Terdot
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
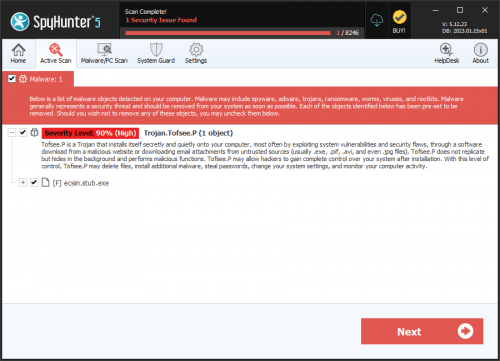
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 12,429 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 398 |
| First Seen: | September 8, 2021 |
| Last Seen: | April 18, 2026 |
| OS(es) Affected: | Windows |
Terdot is a banking Trojan that is related to Zeus, a well-known banking Trojan. Terdot is designed to collect information from its victims, including credit card information and online login information. Terdot also is designed to inject an HTML code into the websites visited on the infected computer, allowing it to get information and trick computer users into logging into fake versions of websites inadvertently and carries out other well-known tactics. One aspect of Terdot is that it targets well-known online email services, including Gmail and Yahoo. Curiously, Terdot does not target vk.com, the largest social media platform in Russia. This may indicate some espionage application or a targeted attack functionality associated with the Terdot banking Trojan.
Table of Contents
Terdot is a Highly Threatening Banking Trojan
Terdot is designed to receive automatic updates, allowing Terdot's operators and creators to update Terdot and upload new data relating to Terdot. Financial institutions and other online platforms take precautions against Trojans like Terdot, taking special steps in safeguarding accounts and credit card information. There are several ways in which this can be done, including a better monitoring of accounts for any activity that is out of the ordinary and informing customers about possible attacks, risks, and other steps that can be taken to prevent attacks like Terdot actively.
How Terdot Carries out Its Attack
Zeus is an infamous Trojan that is responsible for countless attacks on online banking platforms and other websites. After the code for the Zeus Trojan was leaked online in 2011, numerous variants of this Trojan appeared. Terdot is just one of the many Trojans that take advantage of the availability of Zeus' code to carry out attacks. PC security researchers have connected two types of attacks with Terdot; Man-in-the-Middle attacks and phishing. Both are designed to collect the victims' data, using two different approaches. It is important for online platforms to establish preventive measures to defend themselves against these attacks. It is not enough for computer users to have strong security software that is fully up-to-date; protection against threats like Terdot must be taken on both sides.
There are several techniques associated with Terdot that may not have been in the original Zeus framework. These include the use of open source tools for creating fake SSL certificates and obfuscation techniques that allow Terdot to evade some anti-virus programs. Terdot's Man-in-the-Middle attack also is quite sophisticated, filtering all of the victim's online activity in search for data that then is stored and sent to Terdot's operators. Terdot can manipulate the traffic on online email platforms and social media websites, even creating fake messages and posts that appear to be sent by the victim. Terdot is capable of evading detection and removal techniques, which makes it very difficult to remove completely.
The Terdot Attacks are in the Wild
Although there are countless ways of delivering Trojans like Terdot to the victims' computers, the bulk of Terdot infections are related to the SunDown Exploit Kit. Terdot is being spread through corrupted email messages that include a fake PDF file that installs Terdot through the use of a corrupted JavaScript. As with most banking Trojans, it is important for computer users to take special precautions when handling unsolicited email messages and attachments. This is especially true because threats like Terdot can spread through the use of phishing emails, which trick computer users by using social engineering techniques that make it seem as if the email message is coming from a legitimate source. A skilled security program also should be used.
The Return of Zeus Sphinx
The current Zeus Sphinx campaign involves the use of phishing emails. The emails contain malicious documents that appear to be information about government relief programs for the coronavirus pandemic.
Some Terdot activity was noticed last December, but the campaigns kicked into high gear during March 2020. The threat actors behind the virus appear to be taking advantage of people waiting for their government relief.
Much like with the previous campaigns, the team behind Terdot is targeting major banks across Australia, Canada, and the United States.
Hackers ask their victims to fill out a password-protected request form sent to them as a Word document. The email suggests that the recipient will receive relief payments to help them survive at home during the pandemic.
After the user downloads and accesses the document, it will request that they enable macros. If the user allows for macros, the document infects their computer by downloading and running an installer for the Sphinx banking trojan.
