Trojan.Kasidet
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 9,491 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 2,635 |
| First Seen: | June 22, 2015 |
| Last Seen: | August 18, 2023 |
| OS(es) Affected: | Windows |
Trojan.Kasidet is a generic detection name for a PoS malware a.k.a. Point-of-Sale Trojan that was under surveillance as early as 2015 and was added to most AV databases in 2016. The Trojan.Kasidet was hard to classify as it is a mix of code we have seen in the Dexter Infostealer and the Neutrino Bot. Some malware analysts found similarities with the MWZLesson PoS malware as well. The cyber threats of today are usually equipped to handle various tasks that range from network proliferation and data encryption to fileless spying. Hence, Trojans can have Worm-like features, and Backdoor Trojans can be used for DDoS (Distributed Denial of Service) attacks.
Trojan.Kasidet is known to be dropped to vulnerable PoS stations and poses as a legitimate Microsoft product called 'WMI Commandline Utility by Microsoft.' In many cases, threat actors use SFX-RAR (Self-Extracting Archive) files and social engineering to lure poorly educated PC users into installing malware on their devices. Trojan.Kasidet is observed to scan PoS computers for the following processes:
- prl_cc.exe
- prl_tools.exe
- vboxservice.exe
- vboxtray.exe
- vmsrvc.exe
- vmusrvc.exe
- vmwaretray.exe
- vmwareuser.exe
The threat proceeds to search for the following modules:
- api_log.dll
- dir_watch.dll
- pstorec.dll
- sbiedll.dll
- vmcheck.dll
- wpespy.dll
Trojan.Kasidet reads the information stored on the magnetic line of your debit/credit card and monitors the PoS device for PIN input. As soon as you enter your PIN and the system confirms a successful payment, Trojan.Kasidet sends the collected data to its operators. AV companies found that Trojan.Kasidet may communicate with 'Command and Control' servers on the following addresses:
enotecacattaneo[.]it (62.149.128.151)
lattone[.]com (62.149.128.160)
mondaynightfundarts[.]com (216.18.70.74)
pationare[.]bit (144.76.133.38)
studiolegalecontrini[.]com (62.149.128.74)
usuellialfonso[.]it (62.149.128.160)
valentigomme[.]com (62.149.128.151)
www[.]enotecacattaneo[.]it (31.11.32.73)
www[.]lattone[.]com (31.11.33.18)
www[.]studiolegalecontrini[.]com (31.11.32.88)
www[.]usuellialfonso[.]it (89.46.105.15)
www[.]valentigomme[.]com (31.11.32.119)
You may want to know that Trojan.Kasidet can be used to collect the user’s credentials from Internet clients powered by the Triton, the Gecko and Blink layout engines. That means logins saved in Mozilla Firefox, SeaMonkey Opera, Google Chrome, SRWare Iron, Internet Explorer, Avant Browser and Maxthon can be misappropriated. Also, Trojan.Kasidet is reported to extract logins from email clients such as Outlook, Foxmail, and Thunderbird and send the collected credentials to the following IP addresses:
adika-win-iphone[.]comyr[.]com/god
dlms1[.]ir/php5
cosmeticsurgeryonline[.]in
dev1[.]appsichern[.]de
