Trojan.Llac
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 232 |
| First Seen: | April 22, 2011 |
| Last Seen: | May 22, 2023 |
| OS(es) Affected: | Windows |
Trojan.Llac is a detection for a particular piece of malware that is a Trojan-Downloader specialized in using misappropriated digital certificates to infiltrate systems and install other threats undetected. The Llac Trojan-Downloader may use misappropriated digital certificates from Chinese companies and is associated with potent cryptomalware like the TorrentLocker Ransomware. Trojan.Llac is similar to TrojanDownloader:Win32/Filcout and TrojanDownloader:MSIL/Winpud and may download encrypted payload of other harmful programs via HTTP channels that may be used by most IM clients and Web browsers. The Llac threatening program may increase the boot time of infected machines to install harmful code before the system is fully operational and bypass real-time protection mechanisms. The modus operandi of the Llac Trojan downloader is crafted to allow it to run as a portable program and seem harmless to AV scanners.
The Trojan.Llac malware may not need to tamper with your system ports and DNS configuration to execute its operations. Malware researchers note that the Llac Trojan downloader may use publicly available encryption libraries to unpack downloaded cyber threats, install them while the PC is hibernating and is in standby mode. Samples of Trojan.Llac suggest that it may be deployed to users via spam email and be enclosed in RAR and ZIP file archives that feature a double file extension and are designed to drop files in the Temp directory. The spam email loaded with the Trojan.Llac executable may be related to social events, invoices, and payment confirmations from online stores like Amazon and eBay. Responsible computer users should not interact with links and attachments from unknown sources. You can clean a computer that is infected with the Llac Trojan-Downloader by installing a reliable anti-malware application and making sure to do a complete scan of all connected hard drives.
Table of Contents
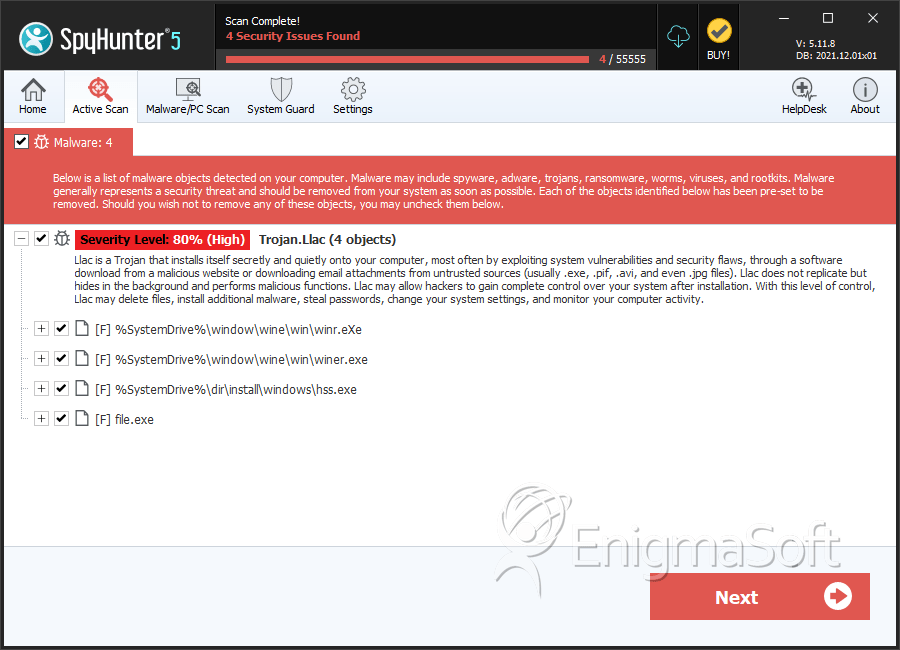
SpyHunter Detects & Remove Trojan.Llac
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | winr.eXe | bfc3e36ae0555859deb31d24a5b8ebed | 76 |
| 2. | winer.exe | f6d3d0197143977ae9dcc3b3f9659e3e | 7 |
| 3. | winr.EXE | 974f140cc277c7538b3899acf3590205 | 4 |
| 4. | hss.exe | 1ed1f7048930c980cd9d3807824a4ce0 | 1 |
| 5. | file.exe | 815805bb2eeaab0b5d9d7e2737964b6a | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.