Researchers discovered Sphinx could patch explorer.exe and browser processes. However, the virus is unable to repatch itself again should the exploit be patched. As such, the persistence of the virus isn’t an issue. It is unlikely to persist after browsers are updated.
Terdot can download custom files designed to mimic banking websites by using Tables web-based control panels. By doing this, the virus appears more legitimate and is better able to trick users into offering up their banking information. The information and authentication codes the person enters into the fake website is sent to the attacker, who can use it for nefarious purposes.
The Tip of the Iceberg
The new Terdot campaign is just one of many virus campaigns leveraging coronavirus to trick victims and steal their sensitive information. The FBI recently warned that they spotted phishing campaigns using fake government stimulus checks to steal information from targets.
The Internet Crime Complaint Center of the FBI warns users to avoid clicking on links and opening attachments sent by unknown people. The FBI also recommends making sure that the websites you visit are legitimate by entering the link into the address bar of the browser yourself instead of clicking on a hyperlink.
One of the most important things you can do is to never offer up personal and financial information over the phone or through emails.
03.31.20 Update
Terdot, also known as Zeus Sphinx and Zloader, has been inactive for the past few years relatively. However, it appears that the panic surrounding the Coronavirus pandemic has caught the attention of its developers, and they have once again started to propagate it – this time, with the help of COVID-19 themed phishing emails.
The current campaign relies on corrupted documents that arrive as legitimate-looking email attachments. One of the common subjects used in the phishing campaign is 'COVID-19 Relief,' and the attached document goes by the same name 'COVID-19 Relief.doc.' The document is password-protected, but the password to unlock it is included in the email – this is a basic measure that cybercriminals adopt to make the job of automatic malware analysis tools more difficult.
If the document is downloaded and opened, the recipient may be asked to enable the execution of macros to view the protected content – if the prompt is accepted, the Terdot payload may be downloaded and initialized. The targets of the 'COVID-19 Relief' phishing campaign appear to be users of various banks in Australia, Canada and the United States.
Once active, the Terdot Banking Trojan will use its classic technique to collect login credentials from its victims – it will alter the online banking portals they visit and insert fake fields that are used to collect information, as well as bypass two-factor authentication.
Analysis Report
General information
| Family Name: | Trojan.Kryptik.VCNB |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
daa69f1ffb8c9da7a993d5f93440bfdc
SHA1:
46e4877890c27574246e24037c736feb47b4f7e9
SHA256:
393BE3FCD47AD61B34A24E2C6A0A8983603458D4E6A19590933E66C52EFE5EE7
File Size:
1.22 MB, 1224704 bytes
|
|
MD5:
b6c193ef5b6eff553048961831c1f340
SHA1:
bf523ce611214ecc13a1a0fccaeacf3bb21d2fea
SHA256:
0E5ABF7D1A0B9CA78A29807A448D03BCED7FFE41F19CB6E39CC2CAE5E4618857
File Size:
548.86 KB, 548864 bytes
|
|
MD5:
9cad9bf9626013968d626deb250c94ec
SHA1:
f166f5f14b2ac3a37ad706b58a742f196eb8d733
SHA256:
662ED672FE4AA6BA73E81AA844F9524F451AC4ECC662EF1AFE043998C95AD38B
File Size:
176.13 KB, 176128 bytes
|
|
MD5:
4e5f770981dc1f690b79475386b30f94
SHA1:
c8fb17745ec142e9b46982820b191b612cfe1ac7
SHA256:
FB2002E4241943760275639CC40C7475FB16C0B8497F573B0B200298026455E7
File Size:
327.68 KB, 327680 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have resources
- File doesn't have security information
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.File Traits
- 2+ executable sections
- No Version Info
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 976 |
|---|---|
| Potentially Malicious Blocks: | 14 |
| Whitelisted Blocks: | 930 |
| Unknown Blocks: | 32 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Cerber.AF
- Kryptik.VCNB
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\downloads\error.txt | Generic Write,Read Attributes |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\software\wow6432node\microsoft\directdraw\mostrecentapplication::name | 46e4877890c27574246e24037c736feb47b4f7e9_0001224704 | RegNtPreCreateKey |
| HKLM\software\wow6432node\microsoft\directdraw\mostrecentapplication::id | 誛桏 | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Other Suspicious |
|
| Anti Debug |
|