cosmeticsurgeryonline[.]in/lib
It is advised to purge the Trojan.Kasidet malware with the assistance of a reputable computer security scanner. Advanced computer users and network administrators may be able to pick up on the network transmissions of Trojan.Kasidet and succeed to remove it quickly. AV companies are known to use the following detection names regarding resources created by Trojan.Kasidet:
- Gen:Variant.Zusy.241505
- TR/Crypt.ZPACK.sfpmn
- TROJ_GEN.R047C0DFD17
- Trojan ( 0050fdd41 )
- Trojan-FNAX!3541BA797863
- Trojan/Win32.Kasidet.C2000867
- W32/Kryptik.FTDD!tr
- W32/S-6d307b46!Eldorado
- WORM_HPKASIDET.SM1
Table of Contents
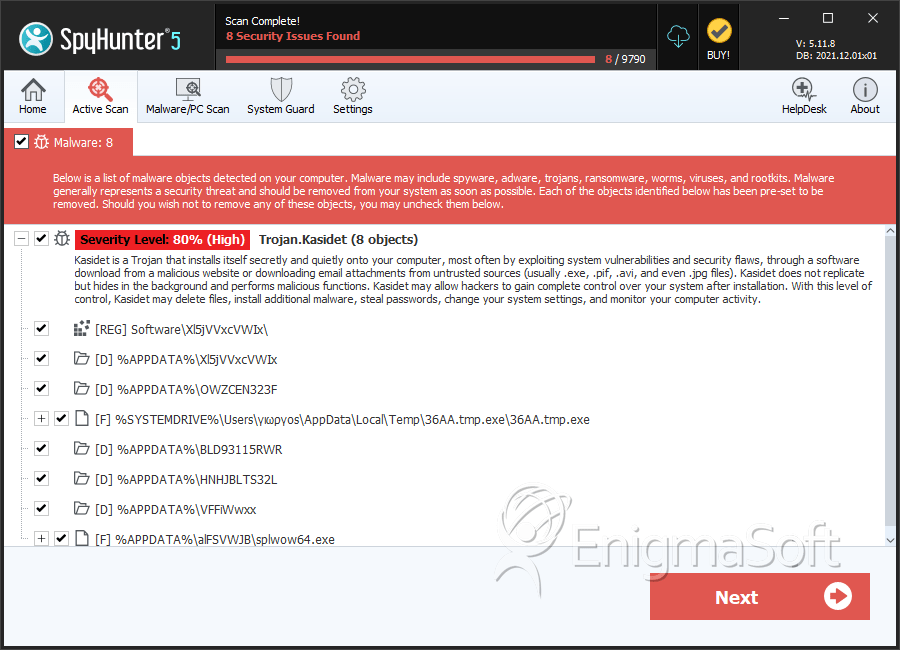
SpyHunter Detects & Remove Trojan.Kasidet
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 36AA.tmp.exe | 2cee541d6254c0c635edf2692fc82c5b | 111 |
| 2. | splwow64.exe | cd603826fe8777ea41012794afc64045 | 46 |
| 3. | jevgr.exe | efd1b86c75ea28ddbb01d3b71b01404c | 43 |
| 4. | regedit.exe | 80f5571b81f24d120e1eb6fde907d869 | 8 |
| 5. | uryccnar.exe | ddd052bab9789dfb0d7a855ab7949987 | 8 |
| 6. | twunk_32.exe | 81382f29fda246b6bd3d9f3a2ade1631 | 7 |
| 7. | regedit.exe | 7ea6a4de5beb54542161d844c604f1ff | 7 |
| 8. | twunk_32.exe | 07bde80d2ab1e19b2bd6836fb11b0919 | 7 |
| 9. | twunk_32.exe | 6c9e6c3a08b9c008c7e96a825553116f | 6 |
| 10. | splwow64.exe | ee67a380f20bcc2ce44fbd4457c1f0a1 | 4 |
| 11. | regedit.exe | 939b1ed7bd72e5753264a44f59a61f43 | 4 |
| 12. | splwow64.exe | 6dbae4517e375e1e276a7fd371b3b166 | 3 |
| 13. | jevgr.exe | a62ef9a11a3e9a0952d88862997b5800 | 3 |
| 14. | regedit.exe | c2aa413e32a9b35cc9f4c8b580aabb9b | 2 |
| 15. | splwow64.exe | 5fda0d16e145423f0d8435f68514bed0 | 2 |
| 16. | splwow64.exe | fd935448f6f1f6e7d0b304d9fc08fbb7 | 2 |
| 17. | splwow64.exe | 75fd8ec84340fd7ab108cbe41acf94f8 | 2 |
| 18. | splwow64.exe | ba0786ada0941f98e24c8cf250e81e9a | 2 |
| 19. | regedit.exe | cd376806c4e93b9a1ff903cb0f8a104e | 2 |
| 20. | jevgr.exe | b4f56e58b968b787c4b680f3a67fad6d | 2 |
| 21. | regedit.exe | 417109a7c6fb3c0da95c4028239bb757 | 1 |
| 22. | jevgr.exe | 14116f749eefb9f2f8574b856d67105e | 1 |
| 23. | uryccnar.exe | 34f312e9096e01b862f538d018b18051 | 1 |
| 24. | uryccnar.exe | d1fbc4c7cb3c51ef295d834b5cc275ed | 1 |
| 25. | file.exe | e575ebf04f85acc5d2f5dbc9270ca6ff | 0 |
Registry Details
Directories
Trojan.Kasidet may create the following directory or directories:
| %APPDATA%\3600540-NN |
| %APPDATA%\4059116-NN |
| %APPDATA%\4MPMMXI-NIF |
| %APPDATA%\4ZBR19116-NNIF |
| %APPDATA%\AAN-DUPKSPPO |
| %APPDATA%\BLD93115RWR |
| %APPDATA%\DDS-NTDTSPJSBPO |
| %APPDATA%\HNHJBLTS32L |
| %APPDATA%\OWZCEN323F |
| %APPDATA%\RRTW-OEXPEXOBM |
| %APPDATA%\UVhVXmJpX2Ax |
| %APPDATA%\UVxRXkE= |
| %APPDATA%\UmVpQUJD |
| %APPDATA%\VFFiWwxx |
| %APPDATA%\VFRfY15VZEE |
| %APPDATA%\W2VTWFFiQQ== |
| %APPDATA%\WlVjY2kx |
| %APPDATA%\XWljZFlTUVxcXFxc |
| %APPDATA%\XkNlZGJZXl8x |
| %APPDATA%\Xl5jVVxcVWIx |
| %APPDATA%\Y2BfYmRgYl8x |
| %APPDATA%\ZBR-JNSEXOBM |
| %APPDATA%\ZlFZQkBA |

