key was used to encrypt your files a moment ago. The private key is necessary for you to decrypt and recover your files. Now, your private key is stored on our secret Internet server. And there is no doubt that no one can recover your files without your private key.
For further information about RSA algorithm, please refer to https://en.wikipedia.org/wiki/RSA_(cryptosystem)
2. How to decrypt my files?
To decrypt and recover your files, you have to pay #ramt# US Dollars for the private key and decryption service. Please note that you have ONLY 72 HOURS to complete your payment. If your payment do not be completed within time limit, your private key will be deleted automatically by our server. All your files will be permanently encrypted and nobody can recover them. Therefore, it is advised that you'd better not waste your time, because there is no other way to recover your files except making a payment.
3. How to pay for my private key?
There are three steps to make a payment and recover your files:
1). For the security of transactions, all the payments must be completed via Bitcoin network. Thus, you need to exchange #ramt# US dollars (or equivalent local currencies) to Bitcoins, and then send these Bitcoins (about #btc# BTC) to the following address. 1N82pq3XovKoJYqUmTrRiXftpNHZyu4jyv
2). Send your personal ID to our official email: TheTrumpLocker@mail2tor.com
Your personal ID is: #id#
3). You will receive a decryptor and your private key to recover all your files within one working day.
4. What is Bitcoin?
Bitcoin is an innovative payment network and a new kind of money. It is based on an open-source cryptographic protocol that is independent of any central authority. Bitcoins can be transferred through a computer or a smartphone withour an intermediate financial institution.
5. How to make a payment with Bitcoin?
You can make a payment with Bitcoin based on Bitcoin Wallet or Based on Perfect Money. You can choose the way that is more convenient for you.
About Based on Bitcoin Wallet
1) Create a Bitcoin Wallet. We recommend Blockchain.info (https://blockchain.info/)
2) Buy necessary amount of Bitcoins. Our recommendations are as follows.
LocalBitcoins.com -- the fastest and easiest way to buy and sell Bitcoins.
CoinCafe.com -- the simplest and fastest way to buy, sell and use Bitcoins.
BTCDirect.eu -- the best for Europe.
CEX.IO -- Visa / MasterCard
CoinMama.com -- Visa / MasterCard
HowToBuyBitcoins.info -- discover quickly how to buy and sell Bitcoins in your local currency.
3) As mentioned above, send about #btc# BTC (equivalent to #ramt# USD) to our Bitcoin receiving address.
4) As mentioned above, and then, send us your personal ID via email, you will receive your private key soon.
About Based on Perfect Money
1) Create a Perfect Money account. (https://perfectmoney.is)
2) Visit to PMBitcoin.com. (https://pmbitcoin.com/btc)
input our Bitcoin receiving address in the \"Bitcoin Wallet\" textbox.
input #ramt# in the \"Amount\" textbox, the amount of Bitcoin will be calculated automatically.
click \"PAY\" button, then you can complete you payment with your Perfect Money account and local debit card.
6. If you have any problem, please feel free to contact us via official email.
Best Regards
The Trump Locker Team
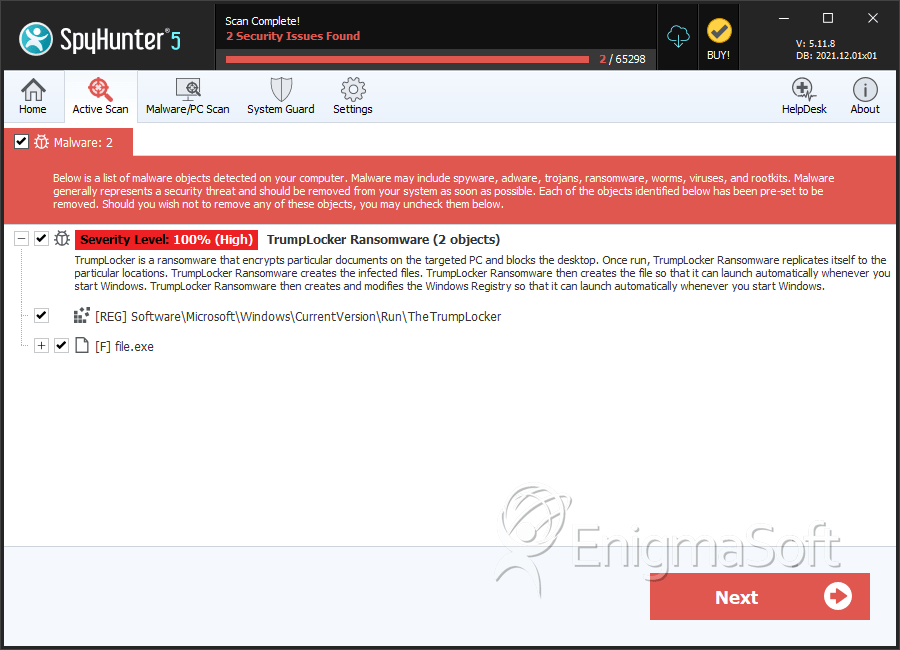
SpyHunter Detects & Remove TrumpLocker Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | c6210a32147375a819ddfb586230ddd1 | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.