The Brotherhood Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 4 |
| First Seen: | July 19, 2018 |
| Last Seen: | February 18, 2022 |
| OS(es) Affected: | Windows |
The Brotherhood Ransomware is an encryption ransomware Trojan based on HiddenTear. This is a ransomware platform that was released initially as an open source program in 2015. Today, most ransomware Trojans are based on HiddenTear in some way, and The Brotherhood Ransomware is no exception. The Brotherhood Ransomware was first observed on July 3, 2018, and it carries out a typical version of the HiddenTear attack, with the ability to carry out an offline version of the ransomware attack, without communicating with a Command and Control server.
Table of Contents
The Ransomware’s Name that should be the Brotherhood of Extortionists
The Brotherhood Ransomware works by encrypting the victim's files. The Brotherhood Ransomware uses a strong encryption algorithm, the AES 256, which means that when The Brotherhood Ransomware encrypts the files, they will be lost permanently, and inaccessible without the decryption key, which the criminals hold in their possession and will only give up after the victim pays a ransom (and even then, it is possible that they will not deliver the decryption key even if the victim makes a ransom payment). The Brotherhood Ransomware targets the user-generated data, encrypting a wide variety of file types in the attack, including numerous media files, databases, document formats, and numerous other files. The known examples of the files that threats like The Brotherhood Ransomware will target in their attacks include:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The Brotherhood Ransomware will mark the targeted files with the file extension '.ransomcrypt,' which it will be added to the targeted file name. Once The Brotherhood Ransomware has encrypted the victim's files, The Brotherhood Ransomware will replace the victim's desktop image with a desktop background containing the following text:
'Your files have been encrypted. To decrypt your file, please transfer 100 BTC
to Bitcoin Address
24fAcfdYasU975qwFGyesl45eH63cNuCZP
Otherwise, you will lose your file today at 16:30:00hrs
HACKED THE BROTHERHOOD'
Some variants of The Brotherhood Ransomware observed by PC security researchers seem to limit their attack to the Documents directory, avoiding other directories on the infected computer.
Protecting Your Data from Threats Like The Brotherhood Ransomware
The amount of 100 Bitcoin is 650,000 USD at the current exchange rate approximately, and it is very unlikely that anyone will pay this amount to recover their files. Since it is clear that the criminals have no intention of restoring the files encrypted by the attack, PC security researchers advise computer users to back up their files as a way that makes them be protected against attacks like The Brotherhood Ransomware preemptively. Having file backups, as well as security products are the two best ways to ensure that your files will be guarded against threats like The Brotherhood Ransomware. Since threats like The Brotherhood Ransomware are delivered using spam email attachments or known tactics online, such as fake software downloads or corrupted advertising, learning to spot online tactics and corrupted email attachments is a key part of protecting your data from threats like The Brotherhood Ransomware. A combination of safe security practices, good security software, and file backups is the best way to ensure that all of your data is safe.
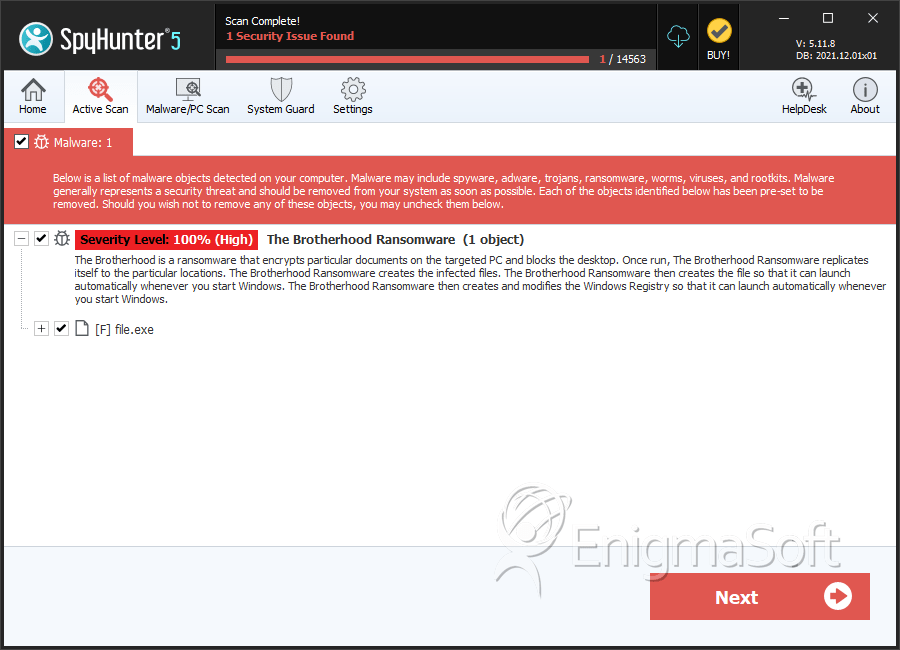
SpyHunter Detects & Remove The Brotherhood Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 23d82835c257a162f57027008bfed716 | 2 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.