Striked Ransomware
The Striked Ransomware is an encryption ransomware Trojan that receives its name because of the peculiar language in its ransom note. The Striked Ransomware's ransom note includes the heading 'YOUR FILES ARE STRIKED!,' an unusual way of referring to the files that have been encrypted or deleted. The Striked Ransomware infection itself is not unique or different from other ransomware Trojans in other respects particularly.
Table of Contents
The Truth Behind the Striked Ransomware’s Name
The Striked Ransomware uses a strong encryption algorithm to make the victims' files inaccessible. In its attack, the Striked Ransomware will use the AES 256 encryption to make the unrecoverable files. The Striked Ransomware will then instruct the victims to contact the email raiden@mortalkombat.top to receive information on how to recover the affected files. There are several ways in which the Striked Ransomware may be delivered. However, the main delivery method associated with the Striked Ransomware involves taking advantage of weak remote desktop configurations and servers with unprotected Web access panels. Weak passwords and other poorly configured security settings allow third parties to access the victim's computer, install the Striked Ransomware, and encrypt the infected computer's data. The Striked Ransomware will change the affected files' file extension and write an additional 36 bytes to each affected file, apart from the use of strong encryption to make the files inaccessible. These additional small portions of data may be part of an effort to prevent PC security researchers from creating a decryption program to help computer users affected by the attack.
The Striked Ransomware’s Ransom Note and Demands
The victims will recognize the Striked Ransomware because it uses a large, colorful ransom notification with its catch phrase mentioned above. The Striked Ransomware also will replace the infected computer's desktop image with its ransom note and drop an HTML file on the infected computer's desktop. This file, named 'README_DECRYPT.html,' will contain the Striked Ransomware's ransom note. The Striked Ransomware ransom note and the new desktop image is quite colorful, including colors like yellow, red and green. The Striked Ransomware's ransom note will be opened on the infected computer's Internet browser and contain the following message for the victim:
'YOUR FILES ARE STRIKED!
-=ALL OF YOUR FILES ARE ENCRYPTED!=-
Your personal identifier: [10 RANDOM DIGITS]
Your documents, photos, databases, save games and other important data were encrypted.
For a data recovery requires a decryptor.
To decrypt your files send an email to raiden@mortalkombat.top
In the reply letter you will receive a program for decryption.
After starting the decryption program, all your files will be restored.
!!! Attention !!!!!! Attention !!!!!! Attention !!!
*** Do not attempt to uninstall the program or run antivirus software
*** Attempts to decrypt files by themselves will result in the loss of your data'
The files encrypted by the Striked Ransomware attack will have a new file extension: '#raiden@mortalkombat.top#id#0123456789.' added to the end of each affected file's name. Unfortunately, the files encrypted by the Striked Ransomware attack are not recoverable without access to the decryption key, which the extortionists hold in their possession.
Dealing with the Striked Ransomware Infection
PC security analysts advise computer users to refrain from paying the ransom that the Striked Ransomware demands. Instead, they should take preventive measures to ensure that their data can be recovered in case of an attack. Having file backups or disk images is the best protection against attacks like the Striked Ransomware. If PC users can restore their files from a backup copy, then the people responsible for the Striked Ransomware attack lose any power over the victims that would allow them to demand a ransom payment. Apart from having file backups, they should block the common infection vectors associated with the Striked Ransomware. Securing all remote desktop connections, Web access and other forms of remote access can go a long way towards preventing the Striked Ransomware infections.
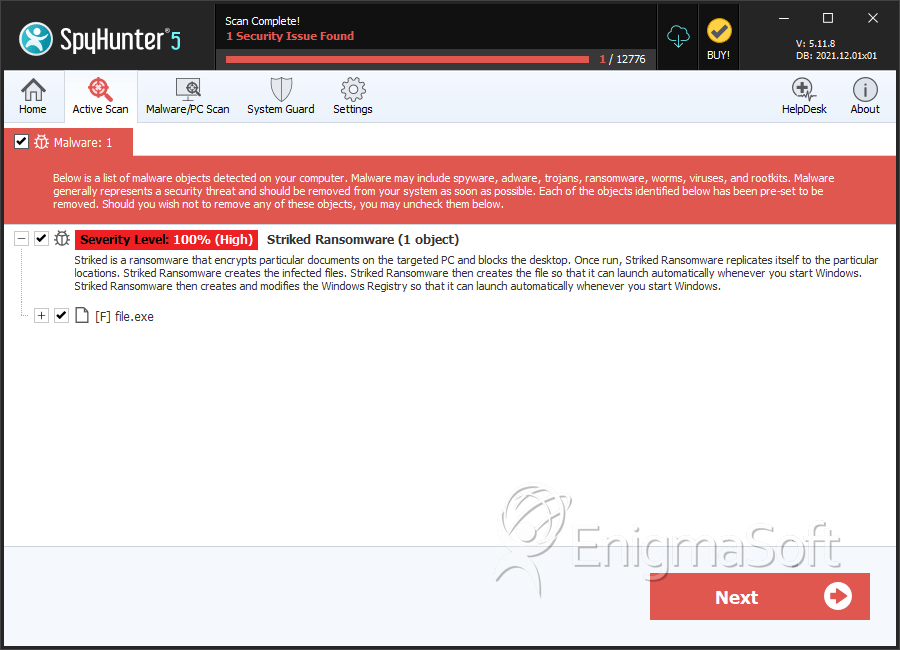
SpyHunter Detects & Remove Striked Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 96aae6a052f24089d13b1460577fc6c9 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.