Teeny Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 5 |
| First Seen: | February 11, 2019 |
| Last Seen: | September 17, 2019 |
| OS(es) Affected: | Windows |
The Teeny Ransomware is an encryption ransomware Trojan that was first observed on January 31, 2019. The Teeny Ransomware is mainly designed to target devices located in Turkey and takes advantage of poor security protection. It is crucial to protect your devices from the Teeny Ransomware attacks, which can be quite destructive and make data permanently inaccessible.
Table of Contents
The Damage Caused by the Teeny Ransomware is not Teeny at All
Most encryption ransomware Trojans target the user-generated files specifically, using a strong encryption algorithm to encrypt the files with extensions such as the following:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi.
The Teeny Ransomware uses a different approach that is much more destructive. The Teeny Ransomware overwrites the Master Boot Record of the affected computer's memory devices rather than encrypting individual files, and then restarts the computer. This makes the entire computer unusable since the operating system will not start up. The Teeny Ransomware does not make a backup copy of the original Master Boot Record, making the recovery of a Teeny Ransomware attack impossible completely. When the infected computer starts up, the following message (written in Turkish) appears on the victim's screen, written in red over a black background:
'dosyalariniz guclu bir algoritma ile sifrelendi.
key olmadan dosyalarinizi acmaya calimsmak diskteki tum verilerin yok olmasina ve zaman kaybina sebep olabilir.
dosyalarinizi kartmak icin altta buluman talimari izleyin.
luften talimari takip eidn.
1. altta bulunan bitcoin hesabina 200$ lik bir odeme gerceklestirin
btc req : [random characters]
2. odemeyi gerceklestirdikten sonra odeme yaptiginiz btc walletin id sini ve altta buluman id ile tarafimize mail atin.
e-posta: teeny@posteo.net
id: [random characters]
3. tarafiniza gonderilen keyi giriniz.
key: [input prompt]'
Below is a translation into English of the above ransom demand:
'Your files are encrypted with a powerful algorithm.
Trying to open your files without a key can result in the loss of all data on the disk and loss of time.
follow the instructions to find your files at the bottom.
Follow the instructions.
1. Perform a $ 200 payment to the underlying bitcoin account
btc req: [random characters]
After you have done the 2nd btc wallet id and the id at the bottom you want to mail us.
email: teeny@posteo.net
id: [random characters]
3. Enter the key that was sent to your side.
key: [input prompt]'
You will not be capable of recovering the data that has been damaged by the Teeny Ransomware attack, despite what the message says. Therefore, computer users should refrain from paying the $200 Bitcoin ransom that the Teeny Ransomware demands in its attack since it will be just a waste of money.
Protecting Your Data from Threats Like the Teeny Ransomware
The best way to keep your data free from attacks like the Teeny Ransomware is to have backup copies of all of your data. These copies should be stored on the cloud or an external memory device, away from the reach of threats like the Teeny Ransomware. It is also recommended to have a dedicated backup service, to minimize the data that is lost in an attack like the Teeny Ransomware. Having file backups ensures that the victims can recover their data after an attack of this type, removing any need to contact the criminals or consider paying any ransom.
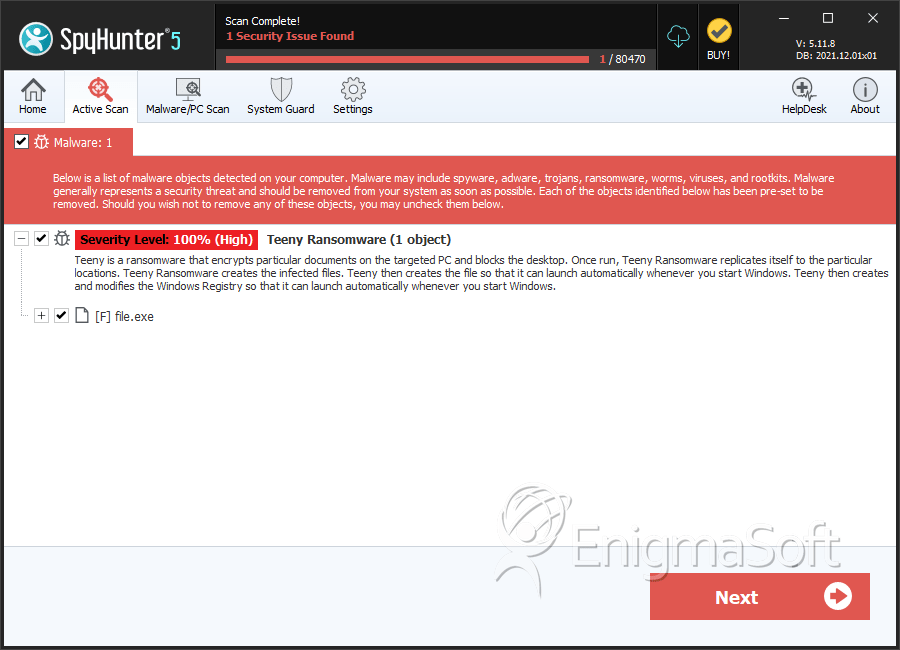
SpyHunter Detects & Remove Teeny Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 7080eceaceef66c032ca0c9bc66b7c3c | 2 |

